Remove ConfigType Adware From Mac
ConfigType: Complete Uninstall Guide
ConfigType is a potentially unwanted program (PUP) that generally sneaks into the Mac computers as an extension and affects the internet browsers such as Firefox, Chrome, MS Edge etc. The app is promoted as a useful tool that improves users’ web browsing experience by providing features such as enhanced search results, special deals and offers while online purchasing and so on. However, it is not more than just a notorious PC threat that can be categorized as both adware as well as a browser hijacker. Soon after infiltrating the Mac systems, it alters the default browser’s settings to promote fake search engine.
ConfigType Hijacks Internet Browsers:
ConfigType assigns its own perilous URL as the new search engine, home page and new tab preferences without seeking for any approval and grabs complete control over the entire browser. Speaking of the customized search tool, all search results provided by this engine are not genuine. Search results are all redirected to genuine ones like Yahoo, Google, Bing and others and are plagued with ads in the form of affiliated links. This nasty adware can affect not only its victims’ searches and the browsing experience but also negatively impact their privacy, since these PUPs gather a variety of user data in the background.
Potentially unwanted programs like ConfigType, ExploreActivity and others are created on regular basis and they are particularly common in nature. They serve as an easy way to monetize on people’s clicks and ad exposure. It displays thousands of annoying ads and pop-ups all over the day and interrupts users’ web sessions badly. These ads are in various formats such as banners, coupons, deals, discounts, offers etc. They are based on pay-per-click scheme and earn profits for the developers when clicked. However, clicking on these adverts might expose you to malware-laced sites that host spyware, trojan, ransomware and other dangerous cyber threats.
ConfigType is able to monitor users’ web activities and collect browsing-related information such as entered search queries, URLs of accessed domains, IP addresses, geolocations and can also steal personal data like banking and credit card details. The collected data is later on sold to third-parties and can be employed for producing target advertisements and generating revenues. This nasty threat messes with vital system files which assure efficient PC functioning and prevents many running apps as well as drivers from working in a proper manner. And so, a quick ConfigType removal is highly required from the Mac computer.
