Trekdeals.com Review: Unveiling the Illusion of Authenticity Online
Trekdeals.com, presenting itself as a discount platform, is deceptive. While it may look like a warehouse clearance marketplace, it’s a trick to appear genuine. Unfortunately, ordering from this site often results in receiving nothing or low-quality, fake items.
Examining Trekdeals.com reveals red flags indicating deception. Unfair advertising, unrealistically low prices, and the absence of customer support and reviews are clear signs of potential fraud. Despite appearing as a discount or liquidation store, these indicators collectively raise concerns about the site’s legitimacy.
Buying from websites like Trekdeals.com often leads to disappointment, with three common scam outcomes. First, you might receive the wrong items – cheats send random things to mimic a legitimate trade while cutting costs. For instance, a worn t-shirt instead of a new one or a scratched dish instead of a set.
Second, you might get counterfeit goods. While you get something, it’s usually an inferior version, especially for popular brands. The details about authenticity might be buried deep in the item description, often overlooked by users, especially when purchasing small items like baubles or electronics.
The third scenario is the worst – receiving absolutely nothing. Scammers take your money, promise delivery, and then disappear. As scam websites are short-lived, they don’t bother pretending to be legitimate. Falling for such scams means losing money without a trace of the promised goods. Be cautious, check thoroughly before purchasing, and stay away from sites like Trekdeals.com to avoid these disappointing outcomes.
How does the Trekdeals.com scam operate?

Trekdeals.com follows a straightforward three-step approach commonly seen in scams. Firstly, it attracts attention by bombarding online platforms like Facebook, YouTube, Instagram, and TikTok with massive promotions. Ads promise unbelievable deals during major events, sometimes posing as liquidation stock resellers from bankrupt retail companies.
Once users visit the website, the next stage involves coaxing them into making purchases. The scammers deploy mind-boggling deals, additional discount codes, and flashy “Order Now” buttons everywhere. Exploiting the allure of these offers, unsuspecting individuals proceed to pay for their orders.
Payments take an unusual route. Instead of conventional options like MasterCard/Visa or PayPal, scammers prefer direct bank transfers, Venmo, or CashApp. These alternatives lack refund policies, even if users can prove the transaction went to scammers. The ‘no refunds’ policy, agreed upon during registration, leaves victims without recourse.
In the final stage, scammers vanish when they’ve accumulated enough money or faced sufficient complaints. Typically occurring within two to three weeks of the site’s activity, fraudsters disappear once awareness about their deception spreads. As more people catch on, the money stops flowing, prompting scammers to move on. Reporting the scam to the hosting service facilitates a swift takedown of the domain.
In essence, Trekdeals.com’s scam involves luring users with enticing deals, convincing them to make unconventional payments, and disappearing once they’ve amassed enough funds or drawn too much attention.
What makes Trekdeals.com deceptive or fraudulent?

Learn to identify fraudulent websites without risking your money. Scammers often neglect creating convincing disguises, making the same red flags evident across various sites. By staying alert to these consistent indicators, you can protect yourself from potential online scams and make informed decisions when navigating the web.
- Lack of Customer Support: Scam sites often omit or provide minimal contact information. Check the “About us” or “Info” page; if there’s no contact info, it’s a red flag. Even if an email or phone number is given, they may remain unresponsive or reply with generic text.
- Reused Contact Information: As scammers frequently reuse phone numbers and email addresses, a simple Google search can reveal their deceptive activities. If the same contact details appear on a different site, it’s a clear indication of a scam.
- Stolen Images: Scammers, lacking real products, tend to steal images from other websites. Perform a reverse image search on Google to verify the uniqueness of product images. Identical goods marketed on various pages using the same images suggest a scam.
- Unrealistically High Discounts/Low Prices: Merchants won’t sell items at a loss. Discounts of 70%, 80%, or 90% are suspicious, even during sales events. Watch out for initial prices significantly lower than market norms, like $30 for a bed or $10 for a branded bag.
- Repetitive Site Design: Scammers reuse site designs under new web addresses. If the design mirrors another suspicious site, it’s a strong indicator of a scam. A reverse image search may lead you to the original scam site.
- Payments without Refund Options: Scammers prefer payment systems that lack refund options, such as direct bank transfers, CashApp, Venmo, or cryptocurrency. Once money is sent, there’s no recourse. Be cautious with payment methods that don’t offer refunds.
- Cryptocurrency Payments: Some scam websites may offer payments in cryptocurrency, which is less controllable than traditional methods. Cryptocurrency transactions attract fraudsters due to their irreversible nature.
- Fake or Absent Reviews: Scam sites aim for short lifespans, so they often lack customer reviews. While new legitimate sites may also lack reviews, be wary of fishy-looking feedback that doesn’t match the site’s offerings. Search for reviews on Google to verify legitimacy.
Remember, scammers aim for a quick profit and are less concerned about creating a convincing façade. By staying vigilant and recognizing these red flags, you can protect yourself from falling victim to online scams.
Warning signs of Trekdeals.com scam:
Trekdeals.com is a website that appears to be suspicious and possibly fraudulent. It’s important for smart shoppers to be aware of certain warning signs that suggest the site might not be trustworthy. These signs indicate that the website could be part of a larger network of scams and may not genuinely offer the products or services it claims to.
One major concern is that research has shown Trekdeals.com to be linked to a larger scam network called the “Uniqueness Scam Network.” This network, which is based in China, is known for operating multiple fake online stores that aim to deceive customers and commit fraud. These fake stores often present enticing deals but ultimately fail to deliver on their promises.
Another significant red flag is the website’s lack of transparency regarding its ownership and operation. Legitimate businesses usually provide clear information about who is behind the website, but Trekdeals.com doesn’t offer any such details. This lack of openness raises suspicions and suggests that the website might not have honest intentions.

Furthermore, the absence of any social media presence for Trekdeals.com is unusual and suspicious. Legitimate businesses typically use social media platforms to engage with customers, promote their products, and build a community. The fact that this website doesn’t have any social media accounts might indicate that it’s not a genuine brand.
The website also employs a tactic of offering extreme discounts to attract shoppers. While discounts are common, overly steep markdowns can be a sign of trouble. Legitimate companies cannot sustain such unrealistically low prices, which could be an indication that the products being sold might be counterfeit or of poor quality.
Trekdeals.com’s failure to provide any contact information is another troubling sign. Legitimate businesses usually make it easy for customers to get in touch, whether through a customer service phone number, a physical address, or a live chat option. The absence of these contact details suggests that the website is not interested in addressing customer concerns or providing proper support.
Even the legal pages on the website, such as the Terms of Service and Privacy Policy, seem to have been copied from other known scam websites. Scammers often plagiarize these pages to make their own websites appear more legitimate. However, these policies likely offer no real protection to users and may not even apply to Trekdeals.com.
The lack of original content on the website is another clear indication of its illegitimacy. All the product information and images seem to have been stolen from other established retailers. This lack of originality further supports the suspicion that Trekdeals.com is not a genuine online store.
