Remove Cylance Ransomware (Open Locked Files)

To remove Cylance Ransomware, follow these steps:
- Disconnect from internet and other devices to prevent the infection from spreading.
- Employ a trusted antivirus software to scan and remove the malware.
- Restore your files from a backup if available.
- If backup is not available, try using a decryption tool.
- If none of the above works, seek professional assistance.
Complete Guide To Terminate Crypto-Virus
Cylance Ransomware is a malicious software piece that encrypts files and appends the “.Cylance” extension to filenames. It also creates a ransom note called “CYLANCE_README.txt”. This ransomware targets Windows and Linux OS. However, it’s important to note that Cylance enterprise cybersecurity is not related to this ransomware and offers endpoint security services.
Ransomware viruses like Cylance, Jypo Ransomware, etc. operate differently from other types of malware, making them more difficult to detect and remove. This is due to their use of encryption to lock certain files, preventing access and allowing them to complete their task without interference from security programs. These parasites encrypt files, effectively blocking them and making them inaccessible to users.
Threat Summary
Name: Cylance Ransomware
Category: Ransomware, File-Locking virus
Characteristics: Encrypts users’ files and asks victims to pay ransom money for the decryption
Extension: .Cylance
Ransom note: CYLANCE_README.txt
Danger level: High
Attackers’ Contact: [email protected] and [email protected]
Symptoms: The compromised files cannot be opened or used, ransom note appearing, strange file extension
Infiltration: Spiteful email attachments, infected sites, fake updaters and installers, etc.
One View On Cylance Ransom Note:
When a ransomware attack occurs, a ransom note is often left behind for the victim. The note shown by Cylance Ransomware informs the victim that all their files have been encrypted and are inaccessible, and provides instructions on how to recover them. The perpetrators of the attack are typically motivated by financial gain, and they offer to decrypt one file as proof of their ability to restore the data. Victims are warned not to use any third-party software or antivirus solutions, as this could result in further data loss by damaging the private key. The note also provides email addresses for victims to contact the attackers for further instructions: [email protected] and [email protected].
Should The Ransom Be Paid?
Victims of Cylance Ransomware should not pay the attackers because it encourages and funds criminal activity. There is no guarantee that paying the ransom will result in the return of the encrypted files, as the criminals may simply take the money and disappear. In addition, paying the ransom fuels the growth of the ransomware industry and may even make the victim a target for future attacks. It’s recommended to try alternative methods of recovery, but before that, remove Cylance Ransomware from the computer using a professional security app.
How To Recover The Locked Data?
If you are a victim of .cylance file virus, you can attempt to restore your files from backup if available. If no backup is available, check if a decryption tool is available online, or try our proficient data-recovery software. If all else fails, seek professional help from a cybersecurity expert or data recovery service. It is important to not pay the ransom, as it encourages and funds criminal activity without any guarantee of file recovery. Before going for any recovery method, make sure to eliminate the threat from the computer.
Frequently Asked Questions
What damage Cylance Ransomware can do?
Cylance Ransomware can cause significant damage to your computer and personal data. It encrypts files, making them inaccessible to you, and can delete or modify files to cause further damage. Additionally, it can steal sensitive information and spread to other devices on the network, causing further infections. Cylance also leaves a ransom note demanding payment in exchange for decryption of the encrypted files, which may lead to financial loss for you.
How to open the “.cylance” files?
Unfortunately, there is currently no known way to open the “.cylance” files encrypted by Cylance Ransomware. Still, it’s important to not pay the ransom as there is no guarantee that the attackers will provide a decryption key. It’s recommended to try restoring files from backups or seek professional help from a cybersecurity expert or data recovery service.
Message In The Ransom Note:
[[=== Cylance Ransomware ===]]
[+] What’s happened?
All your files are encrypted, and currently unsable, but you need to follow our instructions. otherwise, you cant return your data (NEVER).
[+] What guarantees?
Its just a business. We absolutely do not care about you and your deals, except getting benefits. If we do not do our work and liabilities – nobody will not cooperate with us. Its not in our interests.
To check the ability of returning files, we decrypt one file for free. That is our guarantee.
If you will not cooperate with our service – for us, its does not matter. But you will lose your time and data, cause just we have the private key. time is much more valuable than money.
[+] How to cantact with us?
Please write an email to: [email protected] and [email protected]
Write this U-ID in the subject: 9cz9eXn9z
Key:
–
————
!!! DANGER !!!
DON’T try to change files by yourself, DON’T use any third party software for restoring your data or antivirus solutions – its may entail damage of the private key and, as result, The Loss all data.
!!! !!! !!!
ONE MORE TIME: Its in your interests to get your files back. From our side, we (the best specialists) make everything for restoring, but please should not interfere.
!!! !!! !!!
Step1. Remove Connected Devices and Isolate the Infected PC
It is very important that you cut off your infected PC with other computers connected in the same local network. Many of the ransomware are designed in such a way that it spreads in network environment. Hence, you need to take some measures to isolate the PC.
There are two basics steps for separate the infected device.