PUPs Are Spread Via Bundling Technique:
Potentially unwanted programs are typically distributed via software bundling method, which often results in unintentional installation from the users’ side. It is easier to avoid PUPs altogether than you might think. All you have to do is be very careful during the installation of freeware programs that you download from third party websites and be overall more attentive about what you install on your work-station. It is helpful to read app reviews and blog posts before downloading/installing any software.
To prevent the unintentional installation of unwanted applications, you should always select the Advanced or Custom installation settings if such is provided rather than the Recommended or Quick one. The earlier ones would allow you to stay in control of the process from start to finish. Also, be aware of pre-ticked boxes, fine print text, misleading button placements, and other tricks that might be used by app authors and distributors. But at the moment, you must remove ConfigType from the Mac PC without wasting any time.
Special Offer (For Macintosh)
ConfigType can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful antimalware scanner to help you getting rid of this virus
Remove Files and Folders Related to ConfigType
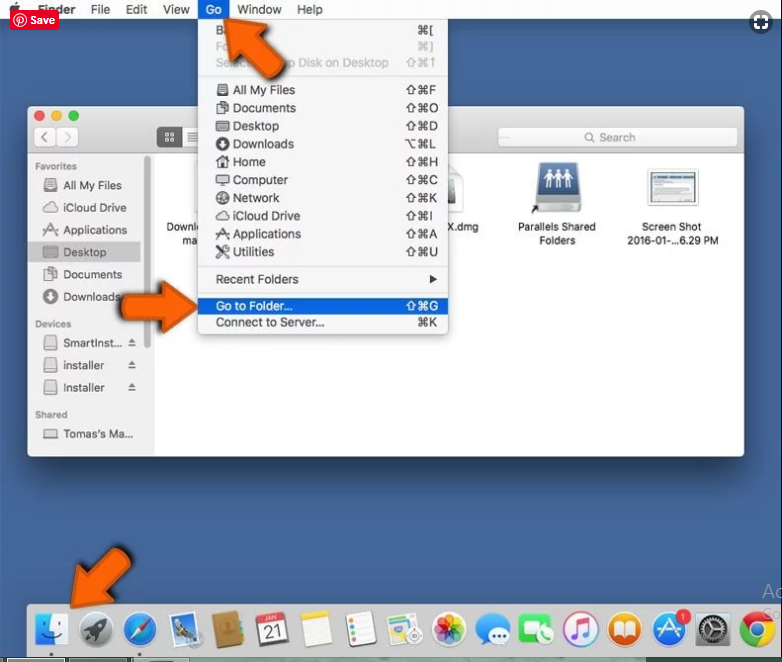
Open the “Menu” bar and click the “Finder” icon. Select “Go” and click on “Go to Folder…”
Step 1: Search the suspicious and doubtful malware generated files in /Library/LaunchAgents folder
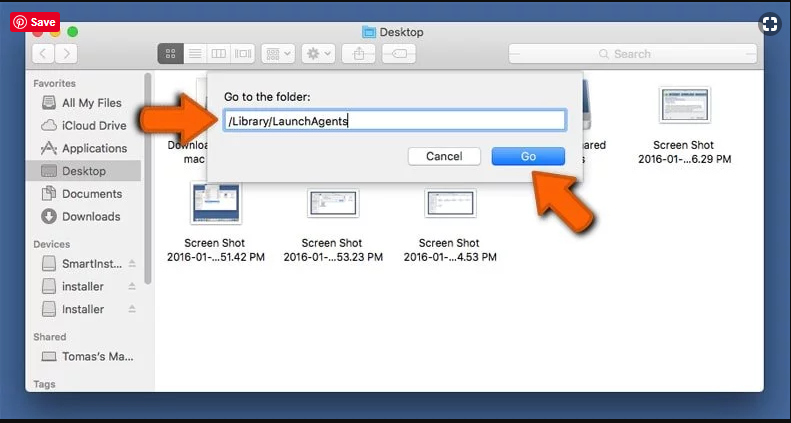
Type /Library/LaunchAgents in the “Go to Folder” option
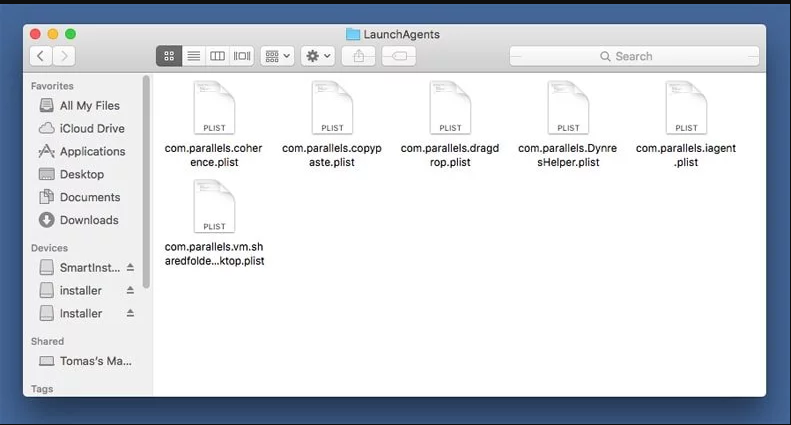
In the “Launch Agent” folder, search for all the files that you have recently downloaded and move them to “Trash”. Few of the examples of files created by browser-hijacker or adware are as follow, “myppes.download.plist”, “mykotlerino.Itvbit.plist”, installmac.AppRemoval.plist”, and “kuklorest.update.plist” and so on.
Step 2: Detect and remove the files generated by the adware in “/Library/Application” Support folder
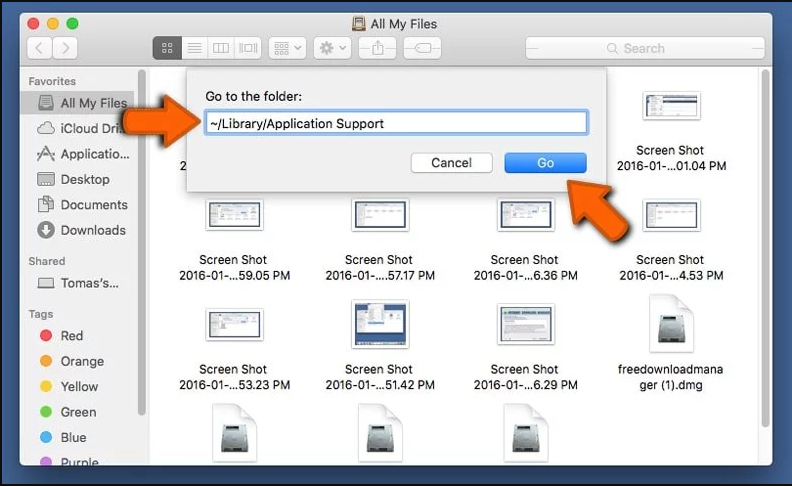
In the “Go to Folder..bar”, type “/Library/Application Support”
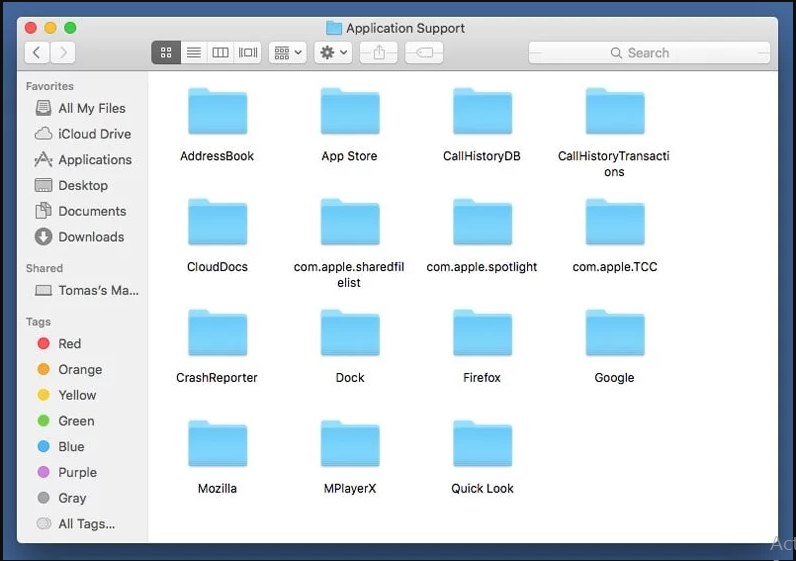
Search for any suspicious newly added folders in “Application Support” folder. If you detect any one of these like “NicePlayer” or “MPlayerX” then send them to “Trash” folder.