Based on these red flags, it’s reasonable to conclude that Trekdeals.com is likely a scam website. This means that it’s not a reliable place to shop, and there’s a significant risk of losing both money and personal information if you make a purchase on the site. It’s crucial to prioritize your safety and satisfaction by avoiding websites like Trekdeals.com and others that share similar warning signs. Instead, opt for well-known and reputable online retailers that have a proven track record of delivering quality products and reliable services to customers. Your peace of mind and security should always come first when shopping online.
If you’ve made a purchase from Trekdeals.com, what steps should you take to address the situation and protect yourself?

If you’ve made a purchase on Trekdeals.com, take these steps to safeguard your information. Immediately change passwords, especially if used across multiple accounts. Consider two-factor authentication for added security against potential hackers.
Contact your bank if payment was made with a credit or debit card. Request transaction cancellation and initiate a refund. Report Trekdeals.com as fraudulent, urging them to block future charges.
Stay cautious about phishing emails related to your order. Treat emails offering discounts or refunds as potential phishing attempts. Avoid clicking on suspicious links or downloading attachments to prevent malware. Delete such emails promptly.
Enhance your online security with a content blocker like AdGuard to combat malicious ads, Trojans, and phishing attempts. This supplements your antivirus software for comprehensive protection.
If you suspect malware on your device, use SpyHunter 5 Anti-Malware for a thorough scan to ensure your security. These measures will help mitigate risks and protect your personal information from potential threats associated with Trekdeals.com. Stay vigilant and act promptly to secure your online presence.
How can Trekdeals.com affect browsers?

Scam online shopping sites, such as Trekdeals.com can affect browsers as well by spreading malware, infecting devices with viruses, and stealing personal information. Clicking on malicious links or downloading files from these sites can lead to harmful software infiltrating a user’s browser and system.
