Ransomware attack stops Argentinian border crossing for four hours
A Netwalker ransomware attack has been occurred in Argentina’s official immigration agency, Dirección Nacional de Migracione, which temporarily stopped border crossing into and out of the country. While the attacks of file-encrypting viruses have been common in cities and local agencies, this might be first known attack against a centralized agency that has disrupted a country’s operations.
As per a criminal complaint published by Argentina’s cyber crime agency, Unidad Fiscal Especializada en Ciberdelincuencia, the government came to know about the lethal crypto-virus attack after receiving a number of tech support calls from checkpoints at approx. 7 AM on August 27th.
“Being approximately 7 a.m. of the day indicated in the paragraph above, the Directorate of Technology and Communications under the Directorate General Information Systems and Technologies of this Organization received numerous calls from various checkpoints requesting technical support.”
“This realized that it was not an ordinary situation, so it was evaluated the situation of the infrastructure of the Central Data Center and Servers Distributed, noting activity of a virus that had affected the systems MS Windows based files (ADAD SYSVOL and SYSTEM CENTER DPM mainly) and Microsoft Office files (Word, Excel, etc.) existing in users’ jobs and shared folders,” a translation of the complaint stated.
To prevent the virus from infecting more devices, the computer networks used by the immigration offices and control posts were shut down. According to Argentinian news site Infobae, this led to a temporary suspension of border crossings for four hours while the servers were brought back online.
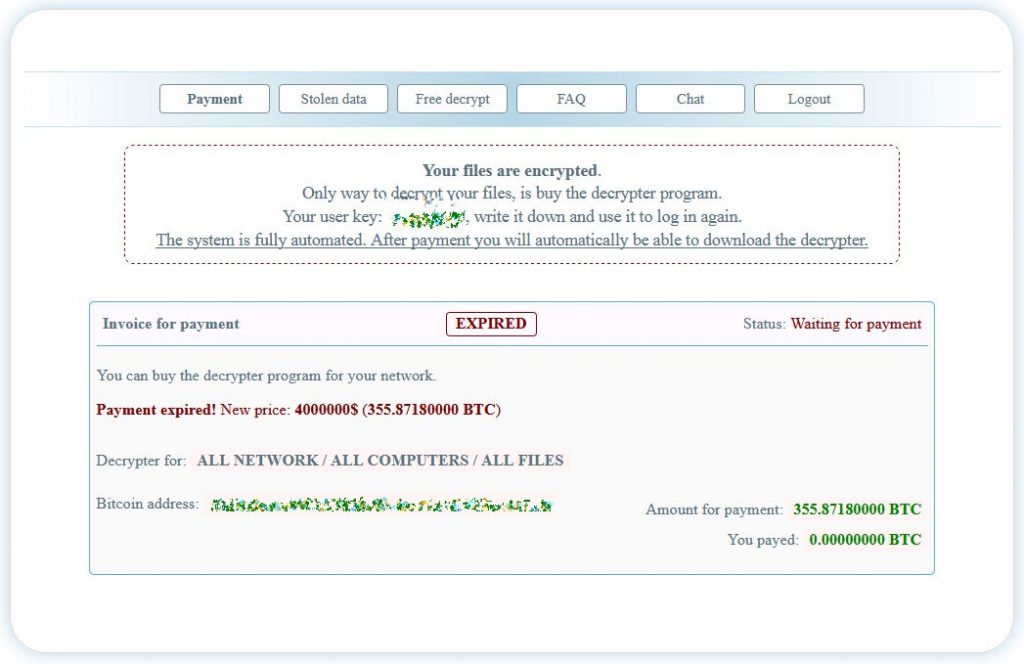
When the Netwalker ransomware performed the attack, a ransom note dropped on infected devices informing victims regarding the attack. These notes contain links to a dark web payment site that involves information on how to purchase a decryptor, the ransom amount, and information about any unencrypted files that were stolen during the attack.
From a Netwalker Tor payment page, it has been noticed that the ransomware actors initially demanded a $2 million ransom. After seven days passed, the ransom increased to $4 million, or approximately 355 bitcoins.