Step 3: Look for the files generated by malware in /Library/LaunchAgent Folder:
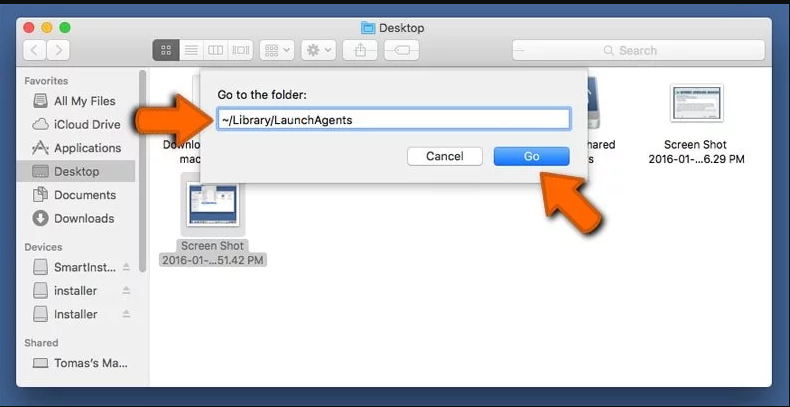
Go to Folder bar and type /Library/LaunchAgents
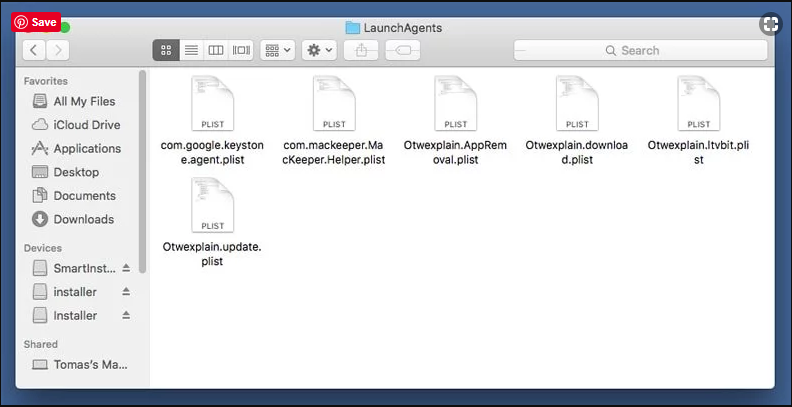
You are in the “LaunchAgents” folder. Here, you have to search for all the newly added files and move them to “Trash” if you find them suspicious. Some of the examples of suspicious files generated by malware are “myppes.download.plist”, “installmac.AppRemoved.plist”, “kuklorest.update.plist”, “mykotlerino.ltvbit.plist” and so on.
Step4: Go to /Library/LaunchDaemons Folder and search for the files created by malware
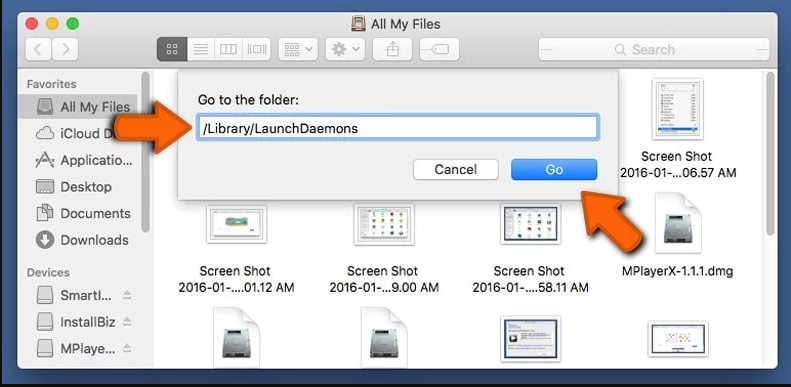
Type /Library/LaunchDaemons in the “Go To Folder” option
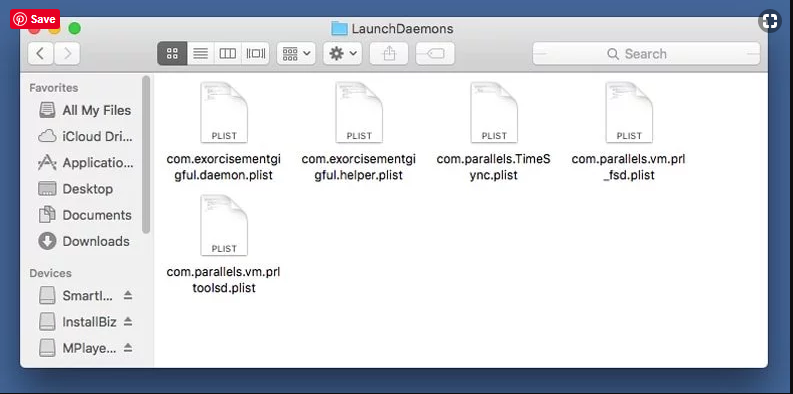
In the newly opened “LaunchDaemons” folder, search for any recently added suspicious files and move them to “Trash”. Examples of some of the suspicious files are “com.kuklorest.net-preferences.plist”, “com.avickUpd.plist”, “com.myppes.net-preference.plist”, “com.aoudad.net-preferences.plist” and so on.
