How to remove DominantCommand from Mac
Complete tips to delete DominantCommand
DominantCommand is a rogue piece of software that promotes a fake search engine (by modifying browser settings). Also, it delivers various intrusive advertisements. Therefore, this app can be said to be an adware as well as browser hijacker. It is important to mention here that the apps of this kind can be designed to collect sensitive information. Adware and Browser hijackers are together called potentially unwanted applications because users rarely download and install them with purpose.
Browser hijackers alter the settings of all browsers installed on the systems compromised. They are designed to promote certain fake search engines. The promoted URLs replace the default homepage, new tab pages and search engine options of the infected web browsers. These changes made it mandate to the victims to surf the session using the fake search engines. These are considered as fake because they do not bear potential to display their own search results. They display results generated by legit web searchers like Google.com, Bing.com or Search.yahoo.com.
Adware-type of applications aims to generate revenue by promoting third parties’ pages through banners, pop-ups, surveys, coupons or other advertisements. These ads may open those pages that cause downloads or even installations of unwanted apps or even malware just after being clicked. When your system is infected with DominantCommand, you will encounter the effect of both of adware and browser hijacker functions. Additionally, it is common that PUAs track users’ browsing session. So, the PUA’s authors can collect the browsing based data like:
- Search queries,
- Viewed pages,
- URLs visited,
- ISP,
- Geo-locations,
- IPs and etc
These data are typically used in designing customized ads. However, the PUAs might share these details to third parties, potent crooks for gaining profit. These people make the use of these data in various illicit activities that may cost on privacy, cause identity exposure and many more severe issues. To prevent all such risks, immediately remove DominantCommand and all associated applications running on the system background. Check the post below for the complete tips regarding the removal process. There, you will find both manual as well as automatic guide in step-by-step manner.
How did DominantCommand infiltrate my computer?