Additionally, these sites may use deceptive tactics to capture sensitive data like credit card details, login credentials, and personal information, leading to identity theft and financial loss. To detect and eliminate concealed risks, adhere to the following instructions for identifying and eradicating threats.
Special Offer (For Windows)
Browser-hijacker can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wait for next 48 hours. If you intend to remove detected threats instantly, then you will have to buy its licenses version that will activate the software fully.
Special Offer (For Macintosh) If you are a Mac user and browser-hijacker has affected it, then you can download free antimalware scanner for Mac here to check if the program works for you.
Antimalware Details And User Guide
Click Here For Windows Click Here For Mac
Important Note: This malware asks you to enable the web browser notifications. So, before you go the manual removal process, execute these steps.
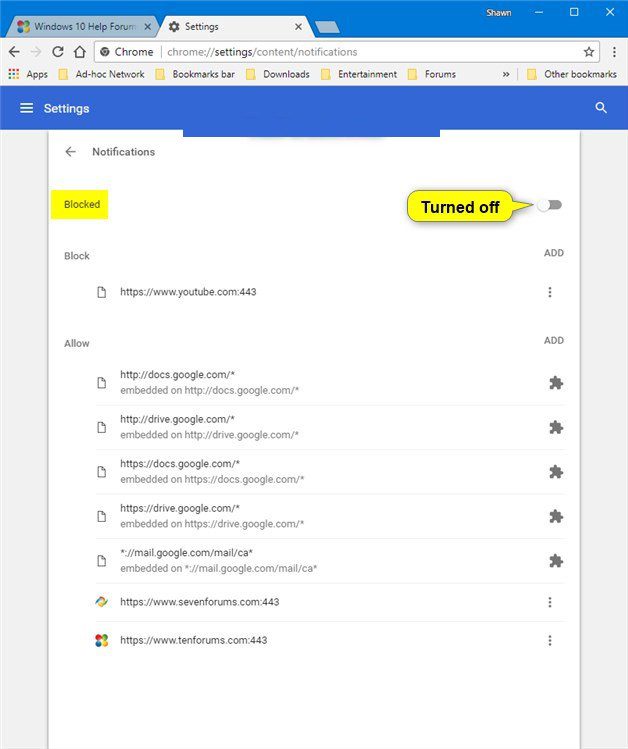
Google Chrome (PC)
- Go to right upper corner of the screen and click on three dots to open the Menu button
- Select “Settings”. Scroll the mouse downward to choose “Advanced” option
- Go to “Privacy and Security” section by scrolling downward and then select “Content settings” and then “Notification” option
- Find each suspicious URLs and click on three dots on the right side and choose “Block” or “Remove” option
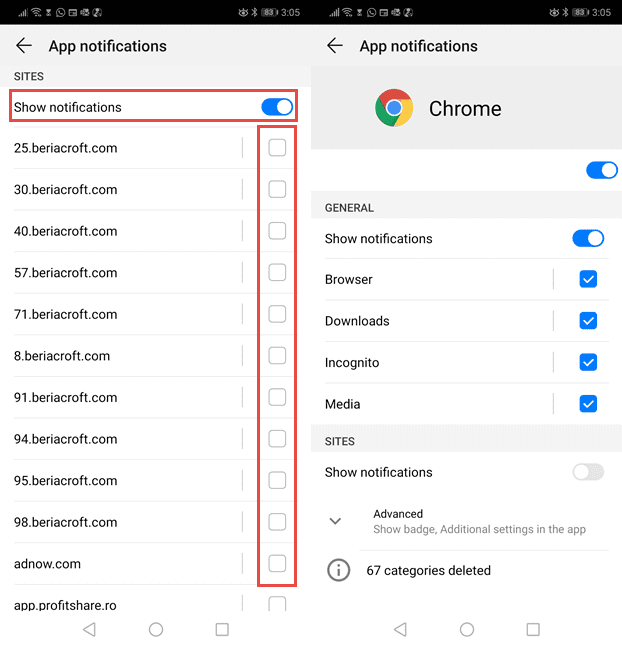
Google Chrome (Android)
- Go to right upper corner of the screen and click on three dots to open the menu button and then click on “Settings”
- Scroll down further to click on “site settings” and then press on “notifications” option
- In the newly opened window, choose each suspicious URLs one by one
- In the permission section, select “notification” and “Off” the toggle button
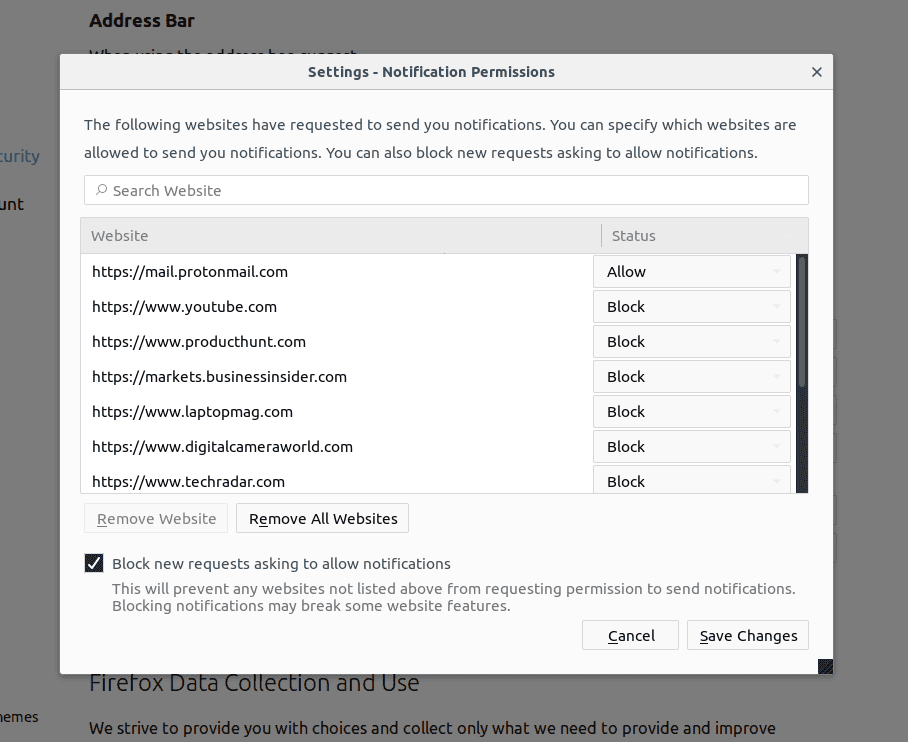
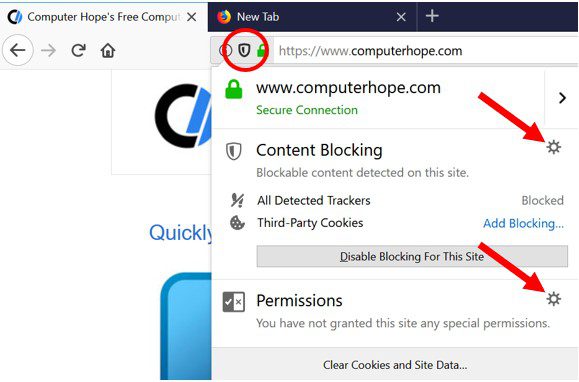
Mozilla Firefox
- On the right corner of the screen, you will notice three dots which is the “Menu” button
- Select “Options” and choose “Privacy and Security” in the toolbar present in the left side of the screen
- Slowly scroll down and go to “Permission” section then choose “Settings” option next to “Notifications”