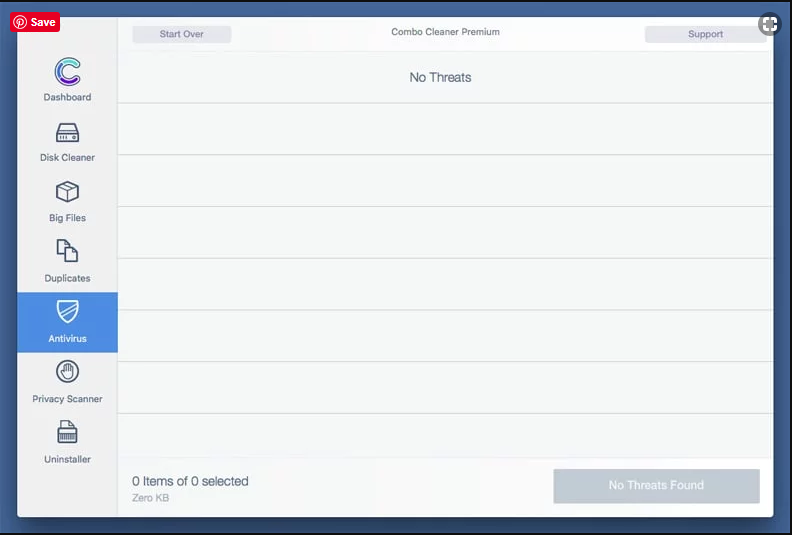
Step 5: Use Combo Cleaner Anti-Malware and Scan your Mac PC
The malware infections could be removed from the Mac PC if you execute all the steps mentioned above in the correct way. However, it is always advised to be sure that your PC is not infected. It is suggested to scan the work-station with “Combo Cleaner Anti-virus”.
Special Offer (For Macintosh)
ConfigType can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful antimalware scanner to help you getting rid of this virus
Once the file gets downloaded, double click on combocleaner.dmg installer in the newly opened window. Next is to open the “Launchpad” and press on “Combo Cleaner” icon. It is advised to wait until “Combo Cleaner” updates the latest definition for malware detection. Click on “Start Combo Scan” button.
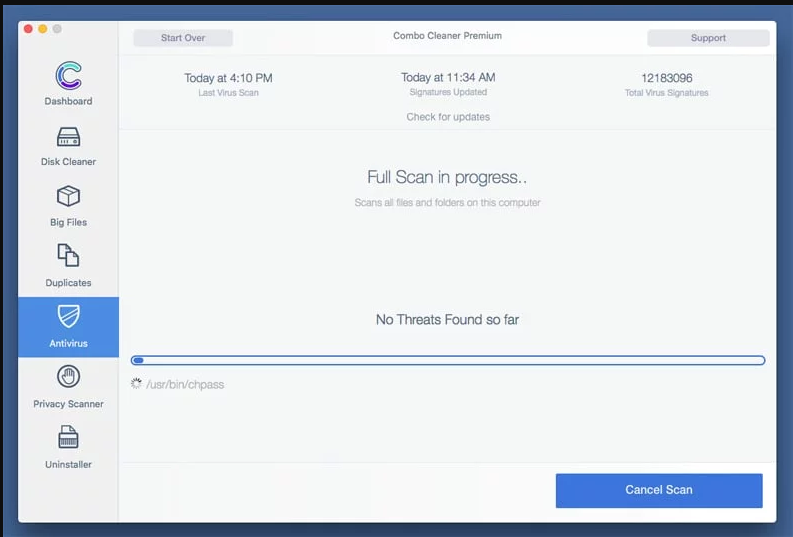
A depth scan of your Mac PC will be executed in order to detect malware. If the Anti-virus scan report says “no threat found” then you can continue with guide further. On the other hand, it is recommended to delete the detected malware infection before continuing.
Now the files and folders created by the adware is removed, you have to remove the rogue extensions from the browsers.