- Disconnect Internet
- Unplug all the external storage device
- Log out of Cloud Storage Accounts (Additional)
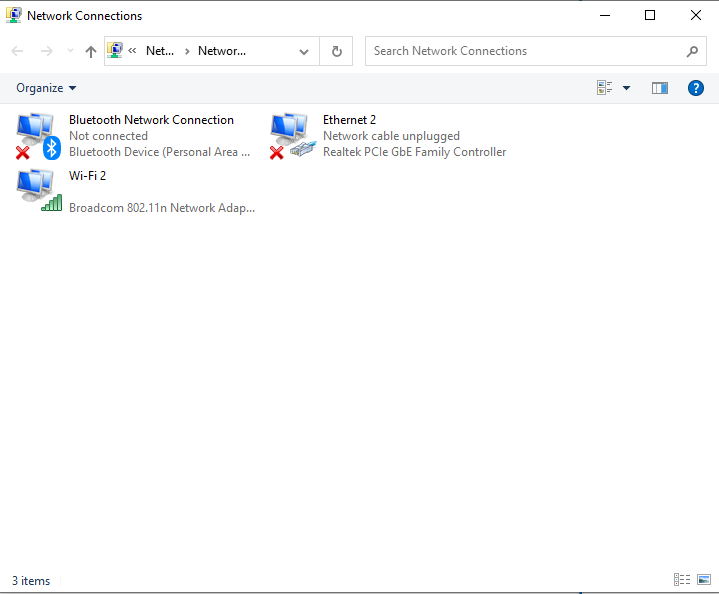
Unplug the Ethernet Cable so that all the wired internet connection gets cut off. In case if the infected PC is connected with wireless internet, you have to disconnect it manually through Control Panel.
Go to Control Panel> Search ‘Network and Sharing Center’
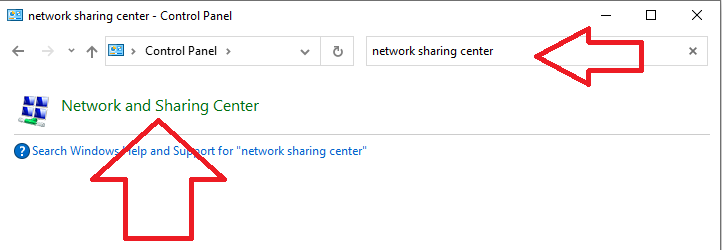
Click on ‘Change adapter settings’
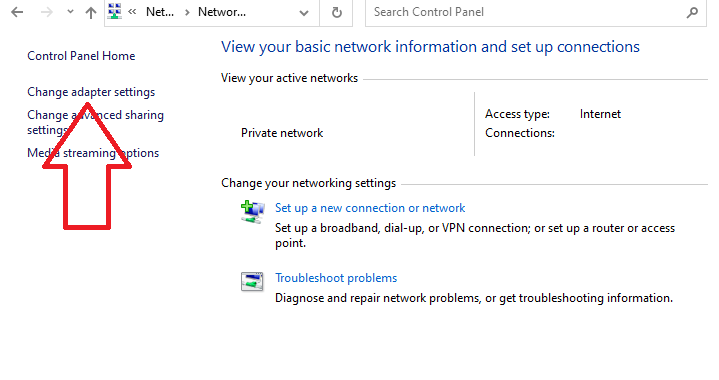
Select the internet connect point, right lick on it and choose ‘Disable’. The PC is no longer connected with internet.
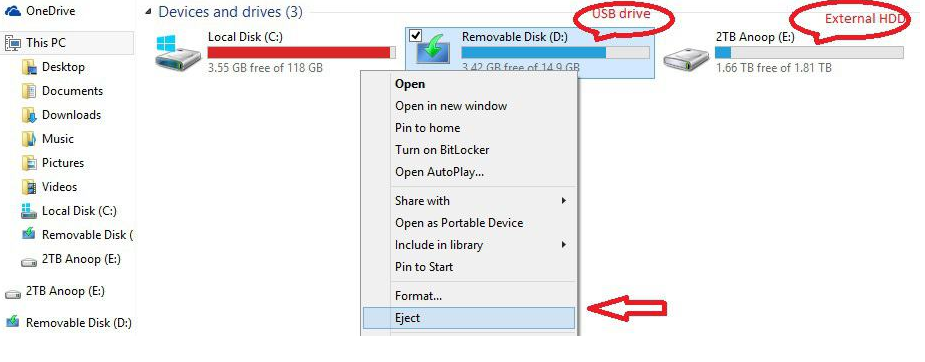
Once the PC is disconnected with internet, the next step is to unplug the connected storage device in order to isolate the computer completely. All kind of storage device such as portable hard drives, pen-drives, flash drives etc. is to be removed so that Cylance Ransomware doesn’t encrypts files stored in them.
Go to “My Computer”, right click on the connected storage device and select “Eject”.
There is high possibility that ransomware could take over the software that handles data stored in “cloud storage”. Hence it is strongly recommended that you log out from your cloud storage whether it is through browser or cloud management software.
Step2. Identify the Ransomware that Attacked your Files
It is important to identify the name and type of ransomware that had attacked your work-station so that you can use the right decryption tool for recovering the locked files. This is important because decryption tool for ransowmare released by security experts are exclusive for particular ransomware and their family. If you use incorrect decryption tool which is not designed for removing Cylance Ransomware, then this may damage the locked files permanently.