- In the newly opened window, select all the suspicious URLs. Click on the drop-down menu and select “Block”
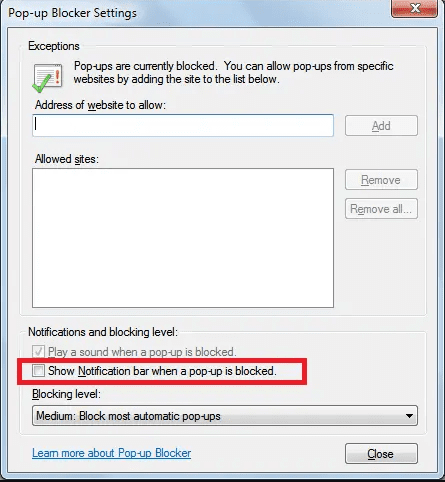
Internet Explorer
- In the Internet Explorer window, select the Gear button present on the right corner
- Choose “Internet Options”
- Select “Privacy” tab and then “Settings” under the “Pop-up Blocker” section
- Select all the suspicious URLs one by one and click on the “Remove” option
Microsoft Edge
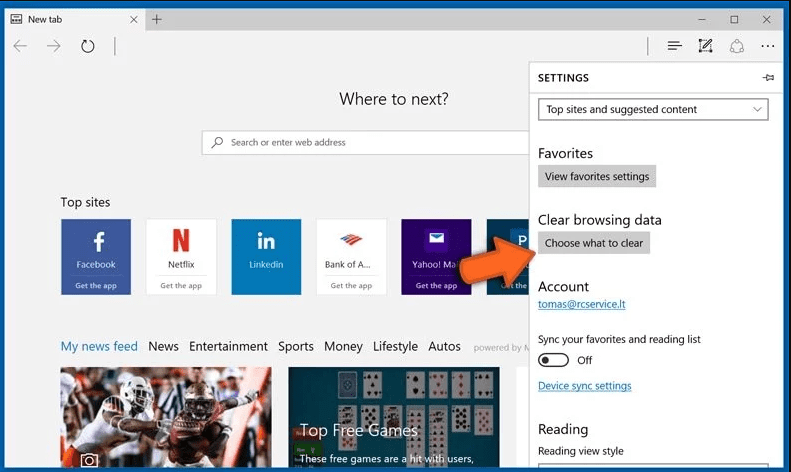
- Open the Microsoft Edge and click on the three dots on the right corner of the screen to open the menu
- Scroll down and select “Settings”
- Scroll down further to choose “view advanced settings”
- In the “Website Permission” option, click on “Manage” option
- Click on switch under every suspicious URL
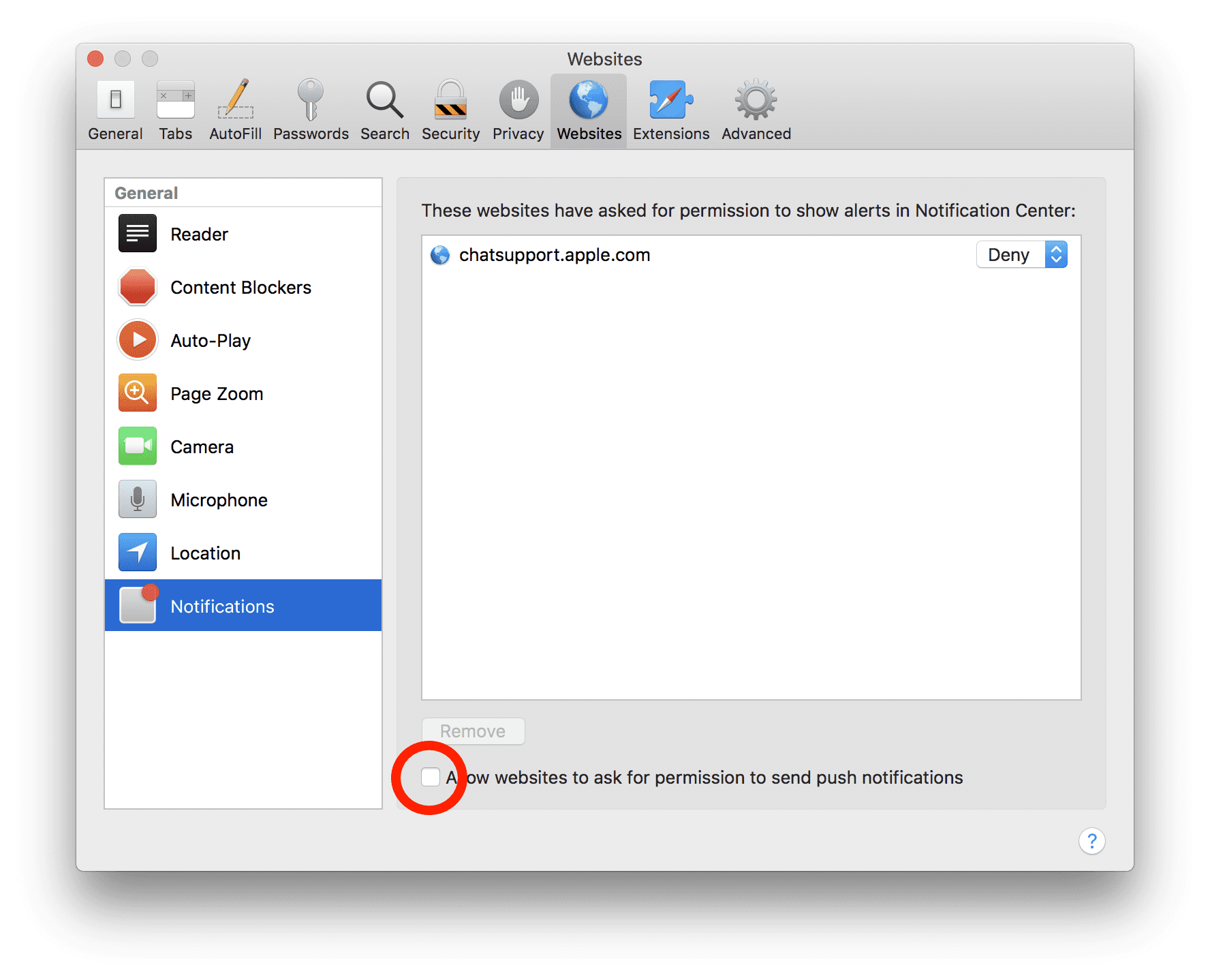
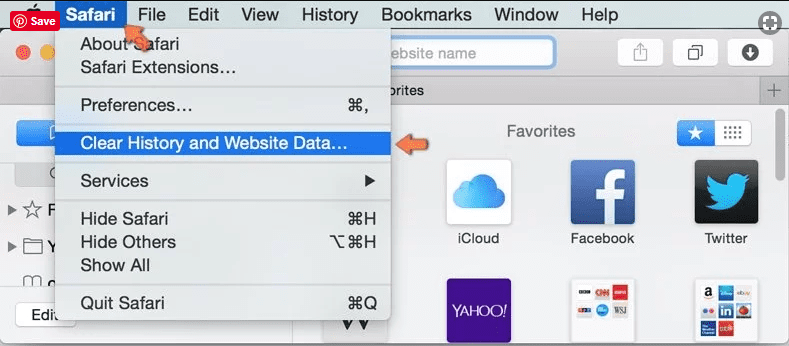
Safari (Mac):
- On the upper right side corner, click on “Safari” and then select “Preferences”
- Go to “website” tab and then choose “Notification” section on the left pane
- Search for the suspicious URLs and choose “Deny” option for each one of them
Manual Steps to Remove browser-hijacker:
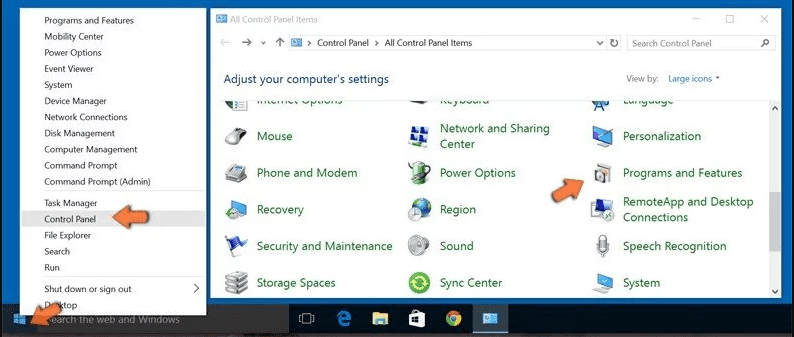
Remove the related items of browser-hijacker using Control-Panel
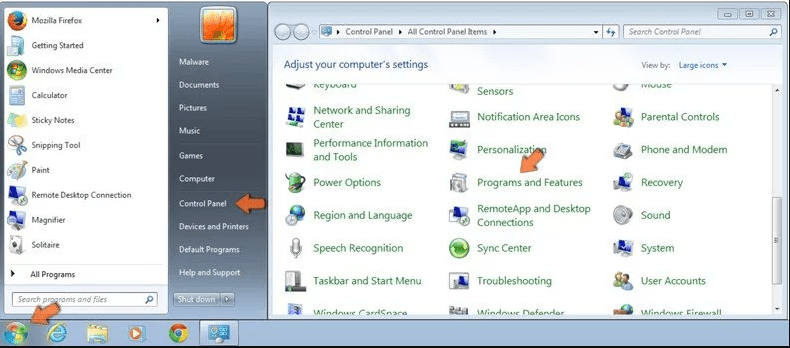
Windows 7 Users
Click “Start” (the windows logo at the bottom left corner of the desktop screen), select “Control Panel”. Locate the “Programs” and then followed by clicking on “Uninstall Program”
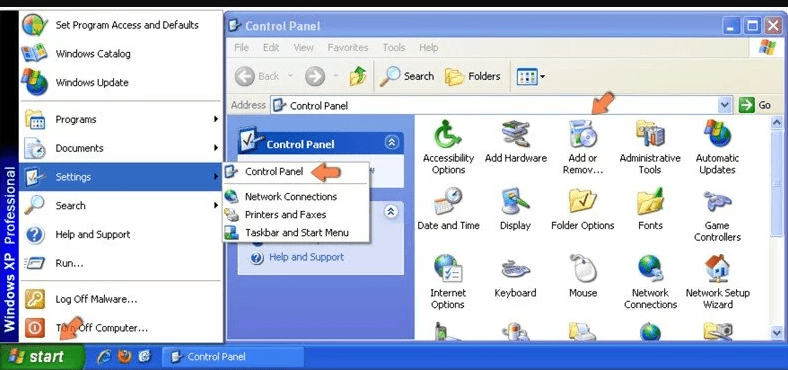
Windows XP Users
Click “Start” and then choose “Settings” and then click “Control Panel”. Search and click on “Add or Remove Program’ option
Windows 10 and 8 Users:
Go to the lower left corner of the screen and right-click. In the “Quick Access” menu, choose “Control Panel”. In the newly opened window, choose “Program and Features”
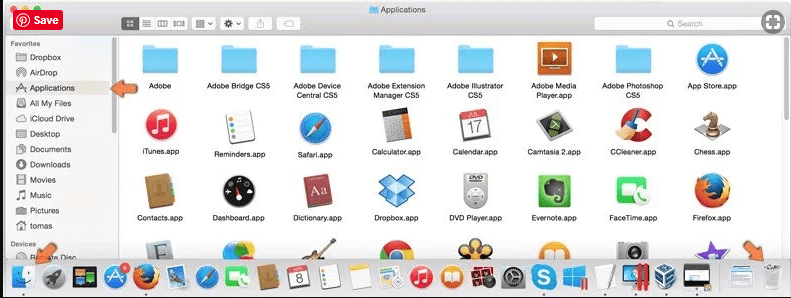
Mac OSX Users
Click on “Finder” option. Choose “Application” in the newly opened screen. In the “Application” folder, drag the app to “Trash”. Right click on the Trash icon and then click on “Empty Trash”.
In the uninstall programs window, search for the PUAs. Choose all the unwanted and suspicious entries and click on “Uninstall” or “Remove”.
