How To Remove TroyStealer Trojan
Simple Steps To Delete TroyStealer
TroyStealer is one more hazardous PC virus designed by a team of vicious Cyber criminals for evil purposes. As name suggests, it’s a hazardous software which is used to steal various types of data and information. This precarious trojan often gets into the targeted computer without users’ permission and then conducts a series of vicious activities in the background. It injects spying cookies on your Internet browsers and constantly monitors your Online activities like your search queries, pages viewed, links opened etc. It steals your personal data relating to banking and other financial details and exposes them to hackers for evil purposes. Cyber actors can misuse your sensitive data for generating illicit profits and cause you to suffer a big financial loss.
Know More About TroyStealer:
According to the reports, TroyStealer targets mostly targets Portuguese users but can also affect people from other regions too. It also records data regarding users’ interests, needs and other preferences which is then utilized by the advertisers for advertisement campaign. And hence, due to its presence, you are bombarded with thousands of intrusive ads and pop-ups all over the day that makes your Online browsing very complex and problematic. These ads look very attractive and can easily gain your attention. They include sponsored links and once you click on them, you are redirected to sites where numerous third-party products and services are promoted. TroyStealer virus might redirect you to malware-laden sites that are filled with malicious contents and cause more hazards to your computer.
Intrusion of TroyStealer:
Such kind of trojan viruses are mostly spread through spam emails campaigns. These emails are in Portuguese and claim that the senders have supposedly tried to send a payment to the recipient’s banking account. However, due to the provided banking information being incorrect, the transaction did not succeed. And hence, recipients are asked to review the details in the attached file and fix mistakes, so that the payment could be successful. Once the file is opened or run or executed, it initiates the infection process to this precarious trojan.
Tips To Prevent Such Attacks:
Such types of malware are designed in a way that they can hardly be noticed when it tries to enter the work-station. However, you should do various things to avoid installation of such threats. First of all, install a reliable anti-spyware and always keep it up-to-date. Avoid visiting deceptive websites because they are actively used for spreading such infections. Moreover, stay away from ads that are offering free tools updates because there is an immense possibility that they will infect your PC with either PU P or virus. Additionally, ignore suspicious emails that are clearly filled with suspicious attachments or links. Delete such mails as early as possible.
Summarize Information
Name– TroyStealer
Category– Trojan, password-stealing virus, spyware, banking malware
Description– Steal users’ sensitive data for adverting purpose and also to generate illicit revenues by misusing those details, Disables all the running security measures of the infected PC and drop more infections in the machine as well as help the criminals to get access to system.
Symptoms– Slowness of system’s performance, fake error messages, security alerts, intrusive ads and pop-ups, unwanted redirects to questioning sites and so on.
Distribution– Spam email campaigns, malicious file downloads, P2P file sharing, and many more.
Removal– Manual and automatic guidelines as provided under this article
Other Harmful Features of TroyStealer:
TroyStealer keeps performing malevolent acts in the background all the time which consumes enormous amount of memory resources and downgrades the overall PC performance severely. It causes the device to respond in a very slow manner and take more than usual time to complete any task. This nasty trojan changes the default registry settings by making spiteful entries in it which allows the virus to get automatically activated every time the device is started. It messes with vital system files that are efficient for smooth computer functioning and prevents many installed apps as well as drivers from working in an appropriate manner. It assists emote criminals to get access to your system and contribute malevolent deeds inside for their delicate welfare. It displays fake security warnings, error messages, update notifications etc. and tries to scam you into installing bogus software. Looking at all these threats, you are strongly recommended to remove TroyStealer from the PC without wasting any time.
Special Offer (For Windows)
TroyStealer can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Special Offer (For Macintosh) If you are a Mac user and TroyStealer has affected it, then you can download free antimalware scanner for Mac here to check if the program works for you.
Antimalware Details And User Guide
Click Here For Windows Click Here For Mac
Important Note: This malware asks you to enable the web browser notifications. So, before you go the manual removal process, execute these steps.