In some cases, users download/ install unwanted applications like DominantCommand through deceptive advertisements. These ads are designed to run certain scripts to cause stealthy downloads/ installations. Although, more often, users cause the unwanted downloads during the download/ installation of other programs. More precisely, the PUAs are often distributed bundled with regular software as additional offers. Users won’t decline these offers available checkboxes or via Custom/Advanced settings of the downloaders/ installers have. Thus, they ultimately agree to the download/ installation of unwanted applications.
How to prevent PUAs intrusion?
Files and programs should be downloaded from official websites and direct links. Other sources can be used to distribute unwanted applications. During the download/ installation, use Custom/Advanced option and manually opt out all additionally attached apps and decline all offers. Also, do not click on any ads appear on any questionable pages – they can open other pages of this kind or execute certain scripts designed to download/ install unwanted software. Since you have DominantCommand already installed on the system, focus on its removal right now. Below, you will find the complete guide on how the removal process should be done.
Special Offer (For Macintosh)
DominantCommand can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful antimalware scanner to help you getting rid of this virus
Remove Files and Folders Related to DominantCommand
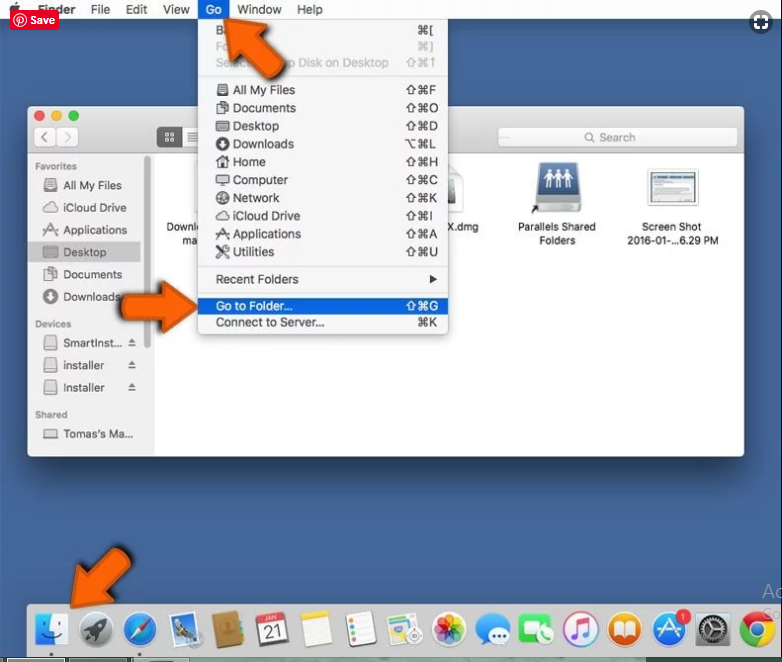
Open the “Menu” bar and click the “Finder” icon. Select “Go” and click on “Go to Folder…”
Step 1: Search the suspicious and doubtful malware generated files in /Library/LaunchAgents folder
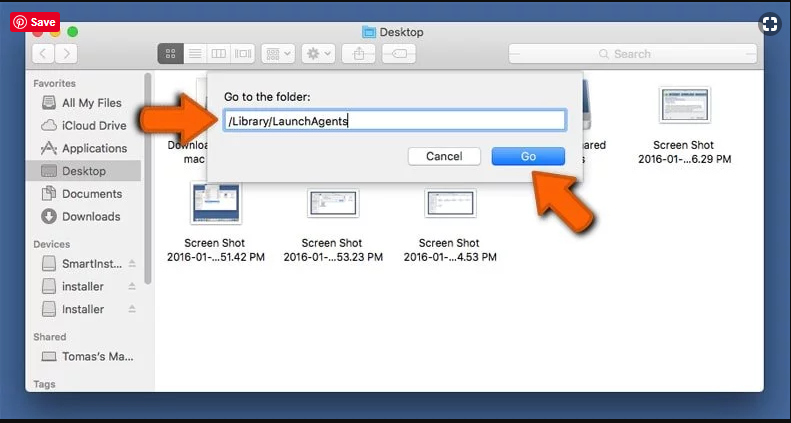
Type /Library/LaunchAgents in the “Go to Folder” option
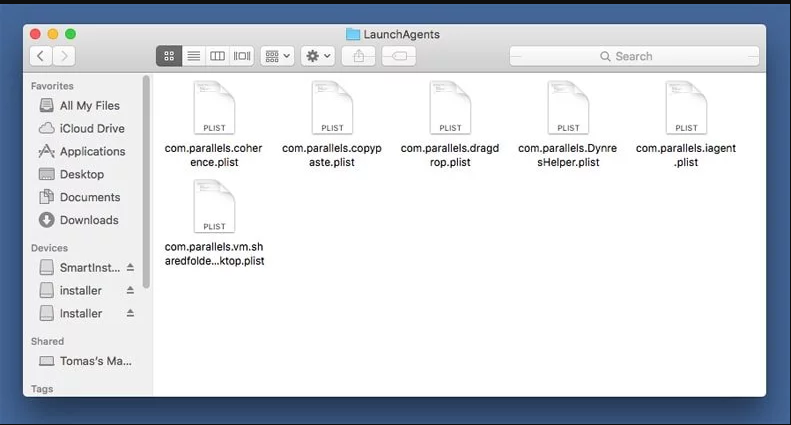
In the “Launch Agent” folder, search for all the files that you have recently downloaded and move them to “Trash”. Few of the examples of files created by browser-hijacker or adware are as follow, “myppes.download.plist”, “mykotlerino.Itvbit.plist”, installmac.AppRemoval.plist”, and “kuklorest.update.plist” and so on.
Step 2: Detect and remove the files generated by the adware in “/Library/Application” Support folder
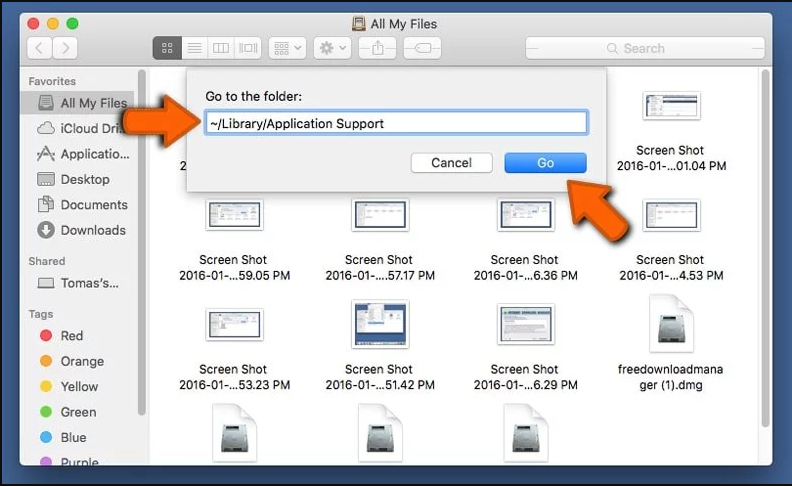
In the “Go to Folder..bar”, type “/Library/Application Support”
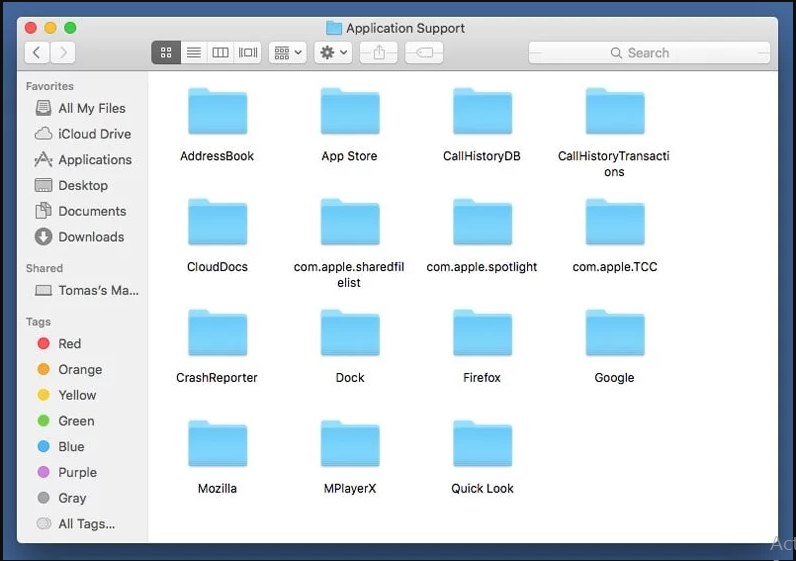
Search for any suspicious newly added folders in “Application Support” folder. If you detect any one of these like “NicePlayer” or “MPlayerX” then send them to “Trash” folder.