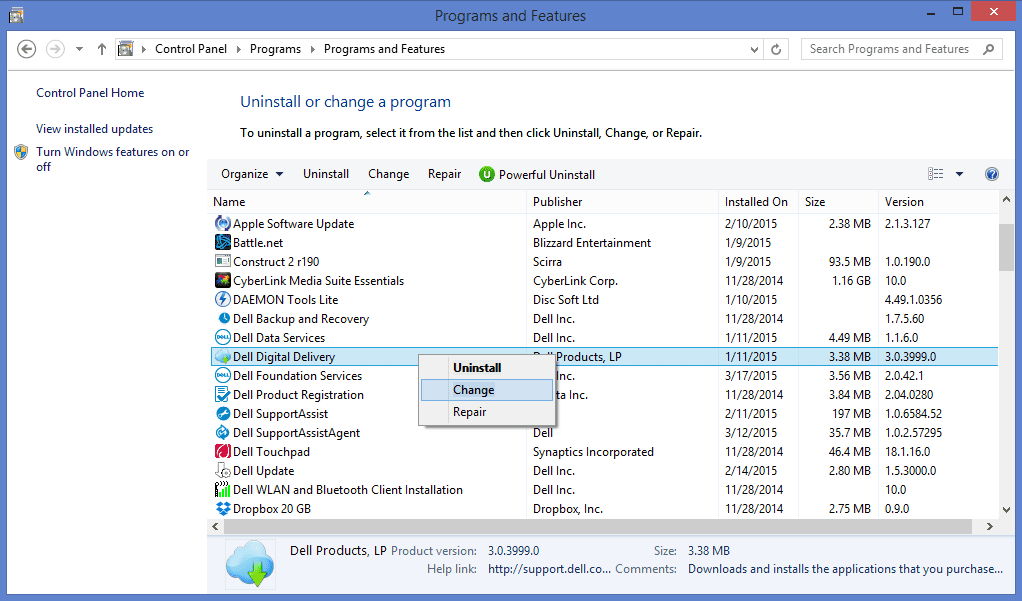
After you uninstall all the potentially unwanted program causing browser-hijacker issues, scan your computer with an anti-malware tool for any remaining PUPs and PUAs or possible malware infection. To scan the PC, use the recommended the anti-malware tool.
Special Offer (For Windows)
Browser-hijacker can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wait for next 48 hours. If you intend to remove detected threats instantly, then you will have to buy its licenses version that will activate the software fully.
Special Offer (For Macintosh) If you are a Mac user and browser-hijacker has affected it, then you can download free antimalware scanner for Mac here to check if the program works for you.
How to Remove Adware (browser-hijacker) from Internet Browsers
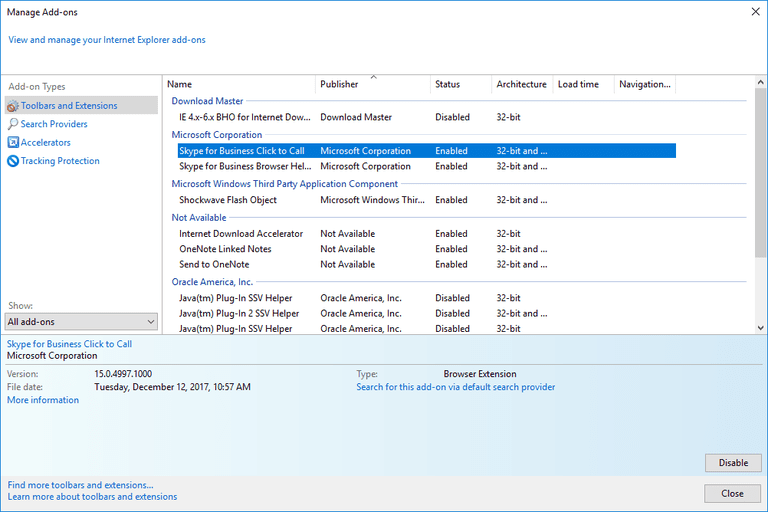
Delete malicious add-ons and extensions from IE
Click on the gear icon at the top right corner of Internet Explorer. Select “Manage Add-ons”. Search for any recently installed plug-ins or add-ons and click on “Remove”.
Additional Option
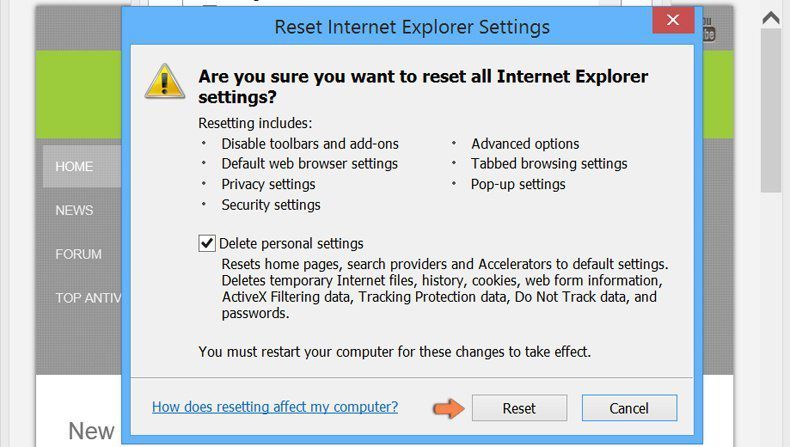
If you still face issues related to browser-hijacker removal, you can reset the Internet Explorer to its default setting.
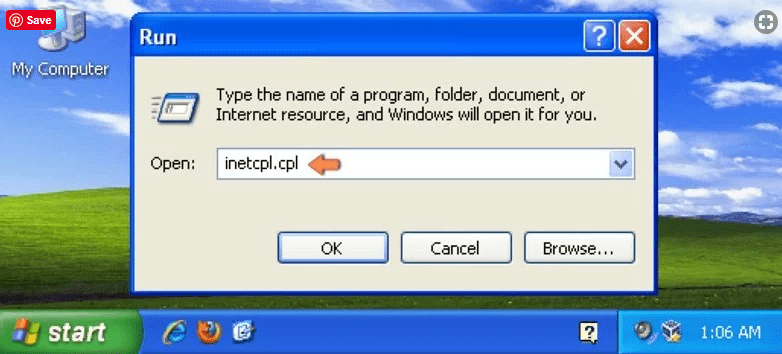
Windows XP users: Press on “Start” and click “Run”. In the newly opened window, type “inetcpl.cpl” and click on the “Advanced” tab and then press on “Reset”.
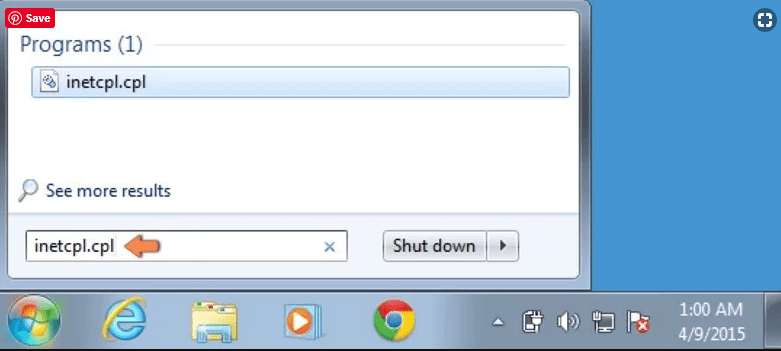
Windows Vista and Windows 7 Users: Press the Windows logo, type inetcpl.cpl in the start search box and press enter. In the newly opened window, click on the “Advanced Tab” followed by “Reset” button.
