MS Sysmon Now Detects Malware Tampering Processes
The tech giant company named Microsoft has reportedly released Sysmon 1.3 and added a new feature in it. As per the reports, the feature can detect if a process has been tampered using process hollowing or process herpaderping techniques.
In order to prevent detection by security applications, malware developers use to inject malicious code into Windows legitimate process. Through this tactics, the malware is allowed to execute, but the process appears as Windows running process in the background in Task Manager.
Speaking about Process Hollowing, it’s a technique under which a malware launches a legitimate process that appears like a suspended one, and replaces the legitimate code with its own malicious ones. And the code then runs in background with whatever the permissions are assigned to original process.
Where as the Process Herpaderping is more advance method under which the malware alters its image on the infected disk and appears like a legit application, following malware is loaded. When the security app scans files on disk, it notice no harmful file while the malicious code keeps running inside system.
In addition to these, many of the malware identities make use of process tampering technique to prevent its detection. Some of the malware are Mailto/defray777 ransomware, TrackBot, and BazarBackdoor.
How to enable process tampering in Sysmon v1.3
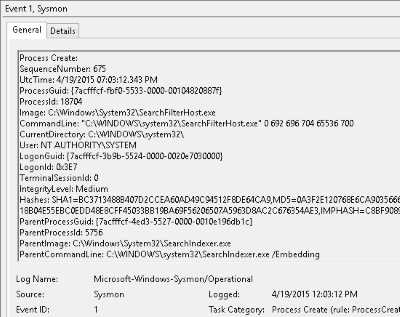
If you are one of those who are still not aware of Sysmon or System Monitor app in Windows, then you should known it’s a Sysinternals tool which is designed to monitor system for malicious processes. In addition, it also logs those processes in Windows event log.
One can download the application from Sysinternal’s official page or http://live.sysinternals.com/sysmon.exe.
To enable the process tampering detection feature, the PC users or administrators need to add the ‘Process Tampering’ configuration option to a configuration file. Keep in mind that Sysmon just monitors basic events such as process creation, and file time changes without a configuration file.
A new directive has also been added to Sysmon 4.50 schema that can be viewed by running the sysmon -S command.
Once can use the following configuration file for a very basic setup which will enable process tampering detection.
<Sysmon schemaversion="4.50"> <EventFiltering> <RuleGroup name="" groupRelation="or"> <ProcessTampering onmatch="exclude"> </ProcessTampering> </RuleGroup> </EventFiltering> </Sysmon>
To initiate the Sysmon and instruct it to use the above configuration file, the users should execute the sysmon -i and pass the configuration file name. For an instance type “sysmon -i sysmon.conf”, where sysmon.conf is the name of config file.
Once the Sysmon starts, will install its driver and initiate collecting data silently in the background.
All Sysmon events will be logged to ‘Applications and Services Logs/Microsoft/Windows/Sysmon/Operational’ in the Event Viewer.
If the Process Tampering feature is enabled, whenever the process hollowing or process herpadering is detected, Sysmon will generate a ‘Event 25 – Process Tampering’ entry in the Event Viewer.
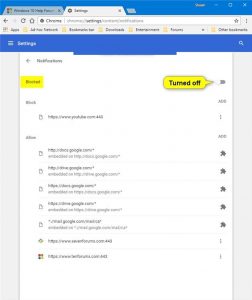
Based on some tests, the feature detected various harmless executables related to Chrome, Opera, Firefox, Fiddler, MS Edhe, and various Setup programs.
However, the feature unfortunately triggered no events in case of the latest TrickBot and BazarLoader.