Step 3: Look for the files generated by malware in /Library/LaunchAgent Folder:
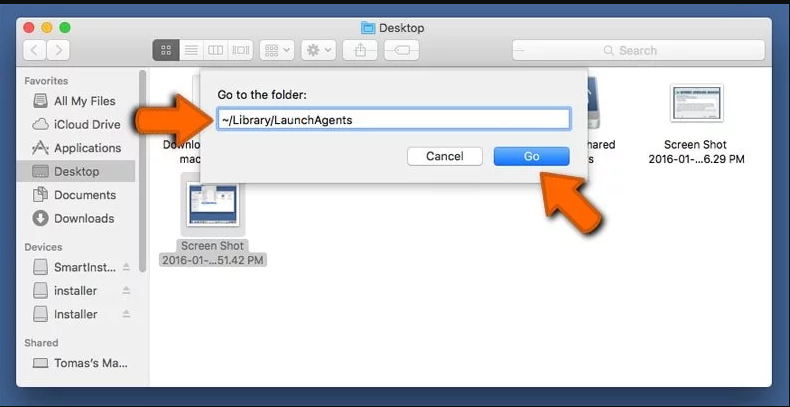
Go to Folder bar and type /Library/LaunchAgents
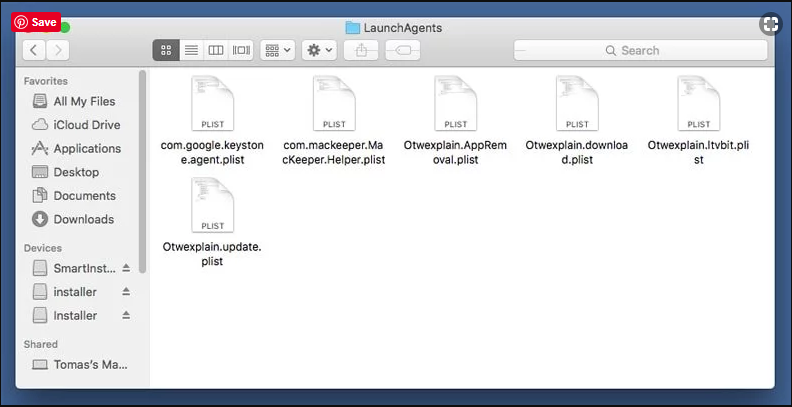
You are in the “LaunchAgents” folder. Here, you have to search for all the newly added files and move them to “Trash” if you find them suspicious. Some of the examples of suspicious files generated by malware are “myppes.download.plist”, “installmac.AppRemoved.plist”, “kuklorest.update.plist”, “mykotlerino.ltvbit.plist” and so on.
Step4: Go to /Library/LaunchDaemons Folder and search for the files created by malware
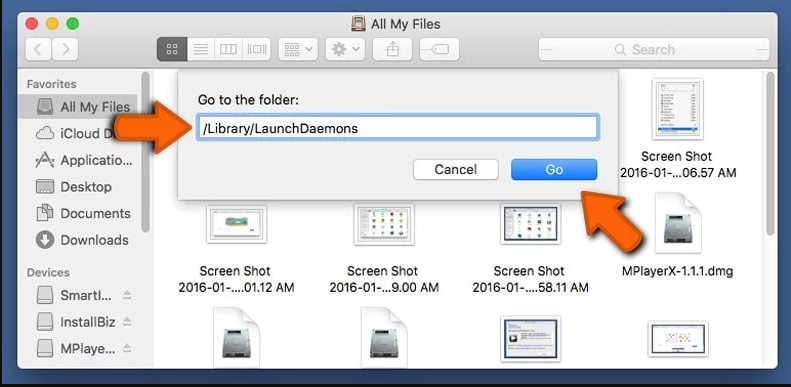
Type /Library/LaunchDaemons in the “Go To Folder” option
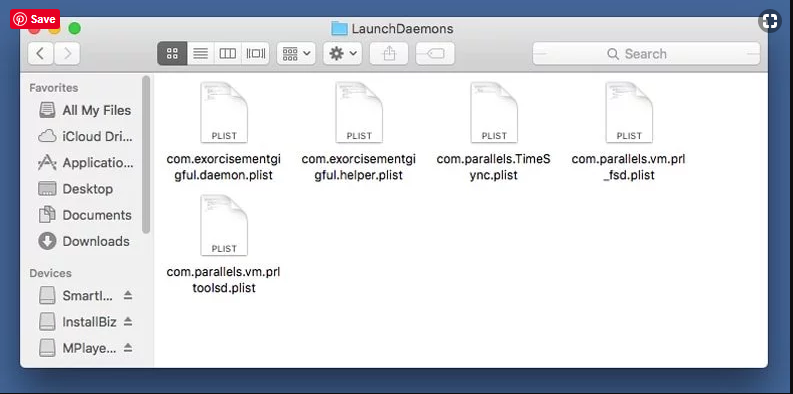
In the newly opened “LaunchDaemons” folder, search for any recently added suspicious files and move them to “Trash”. Examples of some of the suspicious files are “com.kuklorest.net-preferences.plist”, “com.avickUpd.plist”, “com.myppes.net-preference.plist”, “com.aoudad.net-preferences.plist” and so on.