There are possibly three ways to identity the ranosmware infected your PC. First is to go through the rnasowmare note and see if the name is mentioned or not. For example, In Cerber ransomware note, the name of ransomware is clearly mentioned.
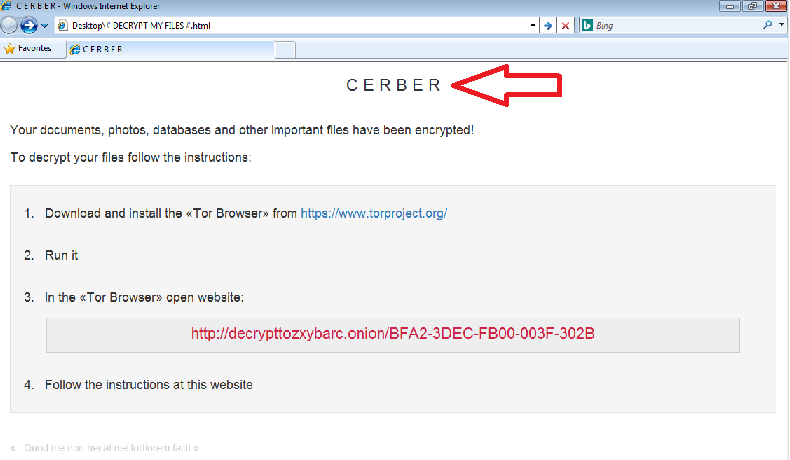
On many occasion, the ransomware name is not mentioned in the note. They contain generic message. Researches shows that different rasnowmare may have same ransom note but they belong from entirely different family or group.
So, if the ransomware note is generic and its name and type is not mentioned, you need to check file extension that it adds on the locked file. When a ransomware locks any file, it appends its own extension name to it in addition. For example, Locky ransomware adds .locky extension name on every files that it encrypts.
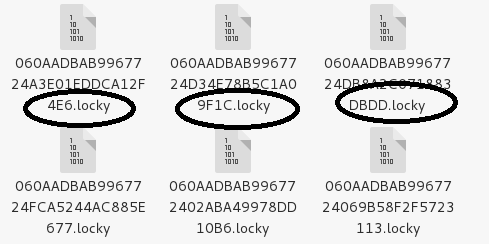
Many of the ransomware uses generic extension names as well such as .encrypted, .locked, .crypted etc. In this case, the generic extension name doesn’t reveals anything about the ransomware name and type.
So, if you are unable to identify the ransomware through its note and extension, it is best to visit ID Ransomware website and upload the ransom note you receive or any one of your file that has been encrypted or possibly both.
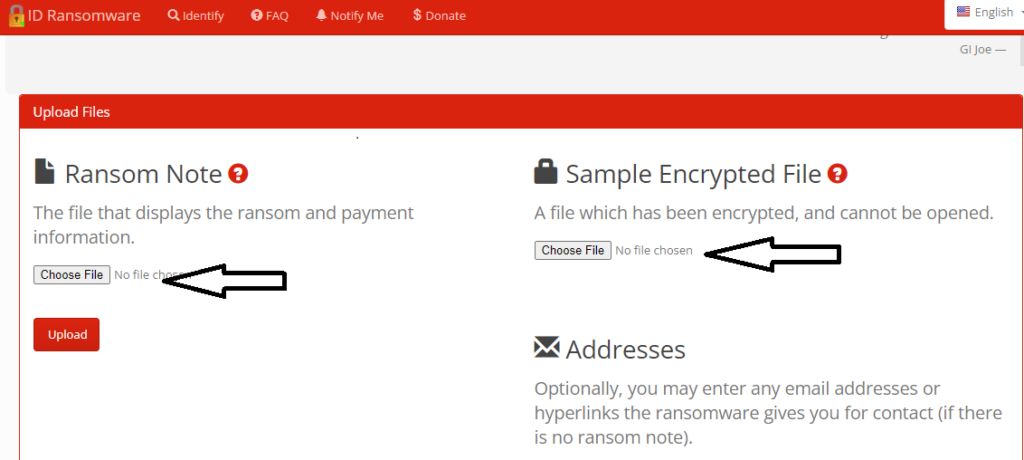
At present, ID ransowmare database has details of around 1100 different ransomwares. In case if the ransomware that infected your files is not supported by ID ransomware website, you can use internet to search more about the ransomware using keywords like its file extension, crypto wallet address or contact email Id.