Remove ConfigType from Internet Browsers
Delete Doubtful and Malicious Extension from Safari
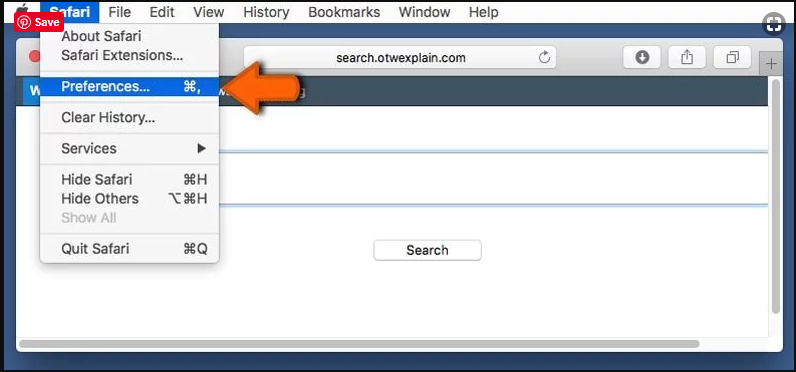
Go to “Menu Bar” and open “Safari” browser. Select “Safari” and then “Preferences”
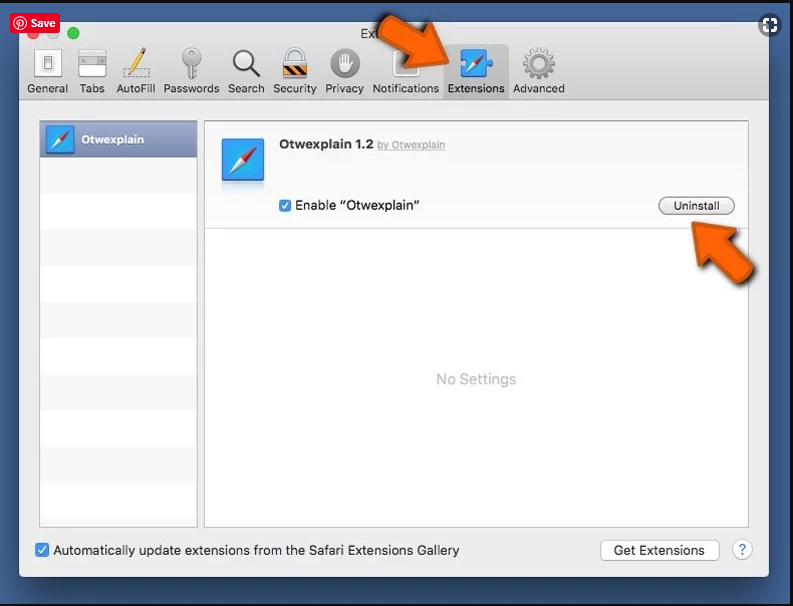
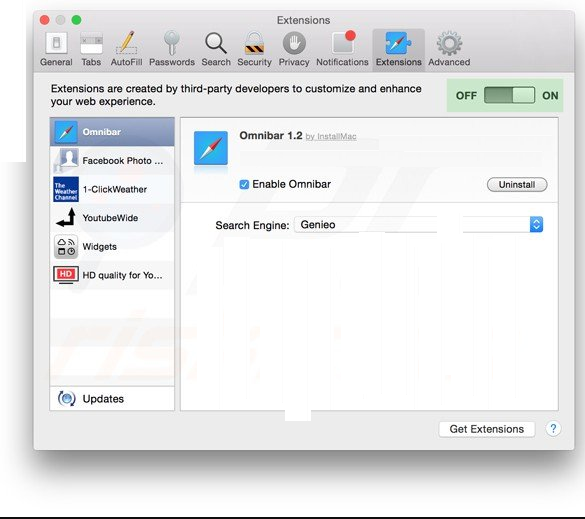
In the opened “preferences” window, select “Extensions” that you have recently installed. All such extensions should be detected and click the “Uninstall” button next to it. If you are doubtful then you can remove all the extensions from “Safari” browser as none of them are important for smooth functionality of the browser.
In case if you continue facing unwanted webpage redirections or aggressive advertisements bombarding, you can reset the “Safari” browser.
“Reset Safari”
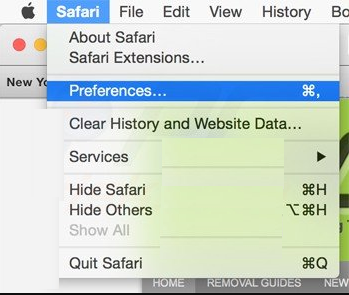
Open the Safari menu and choose “preferences…” from the drop-down menu.
Go to the “Extension” tab and set the extension slider to “Off” position. This disables all the installed extensions in the Safari browser
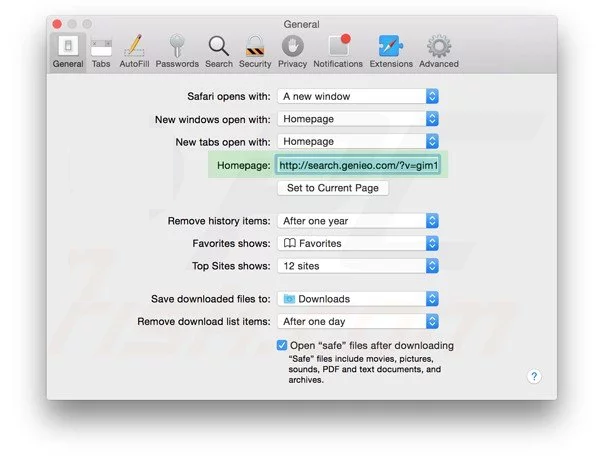
Next step is to check the homepage. Go to “Preferences…” option and choose “General” tab. Change the homepage to your preferred URL.