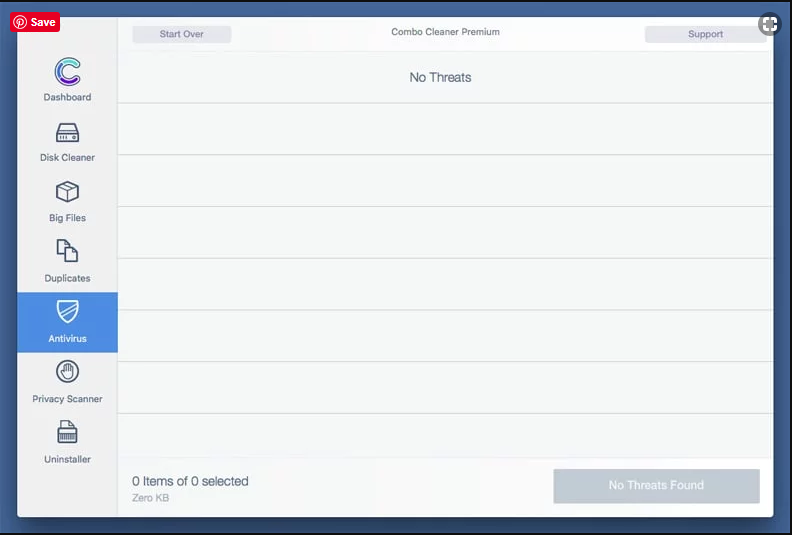
Step 5: Use Combo Cleaner Anti-Malware and Scan your Mac PC
The malware infections could be removed from the Mac PC if you execute all the steps mentioned above in the correct way. However, it is always advised to be sure that your PC is not infected. It is suggested to scan the work-station with “Combo Cleaner Anti-virus”.
Special Offer (For Macintosh)
DominantCommand can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful antimalware scanner to help you getting rid of this virus
Once the file gets downloaded, double click on combocleaner.dmg installer in the newly opened window. Next is to open the “Launchpad” and press on “Combo Cleaner” icon. It is advised to wait until “Combo Cleaner” updates the latest definition for malware detection. Click on “Start Combo Scan” button.
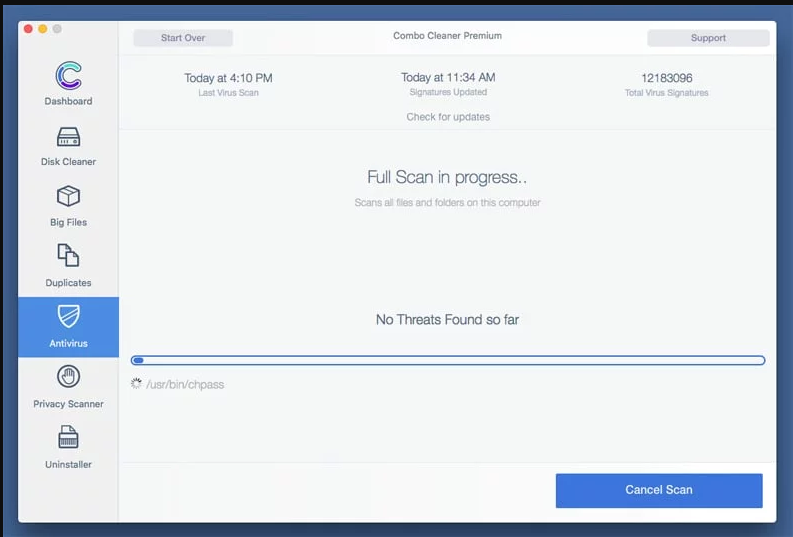
A depth scan of your Mac PC will be executed in order to detect malware. If the Anti-virus scan report says “no threat found” then you can continue with guide further. On the other hand, it is recommended to delete the detected malware infection before continuing.
Now the files and folders created by the adware is removed, you have to remove the rogue extensions from the browsers.