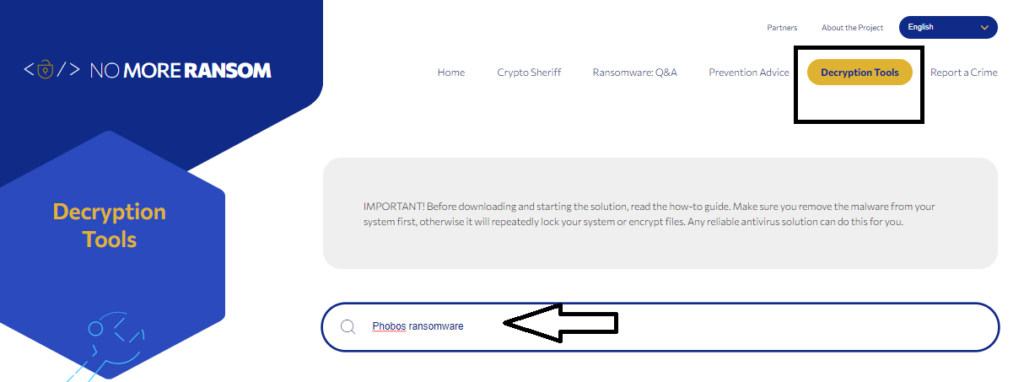
Step 3. Search for Cylance Ransomware Decryption Tool to Recover Locked Files
The developer behind ransomware uses highly advanced encryption key to lock the files on the infected PC and hence if it manages to encrypt the file properly, it cannot be decrypted without the correct decryption key. The unlock key is stored in a remote server. Popular ransowmare family such as Dharma, Cerber, Phobos etc. are known to create flawless ransomware and they update their version time to time.
However, there are so many ransomware types that are poorly developed and have flaws in terms of using unique decryption key for each victim, their decryption key are stored on the infected PC instead of remote server and so on. So, the decryption key for such poorly designed ransomware are available on internet. You just have to check some security forums and Online communities to get identical decryption key for poorly designed ransowmare.
To be on safer side, it is recommended to use platforms such as https://www.nomoreransom.org/en/index.html which have tried and tested decryption key for some of the popular ransomware. Its homepage contains a “Decryption Tools” category with search bar option where you can search for decryption key for a particular ransomware.
How to Remove Cylance Ransomware and Recover locked Files Using Data Recovery Tool
1: Boot the PC “Safe Mode with Networking”
For Windows XP and Windows 7 users: Boot the PC in “Safe Mode”. Click on “Start” option and continuously press on F8 during the start process until the “Windows Advanced Option” menu appears on the screen. Choose “Safe Mode with Networking” from the list.
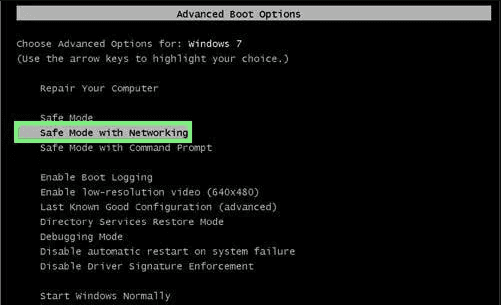
Now, a windows home screen appears on the desktop and work-station is now working on “Safe mode with networking”.
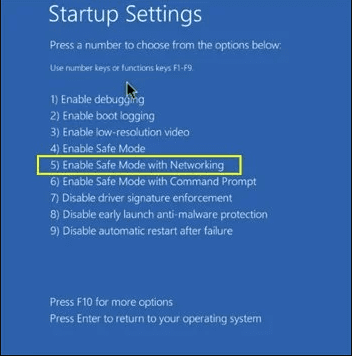
For Windows 8 Users: Go to the “Start Screen”. In the search results select settings, type “Advanced”. In the “General PC Settings” option, choose “Advanced startup” option. Again, click on the “Restart Now” option. The work-station boots to “Advanced Startup Option Menu”. Press on “Troubleshoot” and then “Advanced options” button. In the “Advanced Option Screen”, press on “Startup Settings”. Again, click on “Restart” button. The work-station will now restart in to the “Startup Setting” screen. Next is to press F5 to boot in Safe Mode in Networking.
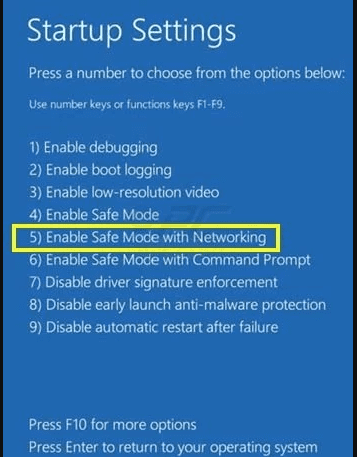
For Windows 10 Users: Press on Windows logo and on the “Power” icon. In the newly opened menu, choose “Restart” while continuously holding “Shift” button on the keyboard. In the new open “Choose an option” window, click on “Troubleshoot” and then on the “Advanced Options”. Select “Startup Settings” and press on “Restart”. In the next window, click on “F5” button on the key-board.
Once the PC get booted in Safe mode with networking, you can use anti-malware tool such as “SpyHunter”. The automatic removal tool has advanced scanning algorithm and programming logics hence it doesn’t leave any trace of ransomware behind.
Click Here For SpyHunter Details and User Guide
Open the browser and download a legitimate anti-malware tool. Do a full System scanning. Remove all the malicious detected entries including those belong to ransomware.
Special Offer (For Windows)
Cylance Ransomware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Data Recovery Offer
We Suggest you to choose your lately created backup files in order to restore your encrypted files, however in case if you don’t have any such backups, you can try a data recovery tool to check if you can restore your lost data.