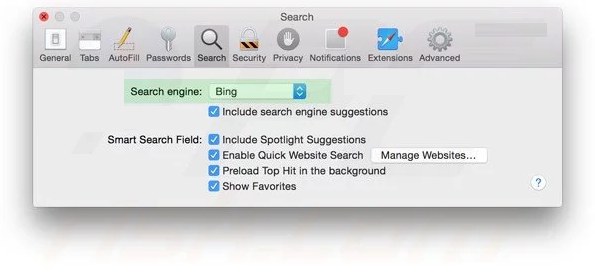
Also check the default search-engine provider settings. Go to “Preferences…” window and select the “Search” tab and select the search-engine provider that you want such as “Google”.
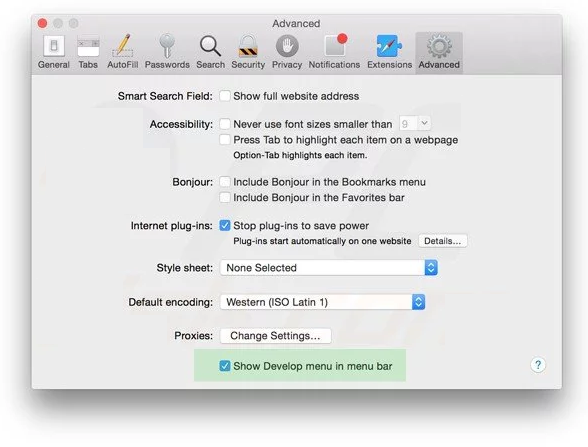
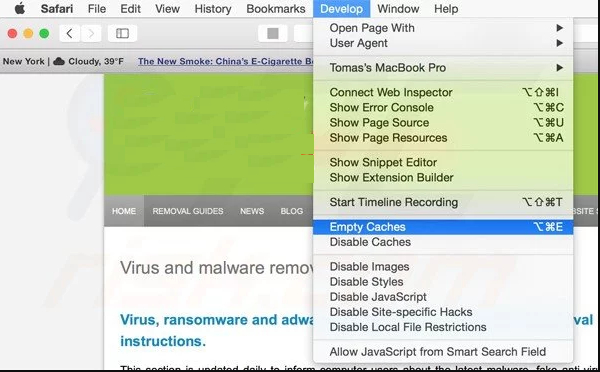
Next is to clear the Safari browser Cache- Go to “Preferences…” window and select “Advanced” tab and click on “Show develop menu in the menu bar.“
Go to “Develop” menu and select “Empty Caches”.
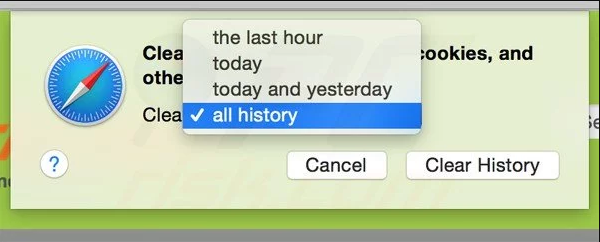
Remove website data and browsing history. Go to “Safari” menu and select “Clear History and Website Data”. Choose “all history” and then click on “Clear History”.
Remove Unwanted and Malicious Plug-ins from Mozilla Firefox
Delete ConfigType add-ons from Mozilla Firefox
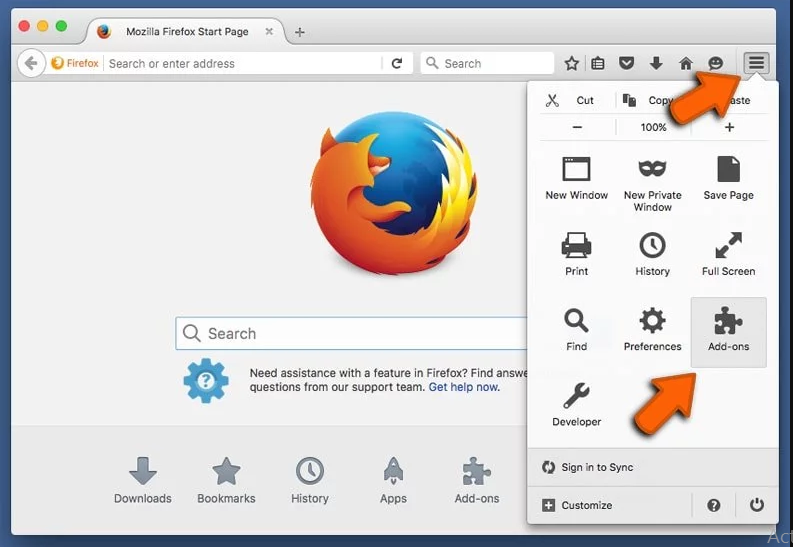
Open the Firefox Mozilla browser. Click on the “Open Menu” present in the top right corner of the screen. From the newly opened menu, choose “Add-ons”.