Remove DominantCommand from Internet Browsers
Delete Doubtful and Malicious Extension from Safari
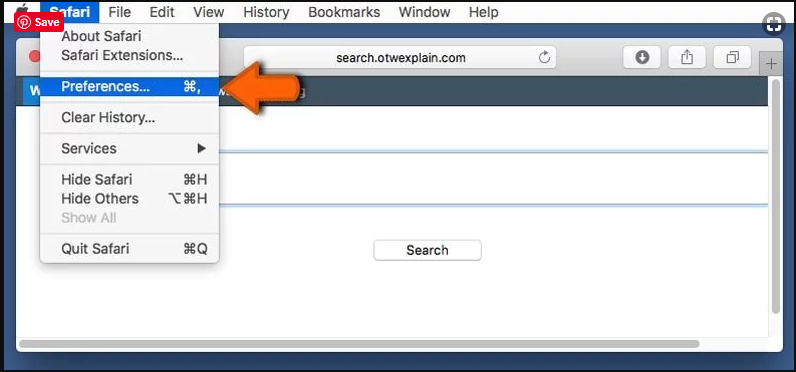
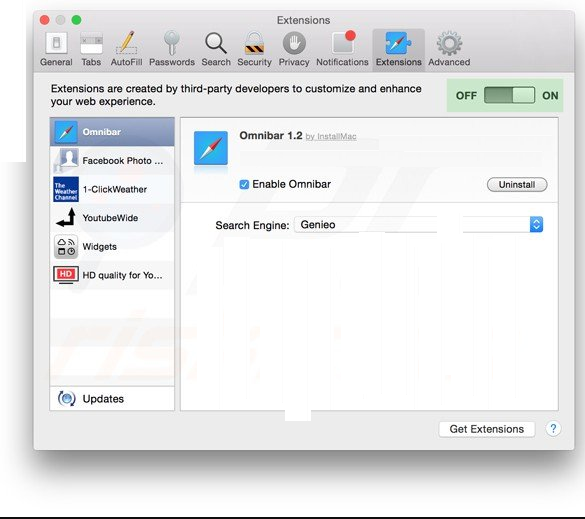
Go to “Menu Bar” and open “Safari” browser. Select “Safari” and then “Preferences”
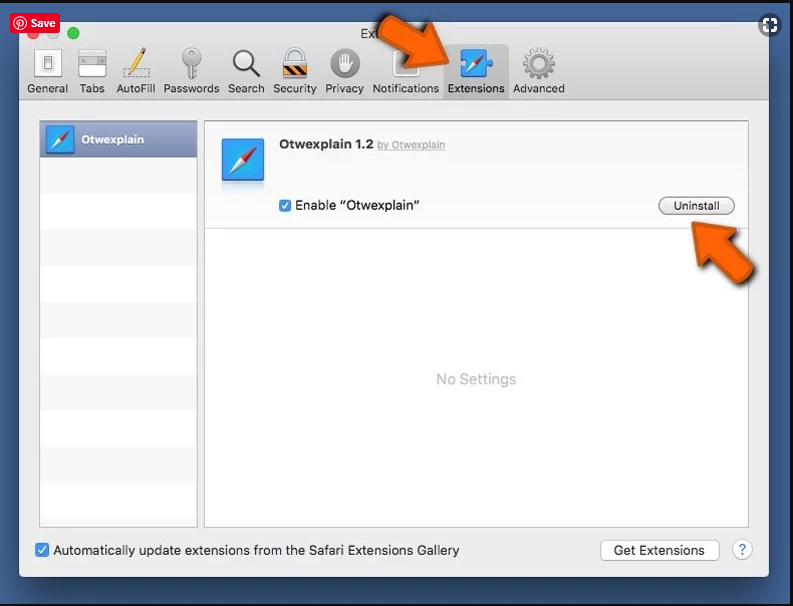
In the opened “preferences” window, select “Extensions” that you have recently installed. All such extensions should be detected and click the “Uninstall” button next to it. If you are doubtful then you can remove all the extensions from “Safari” browser as none of them are important for smooth functionality of the browser.
In case if you continue facing unwanted webpage redirections or aggressive advertisements bombarding, you can reset the “Safari” browser.
“Reset Safari”
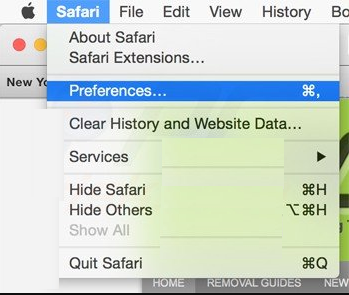
Open the Safari menu and choose “preferences…” from the drop-down menu.
Go to the “Extension” tab and set the extension slider to “Off” position. This disables all the installed extensions in the Safari browser
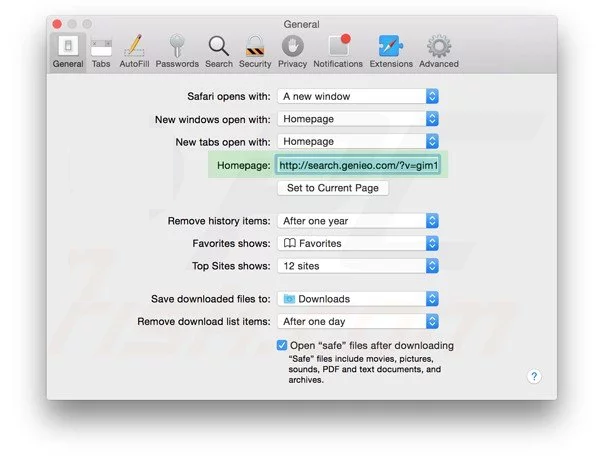
Next step is to check the homepage. Go to “Preferences…” option and choose “General” tab. Change the homepage to your preferred URL.