2: Delete Cylance Ransomware Infection using “System Restore”
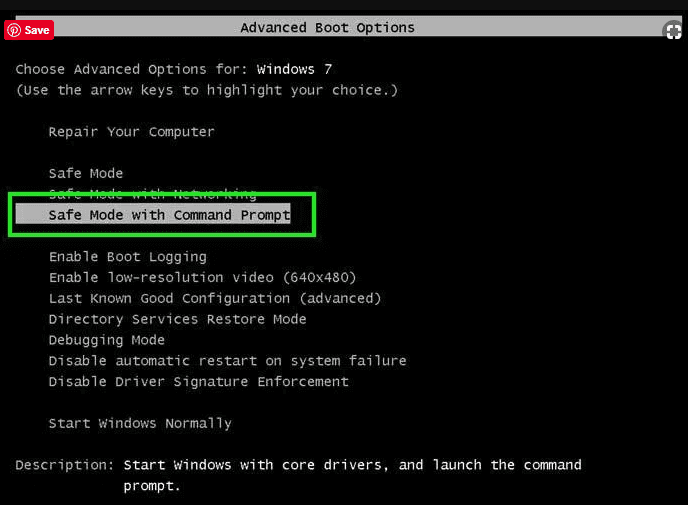
In case if you cannot start the PC in “Safe Mode with Networking”, Try using “System Restore”. During the “Startup”, continuously press on F8 key until the “Advanced Option” menu appears. From the list, choose “Safe Mode with Command Prompt” and then press “Enter”
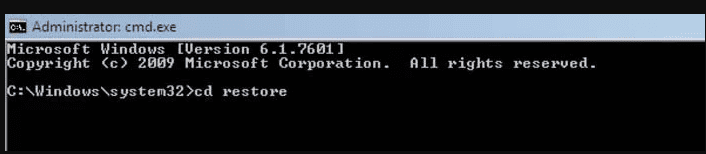
In the new opened command prompt, enter “cd restore” and then press “Enter”.
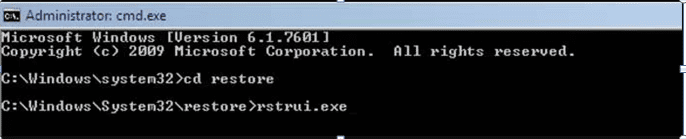
Type: rstrui.exe and Press “ENTER”
Click “Next” on the new windows
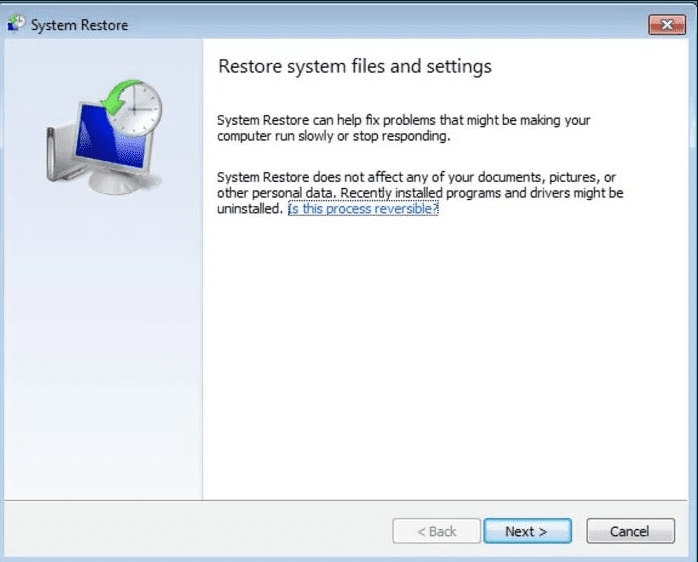
Choose any of the “Restore Points” and click on “Next”. (This step will restore the work-station to its earlier time and date prior to Cylance Ransomware infiltration in the PC.
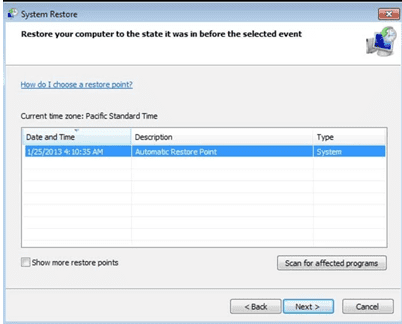
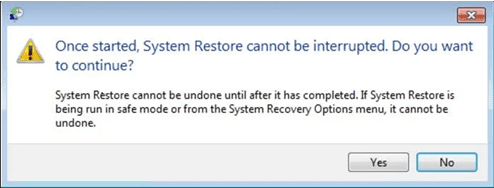
In the newly opened windows, press on “Yes”.
Once your PC gets restored to its previous date and time, download the recommended anti-malware tool and perform a deep scanning in order to remove Cylance Ransomware files if they left in the work-station.