For Windows 8 Users: Open IE and click on the “gear” icon. Choose “Internet Options”
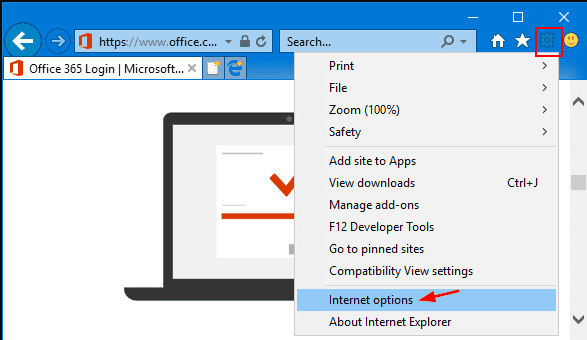
Select the “Advanced” tab in the newly opened window
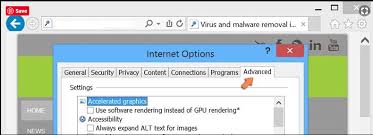
Press on “Reset” option
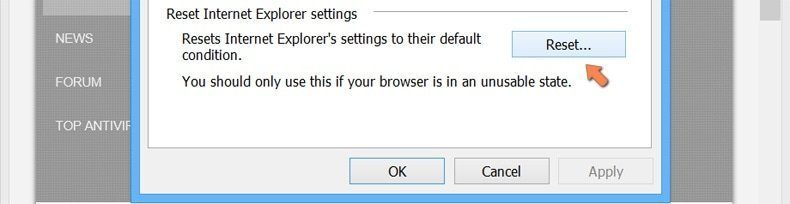
You have to press on the “Reset” button again to confirm that you really want to reset the IE
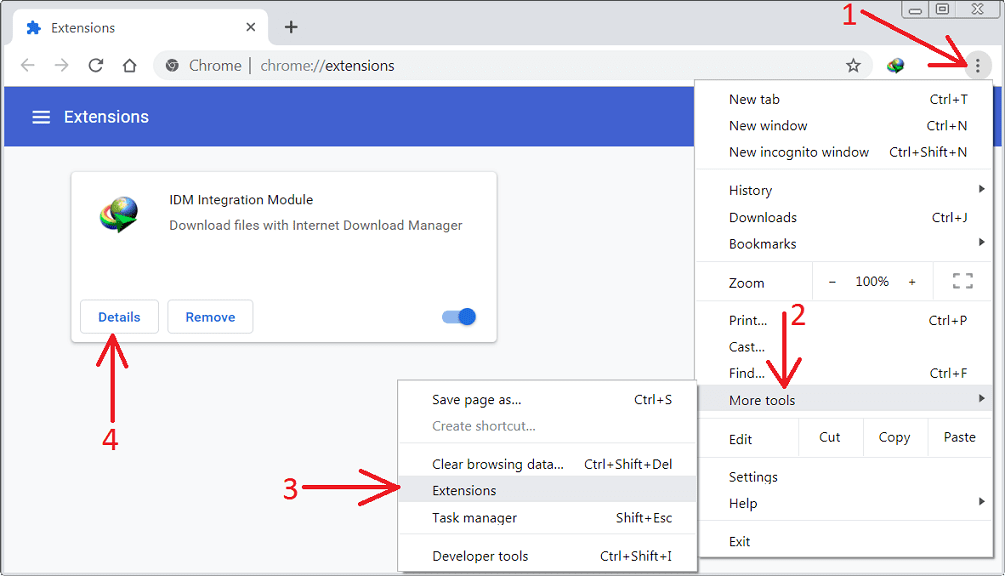
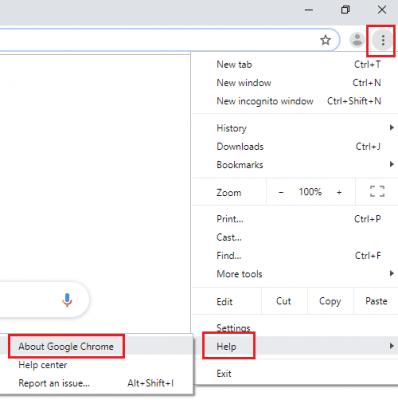
Remove Doubtful and Harmful Extension from Google Chrome
Go to menu of Google Chrome by pressing on three vertical dots and select on “More tools” and then “Extensions”. You can search for all the recently installed add-ons and remove all of them.
Optional Method
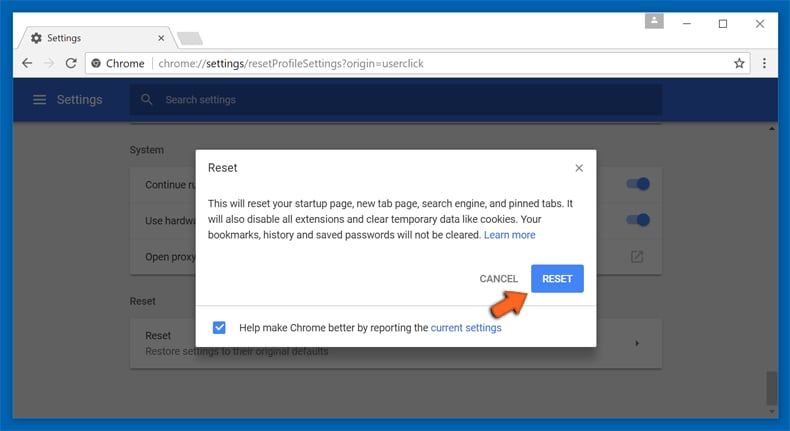
If the problems related to browser-hijacker still persists or you face any issue in removing, then it is advised that your reset the Google Chrome browse settings. Go to three dotted points at the top right corner and choose “Settings”. Scroll down bottom and click on “Advanced”.
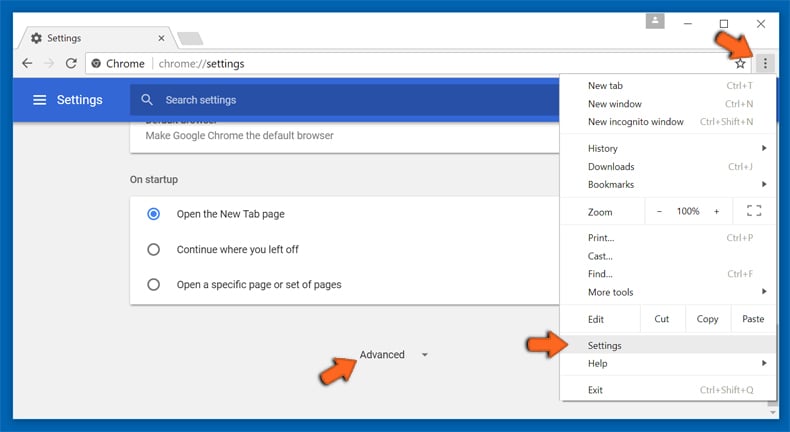
At the bottom, notice the “Reset” option and click on it.