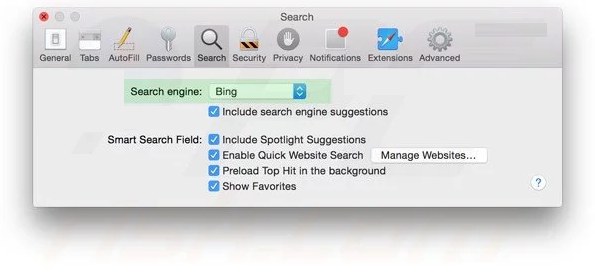
Also check the default search-engine provider settings. Go to “Preferences…” window and select the “Search” tab and select the search-engine provider that you want such as “Google”.
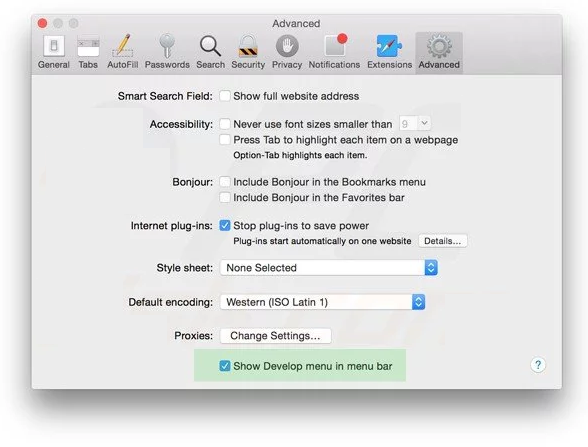
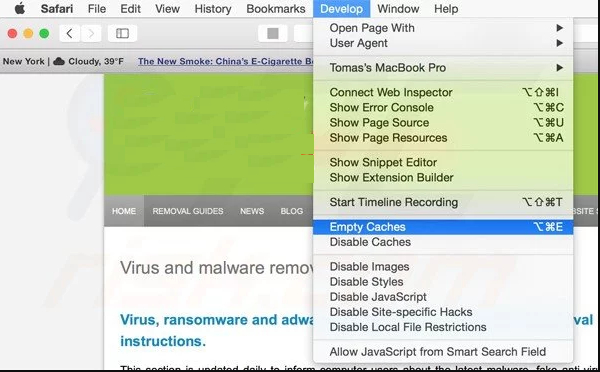
Next is to clear the Safari browser Cache- Go to “Preferences…” window and select “Advanced” tab and click on “Show develop menu in the menu bar.“
Go to “Develop” menu and select “Empty Caches”.
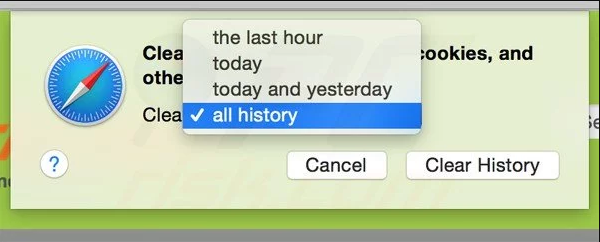
Remove website data and browsing history. Go to “Safari” menu and select “Clear History and Website Data”. Choose “all history” and then click on “Clear History”.
Remove Unwanted and Malicious Plug-ins from Mozilla Firefox
Delete DominantCommand add-ons from Mozilla Firefox
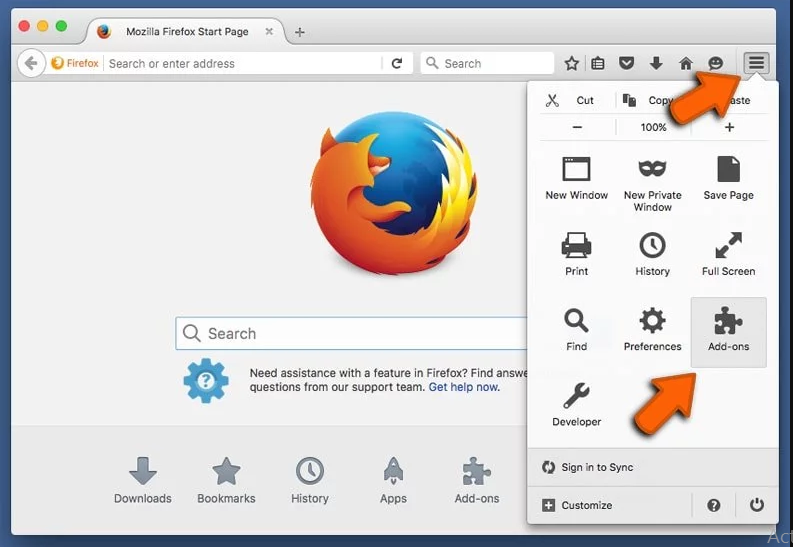
Open the Firefox Mozilla browser. Click on the “Open Menu” present in the top right corner of the screen. From the newly opened menu, choose “Add-ons”.