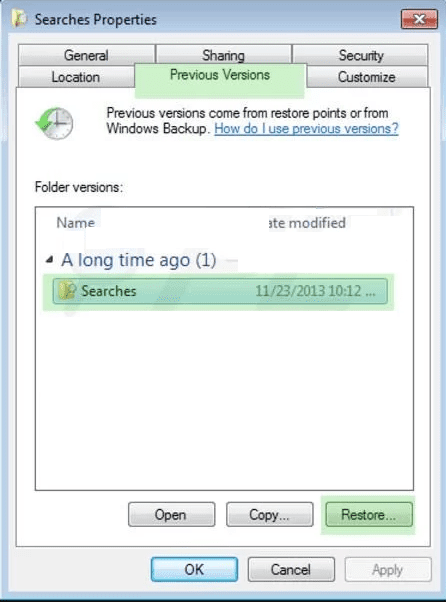
In order to restore the each (separate) file by this ransomware, use “Windows Previous Version” feature. This method is effective when “System Restore Function” is enabled in the work-station.
Important Note: Some variants of Cylance Ransomware delete the “Shadow Volume Copies” as well hence this feature may not work all the time and is applicable for selective computers only.
How to Restore Individual Encrypted File:
In order to restore a single file, right click on it and go to “Properties”. Select “Previous Version” tab. Select a “Restore Point” and click on “Restore” option.
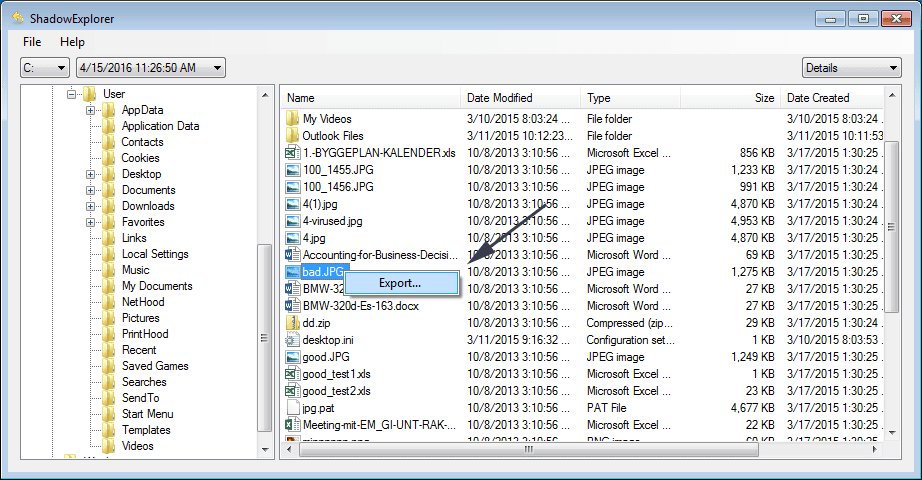
In order to access the files encrypted by Cylance Ransomware, you can also try using “Shadow Explorer”. In order to get more information on this application, press here.
Important: Data Encryption Ransomware are highly dangerous and it is always better that you take precautions to avoid its attack on your work-station. It is advised to use a powerful anti-malware tool in order to get protection in real-time. With this help of “SpyHunter”, “group policy objects” are implanted in the registries in order to block harmful infections like Cylance Ransomware.
Also, In Windows 10, you get a very unique feature called “Fall Creators Update” that offer “Controlled Folder Access” feature in order to block any kind of encryption to the files. With the help of this feature, any files stored in the locations such as “Documents”, “Pictures”, “Music”, “Videos”, “Favorites” and “Desktop” folders are safe by default.
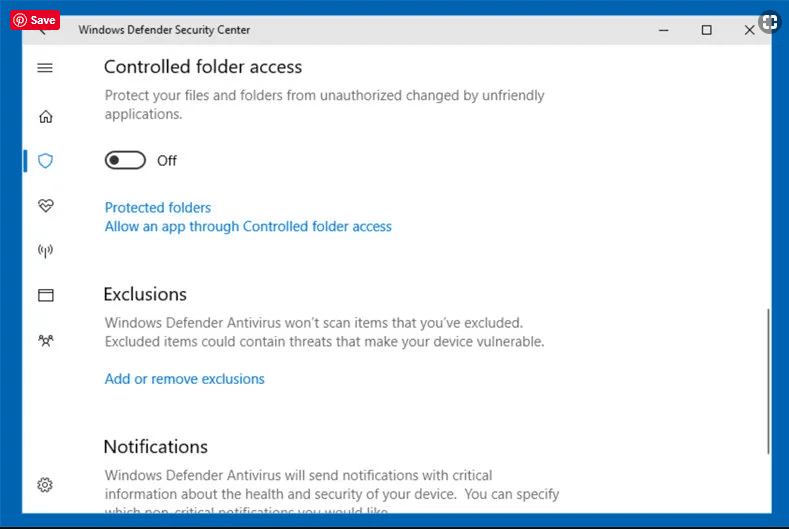
It is very important that you install this “Windows 10 Fall Creators Update” in your PC to protect your important files and data from ransomware encryption. The more information on how to get this update and add an additional protection form rnasomware attack has been discussed here.