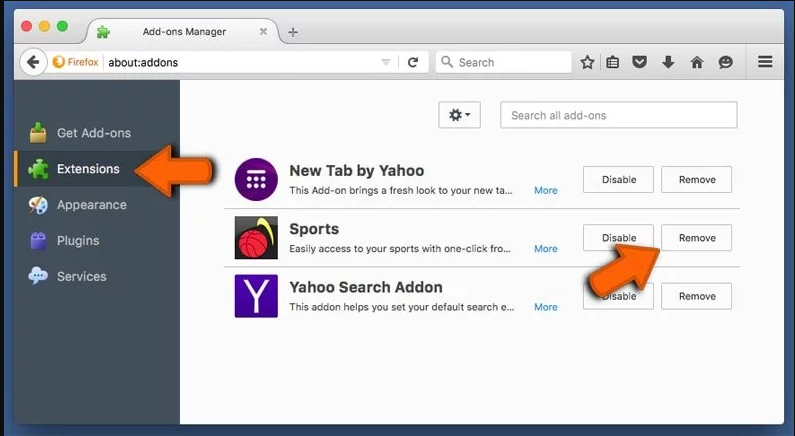
Go to “Extension” option and detect all the latest installed add-ons. Select each of the suspicious add-ons and click on “Remove” button next to them.
In case if you want to “reset” the Mozilla Firefox browser then follow the steps that has been mentioned below.
Reset Mozilla Firefox Settings
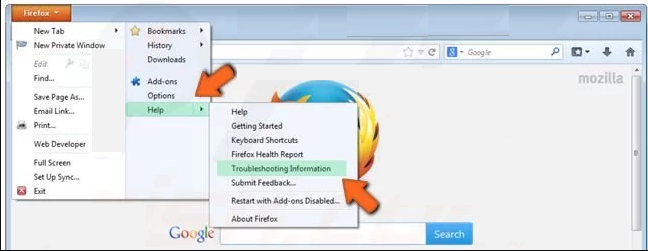
Open the Firefox Mozilla browser and click on “Firefox” button situated at the top left corner of the screen.

In the new menu, go to “Help” sub-menu and choose “Troubleshooting Information”
In the “Troubleshooting Information” page, click on “Reset Firefox” button.
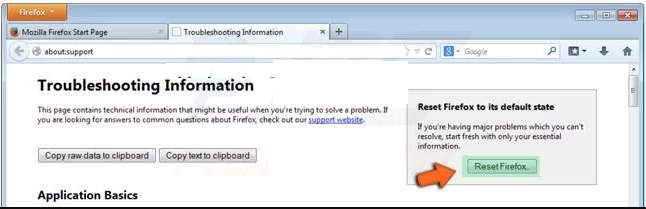
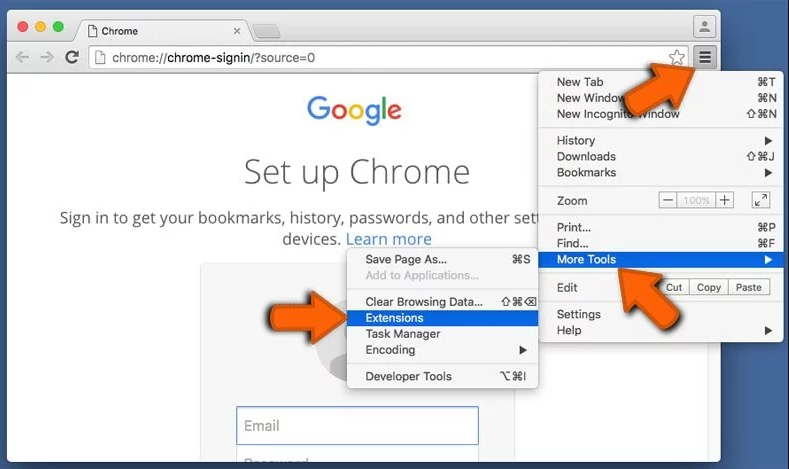
Confirm that you want to reset the Mozilla Firefox settings to default by pressing on “Reset Firefox” option
The browser will get restarted and the settings changes to factory default
Delete Unwanted and Malicious Extensions from Google Chrome
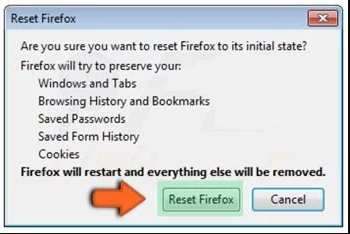
Open the chrome browser and click on “Chrome menu”. From the drop down option, choose “More Tools” and then “Extensions”.