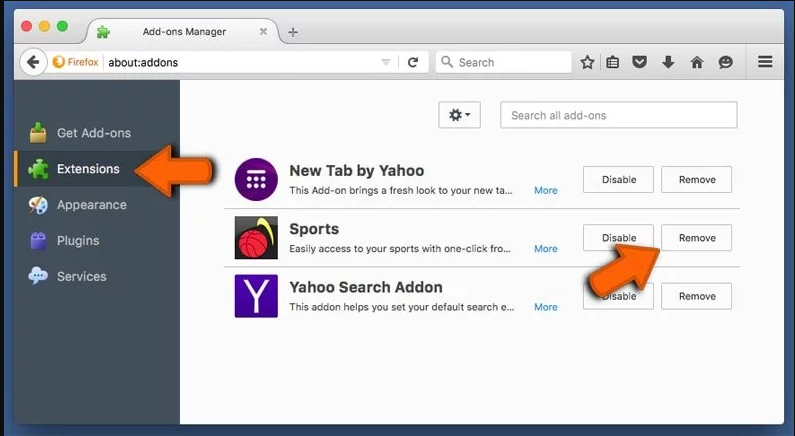
Go to “Extension” option and detect all the latest installed add-ons. Select each of the suspicious add-ons and click on “Remove” button next to them.
In case if you want to “reset” the Mozilla Firefox browser then follow the steps that has been mentioned below.
Reset Mozilla Firefox Settings
Open the Firefox Mozilla browser and click on “Firefox” button situated at the top left corner of the screen.

In the new menu, go to “Help” sub-menu and choose “Troubleshooting Information”
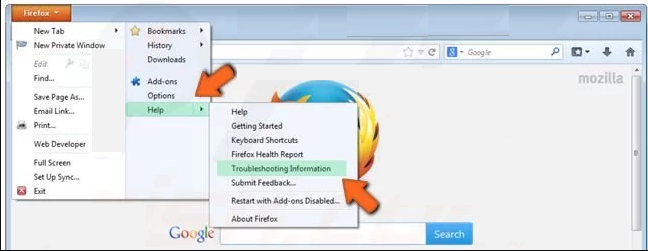
In the “Troubleshooting Information” page, click on “Reset Firefox” button.
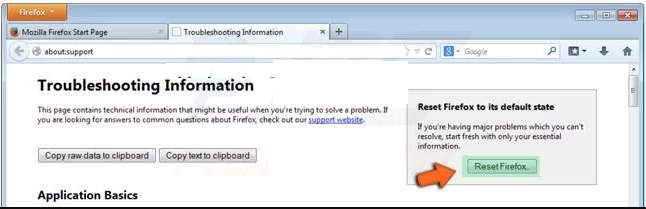
Confirm that you want to reset the Mozilla Firefox settings to default by pressing on “Reset Firefox” option
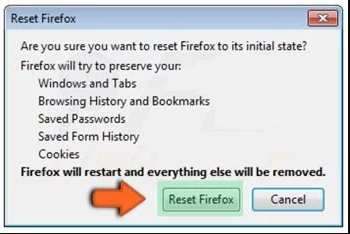
The browser will get restarted and the settings changes to factory default
Delete Unwanted and Malicious Extensions from Google Chrome
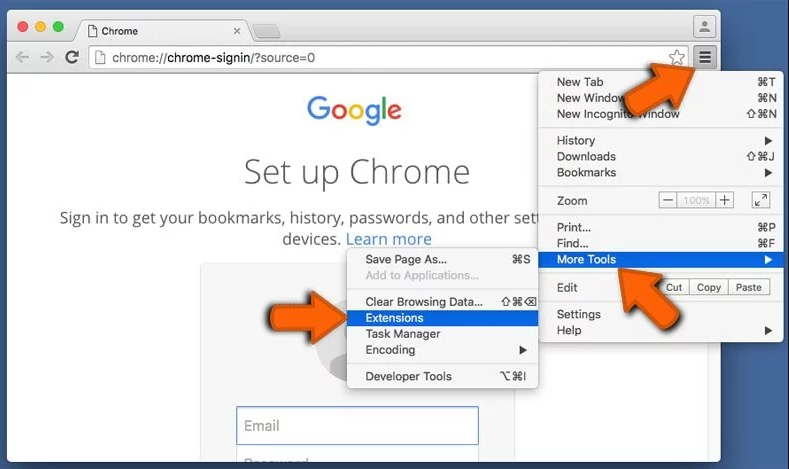
Open the chrome browser and click on “Chrome menu”. From the drop down option, choose “More Tools” and then “Extensions”.