3. How to Recover the Files Encrypted by Cylance Ransomware?
Till now, you would have understood that what had happed to your personal files that got encrypted and how you can remove the scripts and payloads associated with Cylance Ransomware in order to protect your personal files that has not been damaged or encrypted until now. In order to retrieve the locked files, the depth information related to “System Restore” and “Shadow Volume Copies” has already been discussed earlier. However, in case if you are still unable to access the encrypted files then you can try using a data recovery tool.
Use of Data Recovery Tool
This step is for all those victims who have already tries all the above mentioned process but didn’t find any solution. Also it is important that you are able to access the PC and can install any software. The data recovery tool works on the basis of System scanning and recovery algorithm. It searches the System partitions in order to locate the original files which were deleted, corrupted or damaged by the malware. Remember that you must not re-install the Windows OS otherwise the “previous” copies will get deleted permanently. You have to clean the work-station at first and remove Cylance Ransomware infection. Leave the locked files as it is and follow the steps mentioned below.
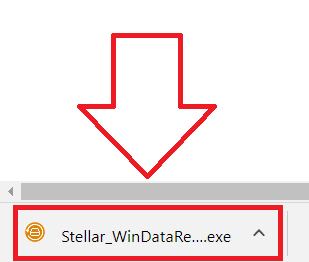
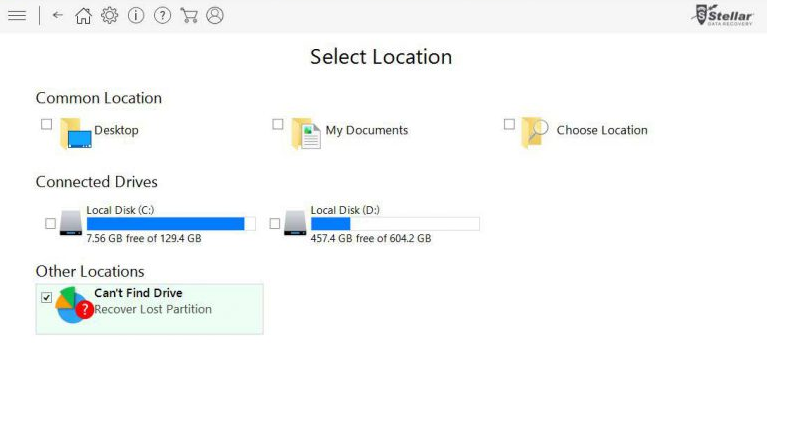
Step1: Download the software in the work-station by clicking on the “Download” button below.
Step2: Execute the installer by clicking on downloaded files.
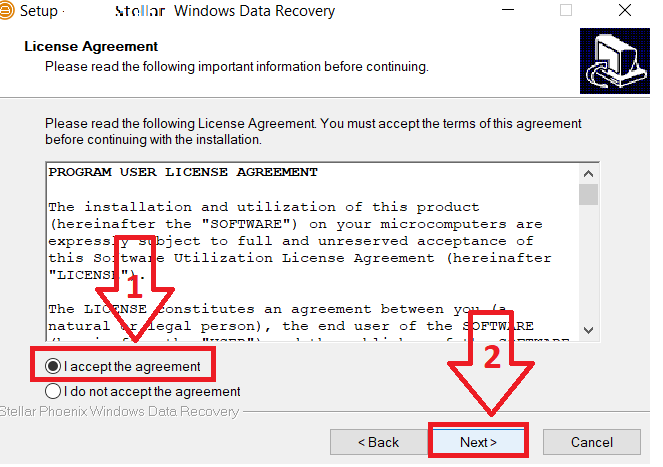
Step3: A license agreement page appears on the screen. Click on “Accept” to agree with its terms and use. Follow the on-screen instruction as mentioned and click on “Finish” button.
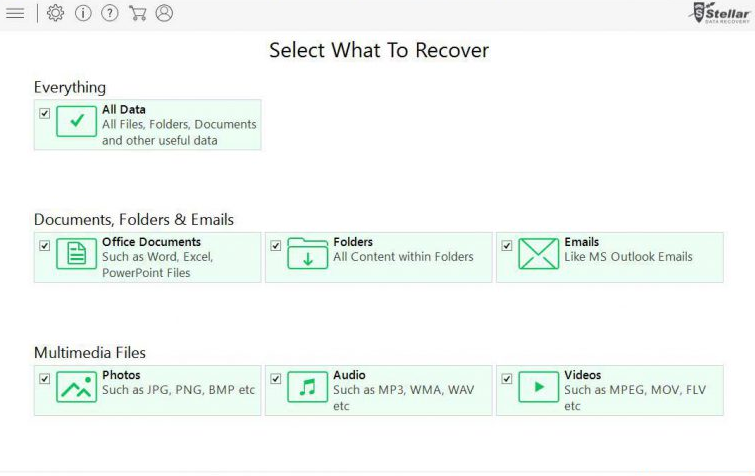
Step4: Once the installation gets completed, the program gets executed automatically. In the newly opened interface, select the file types that you want to recover and click on “Next”.