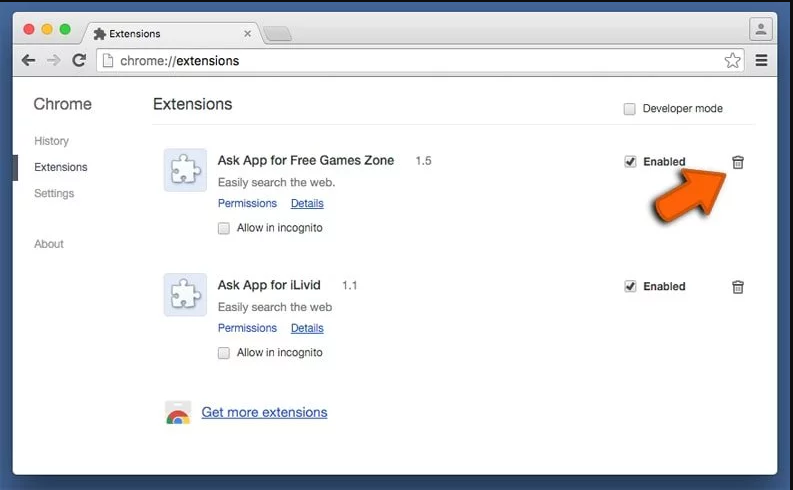
In the “Extensions” option, search for all the recently installed add-ons and extensions. Select them and choose “Trash” button. Any third-party extension is not important for the smooth functionality of the browser.
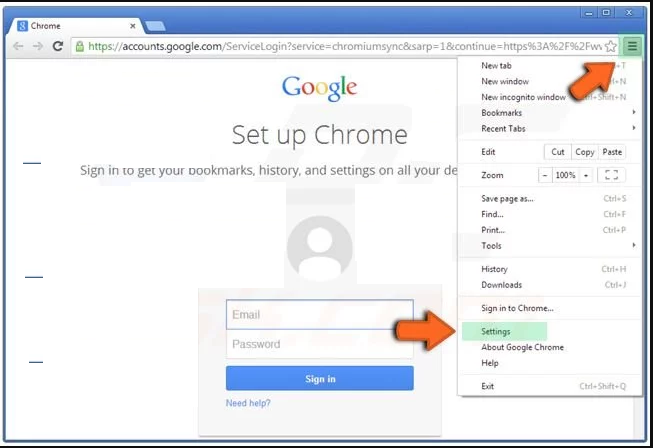
Reset Google Chrome Settings
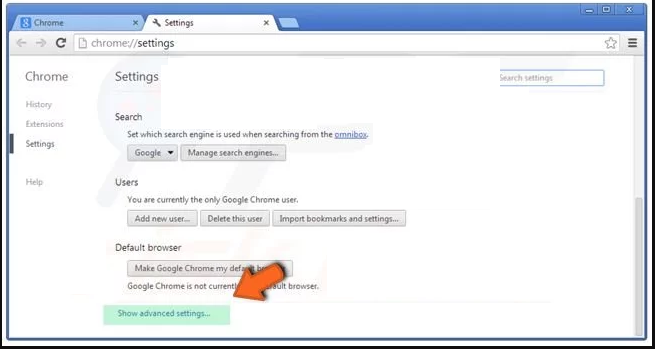
Open the browser and click on three line bar at the top right side corner of the window.
Go to the bottom of the newly opened window and select “Show advanced settings”.
In the newly opened window, scroll down to the bottom and choose “Reset browser settings”
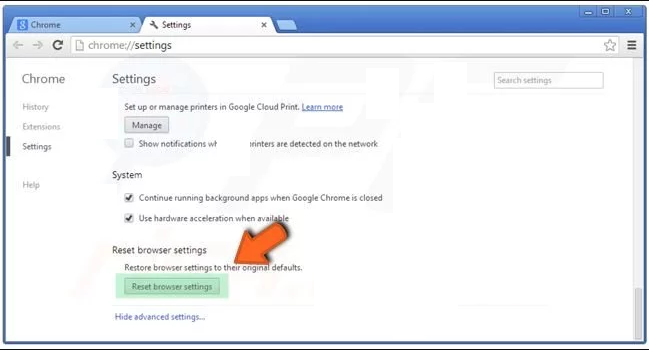
Click on the “Reset” button on the opened “Reset browser settings” window
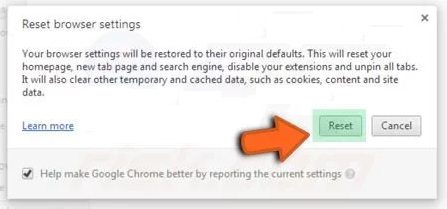
Restart the browser and the changes you get will be applied
The above mentioned manual process should be executed as it is mentioned. It is a cumbersome process and requires a lot of technical expertise. And hence it is advised for technical experts only. To be sure that your PC is free from malware, it is better that you scan the work-station with a powerful anti-malware tool. The automatic malware removal application is preferred because it doesn’t requires any additional technical skills and expertise.
Special Offer (For Macintosh)
ConfigType can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful antimalware scanner to help you getting rid of this virus
Download the application and execute it on the PC to begin the depth scanning. Once the scanning gets completed, it shows the list of all the files related to ConfigType. You can select such harmful files and folders and remove them immediately.