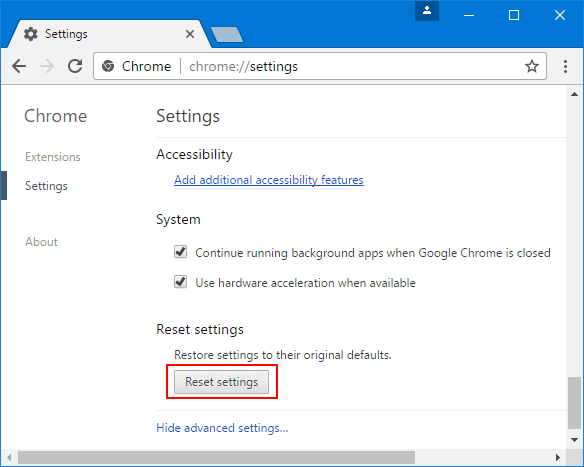
In the next opened window, confirm that you want to reset the Google Chrome settings by click on the “Reset” button.
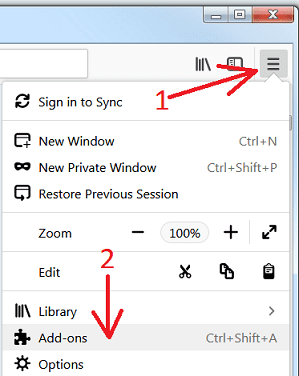
Remove browser-hijacker plugins (including all other doubtful plug-ins) from Firefox Mozilla
Open the Firefox menu and select “Add-ons”. Click “Extensions”. Select all the recently installed browser plug-ins.
Optional Method
If you face problems in browser-hijacker removal then you have the option to rese the settings of Mozilla Firefox.
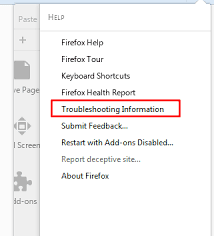
Open the browser (Mozilla Firefox) and click on the “menu” and then click on “Help”.
Choose “Troubleshooting Information”
In the newly opened pop-up window, click “Refresh Firefox” button
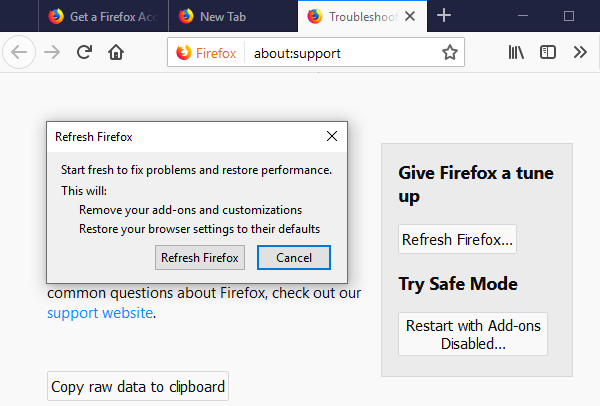
The next step is to confirm that really want to reset the Mozilla Firefox settings to its default by clicking on “Refresh Firefox” button.
Remove Malicious Extension from Safari
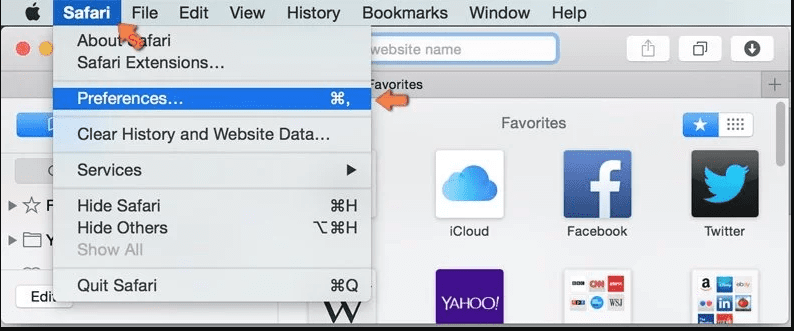
Open the Safari and go to its “Menu” and select “Preferences”.
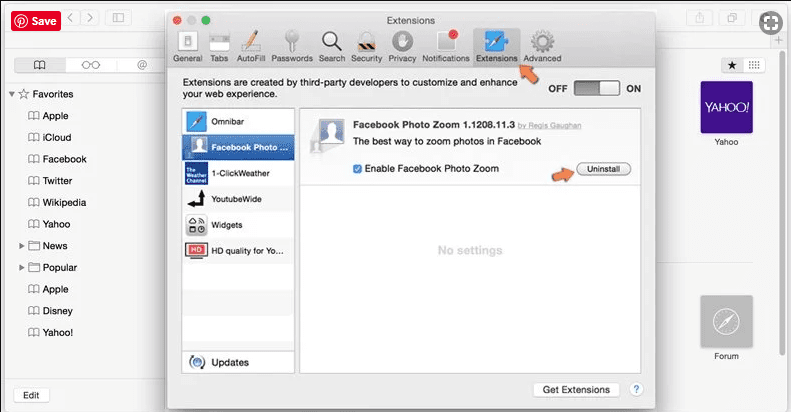
Click on the “Extension” and select all the recently installed “Extensions” and then click on “Uninstall”.
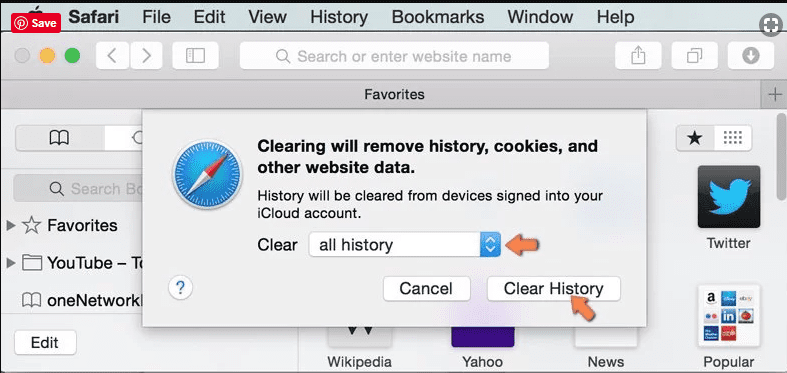
Optional Method
Open the “Safari” and go menu. In the drop-down menu, choose “Clear History and Website Data”.
In the newly opened window, select “All History” and then press on “Clear History” option.