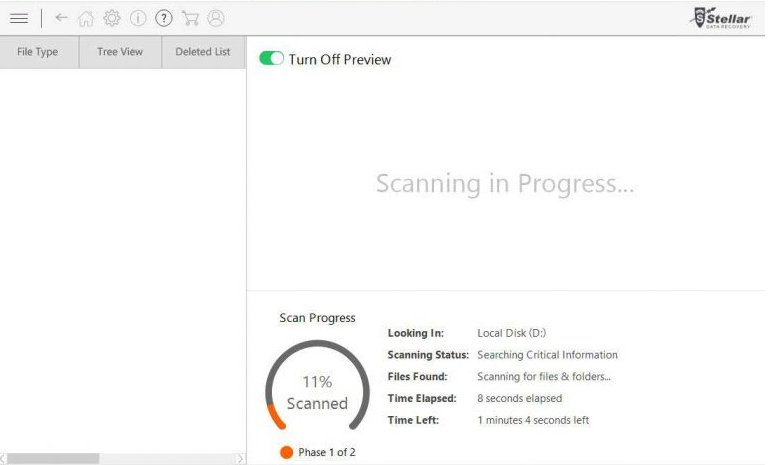
Step5: You can select the “Drives” on which you want the software to run and execute the recovery process. Next is to click on the “Scan” button.
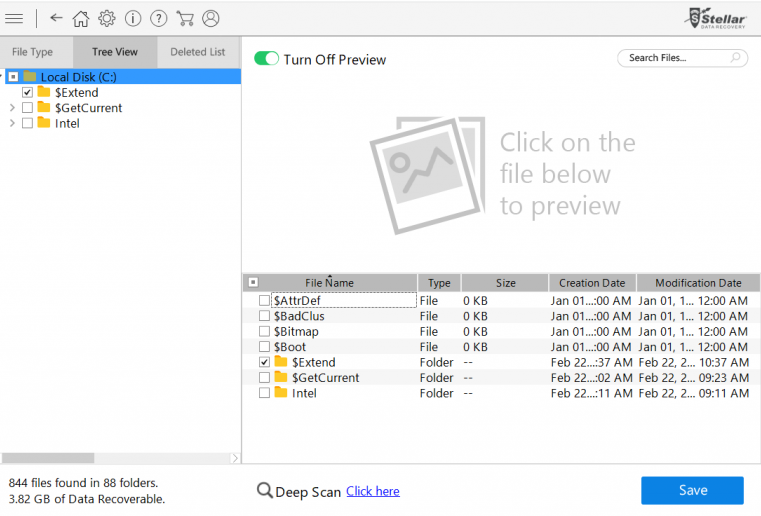
Step6: Based on drive you select for scanning, the restore process begins. The whole process may take time depending on the volume of the selected drive and number of files. Once the process gets completed, a data explorer appears on the screen with preview of that data that is to be recovered. Select the files that you want to restore.
Step7. Next is to locate the location where you want to saver the recovered files.
Special Offer (For Windows)
Cylance Ransomware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Data Recovery Offer
We Suggest you to choose your lately created backup files in order to restore your encrypted files, however in case if you don’t have any such backups, you can try a data recovery tool to check if you can restore your lost data.
Some Related FAQs
How can I open files encrypted by Cylance Ransomware? Can I access it myself?
A file that is locked by ransomware cannot be accessed unless it is first decrypted using the decryption key.
What could I do to access the locked files?
In case if you have backup files, use it and don’t worry about the files that got encrypted since you can use it from backup. However remember that in order to use the backup files on same PC, you first have to remove the ransomware infection completely otherwise the backup file will get encrypted as well. For removing the ransommare, it is suggested to use a powerful anti-malware tool.
In case if the backup is not available, you can try “Restore Point” to roll back the System to point where the PC was free from ransomware attack. If these options doesn’t works then you can try your luck with any powerful data recovery tool.
Additionally, there is high possibility that the encrypted files are still with you hence you can check all the possible locations such as sent or received emails, contact your friends, family members to get files like images, videos, etc. that would have shared earlier. Check your cloud storage and social media platforms, old devices including laptop, PC, mobile phones and so on.
Should I Pay Ransom in order to get decryption key?
It is never recommended to pay money because there is no guarantee of receiving the correct decryption key from cyber-criminals even after the ransom amount is paid. The identity of cyber-criminals are often key anonymous hence you cannot do anything much later.
Where can I report about the ransowmare attack?
There are cyber-security agencies in every country where you can report about ransomware attack. The links for the respective authorities are as follow. You can visit the link as per your country and report about the attack.
- USA– Internet Crime Complaint Centre IC3 or On Guard Online;
- In Canada- Canadian Anti-Fraud Centre;
- United Kingdom– Action Fraud
- Australia – Australian High Tech Crime Center
- In Ireland- An Garda Síochána
- Greece – Cyber Crime Unit (Hellenic Police)
- New Zealand- Consumer Affairs Scams
- Spain– Policía Nacional
- Poland– Policja
- Portugal– Polícia Judiciária
- France– Ministère de l’Intérieur
- Germany– Polizei
- Italy– Polizia di Stato
- The Netherlands– Politie
- India – CyberCrime Investigation Cell
Can Antivirus protect against ransomware?
A powerful antivirus can protect, detect as well as remove ransomware. It is always a good practice to use a security application in order to get protection from ransomware in real-time. Additionally, it is equally important to follow good cyber-security practices.