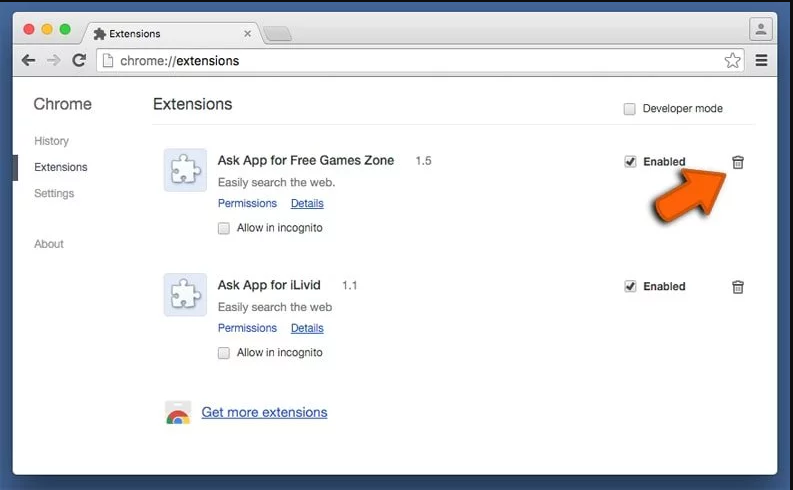
In the “Extensions” option, search for all the recently installed add-ons and extensions. Select them and choose “Trash” button. Any third-party extension is not important for the smooth functionality of the browser.
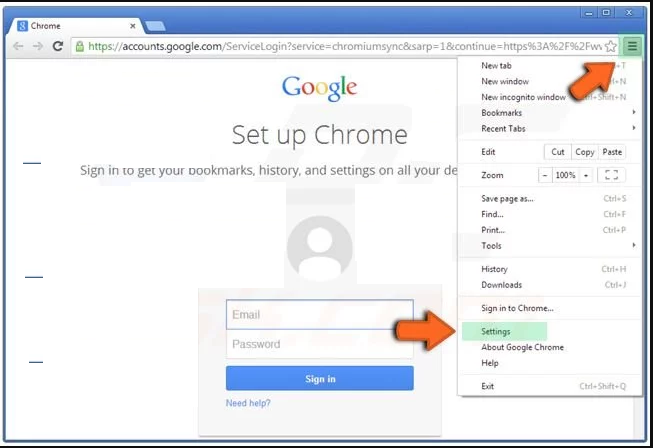
Reset Google Chrome Settings
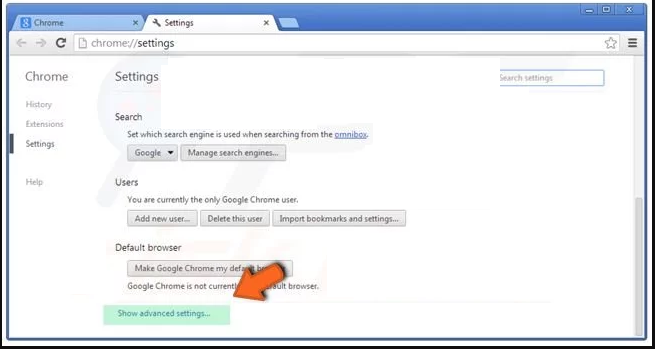
Open the browser and click on three line bar at the top right side corner of the window.
Go to the bottom of the newly opened window and select “Show advanced settings”.
In the newly opened window, scroll down to the bottom and choose “Reset browser settings”
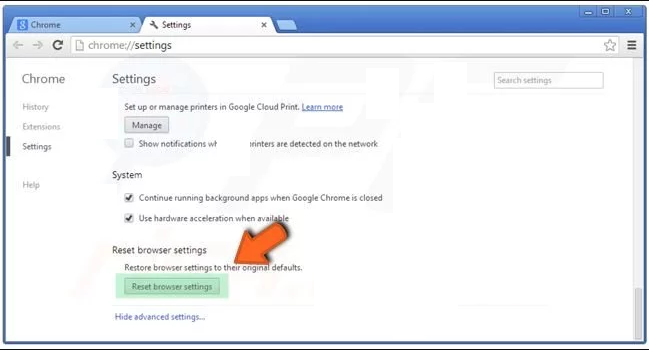
Click on the “Reset” button on the opened “Reset browser settings” window
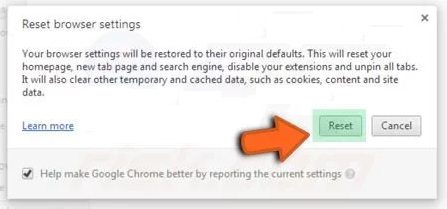
Restart the browser and the changes you get will be applied
The above mentioned manual process should be executed as it is mentioned. It is a cumbersome process and requires a lot of technical expertise. And hence it is advised for technical experts only. To be sure that your PC is free from malware, it is better that you scan the work-station with a powerful anti-malware tool. The automatic malware removal application is preferred because it doesn’t requires any additional technical skills and expertise.
Special Offer (For Macintosh)
DominantCommand can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful antimalware scanner to help you getting rid of this virus
Download the application and execute it on the PC to begin the depth scanning. Once the scanning gets completed, it shows the list of all the files related to DominantCommand. You can select such harmful files and folders and remove them immediately.