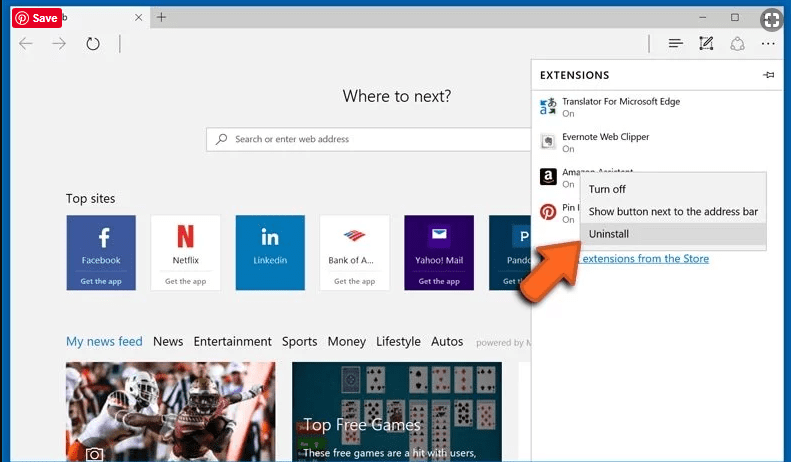
Delete browser-hijacker (malicious add-ons) from Microsoft Edge
Open Microsoft Edge and go to three horizontal dot icons at the top right corner of the browser. Select all the recently installed extensions and right click on the mouse to “uninstall”
Optional Method
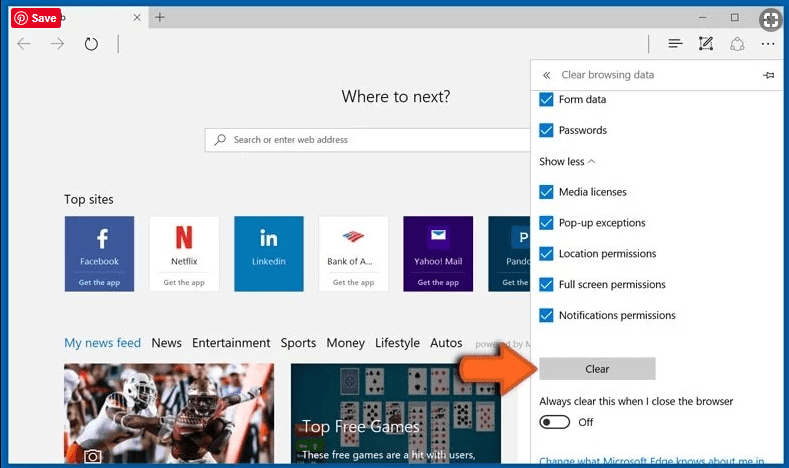
Open the browser (Microsoft Edge) and select “Settings”
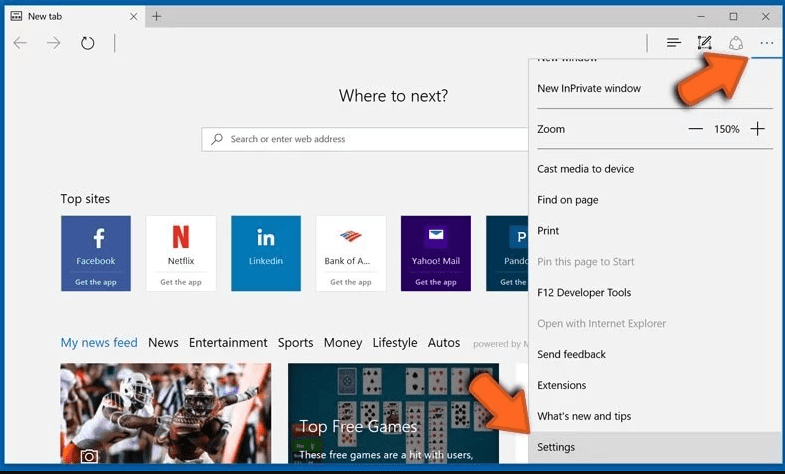
Next steps is to click on “Choose what to clear” button
Click on “show more” and then select everything and then press on “Clear” button.
Recommended online habits you should acquire?
As soon as browser-hijacker infiltrates the PC system, it starts carrying out malicious activities in the background and may lead to a number of unpleasant issues. To avoid getting infected with such browser-based pests, below are some steps you can take:
- Download software from reputable sources: Only download software from reputable websites, such as the official page of the software vendor or well-known download portals. Avoid downloading software from third-party websites or peer-to-peer networks, as these are often sources of bundled adware.
- Pay attention during the installation process: When installing software, pay attention to each step of the installation process. Look for the checkboxes that may indicate the installation of additional software, such as adware or browser extensions. Uncheck these boxes if you don’t want to install the additional software.
- Choose custom installation: During the installation process, choose the custom installation option instead of the default or express installation. This will allow you to select which components to install and to opt-out of installing any bundled adware or other unwanted software.
- Read the End User License Agreement (EULA): Read the EULA carefully before installing any software. Look for clauses that may allow the installation of additional software or adware like browser-hijacker. If EULA contains such clauses, reconsider installing the software.
- Use a reputable web browser: Choose a reputable web browser, such as Google Chrome or Mozilla Firefox, and keep it up-to-date with the latest security patches.
- Install ad-blockers and pop-up blockers: You should use ad-blockers and pop-up blockers to prevent unwanted ads and pop-ups from appearing on your computer screen. Some web browsers have built-in ad-blocker and pop-up blockers, or you can install browser extensions that provide this functionality.
- Be careful when clicking on links: Don’t click on links in emails or on websites unless you are sure they are legitimate. Check the URL and ensure it is spelled correctly and is the correct website. Be wary of shortened URLs or URLs that lead to suspicious or unknown websites.
- Keep your web browser and operating system up-to-date: Regularly install software updates and security patches for your web browser and operating system. This will help to close any security vulnerabilities that adware, hijacker and other malware may exploit.
- Use a reputable antivirus program: A good antivirus program can detect and block infections like browser-hijacker and other malware before they can infect your computer. Make sure you choose a reliable antivirus suite and keep it up-to-date with the latest virus definitions.
By following these steps, you can minimize the risk of potentially unwanted program intrusion and keep your PC system safe and secure.
Conclusion:
To sum up, browser-hijacker can cause significant problems for computer users, including unwanted browser redirects, changes to homepage and search engine settings, and even the installation of additional malware. These infections typically result from downloading and installing software from untrusted sources or clicking on suspicious links. To prevent browser hijackers or adware, it is important to be cautious when downloading and installing software, use reputable antivirus tool, and keep browsers and operating systems updated with the latest security patches.
Related FAQs about browser-hijacker
What are the Symptoms of Browser-hijacker ?
The common symptoms of browser-hijacker infection include changes to the default homepage and search engine, unwanted toolbars and extensions, pop-up ads, and redirects to unfamiliar websites. Additionally, the browser may slow down or crash frequently, and search results may be manipulated or irrelevant to the query.
What Should I do if my PC gets infected with virus like browser-hijacker?
If your computer is infected with this browser-based threat, you should immediately run a virus scan using reputable antivirus software. If the software detects the malware, you should follow the removal instructions provided by it to eliminate the infection and restore your browser settings to default.
How can I protect my password and other personal credentials from browser-hijacker?
To protect your password and other sensitive information from browser-hijacker, you should employ reputable antivirus suite, enable two-factor authentication on all accounts, and use strong and unique passwords for each account. Also, you should avoid clicking on suspicious links or downloading software from untrusted sources.
Why I should trust your research conducted on browser-hijacker?
It’s important to mention that our research is conducted independently and with the assistance of unbiased security experts, who provide us with daily updates on the latest definitions and threats related to malware, adware, and browser hijackers. Moreover, our study on the browser-hijacker threat is supported by VirusTotal.
Special Offer (For Windows)
Browser-hijacker can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wait for next 48 hours. If you intend to remove detected threats instantly, then you will have to buy its licenses version that will activate the software fully.
Special Offer (For Macintosh) If you are a Mac user and browser-hijacker has affected it, then you can download free antimalware scanner for Mac here to check if the program works for you.