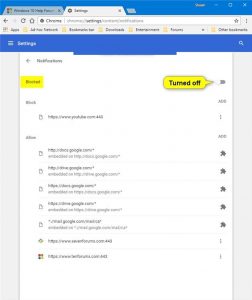
Google Chrome (PC)
- Go to right upper corner of the screen and click on three dots to open the Menu button
- Select “Settings”. Scroll the mouse downward to choose “Advanced” option
- Go to “Privacy and Security” section by scrolling downward and then select “Content settings” and then “Notification” option
- Find each suspicious URLs and click on three dots on the right side and choose “Block” or “Remove” option
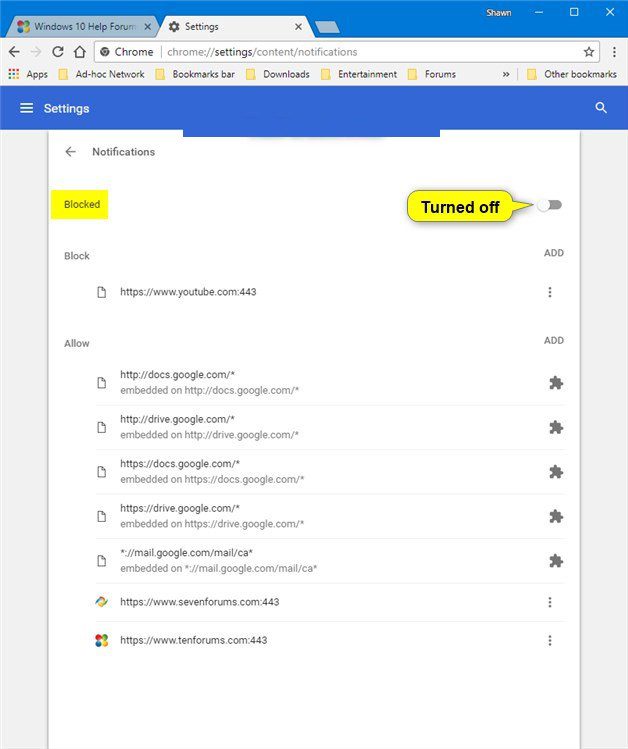
Google Chrome (Android)
- Go to right upper corner of the screen and click on three dots to open the menu button and then click on “Settings”
- Scroll down further to click on “site settings” and then press on “notifications” option
- In the newly opened window, choose each suspicious URLs one by one
- In the permission section, select “notification” and “Off” the toggle button
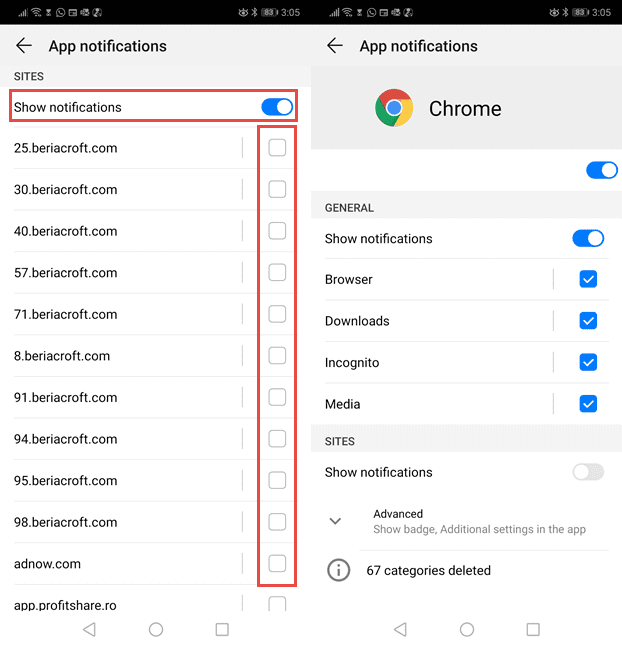
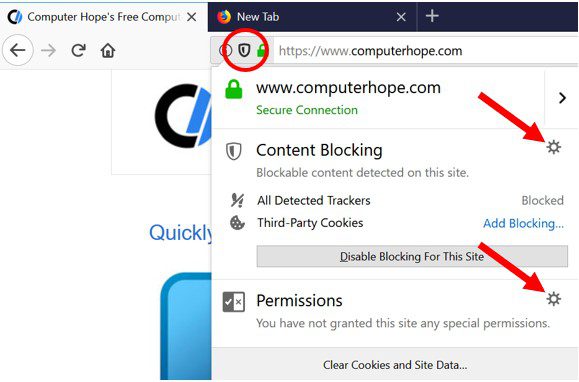
Mozilla Firefox
- On the right corner of the screen, you will notice three dots which is the “Menu” button
- Select “Options” and choose “Privacy and Security” in the toolbar present in the left side of the screen
- Slowly scroll down and go to “Permission” section then choose “Settings” option next to “Notifications”
- In the newly opened window, select all the suspicious URLs. Click on the drop-down menu and select “Block”
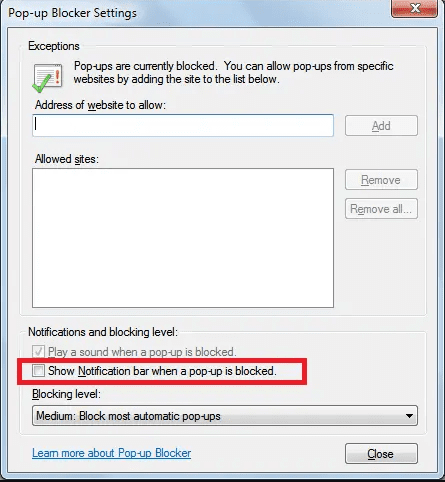
Internet Explorer
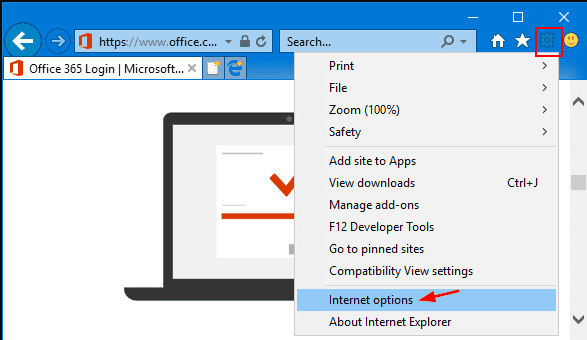
- In the Internet Explorer window, select the Gear button present on the right corner
- Choose “Internet Options”
- Select “Privacy” tab and then “Settings” under the “Pop-up Blocker” section
- Select all the suspicious URLs one by one and click on the “Remove” option
Microsoft Edge
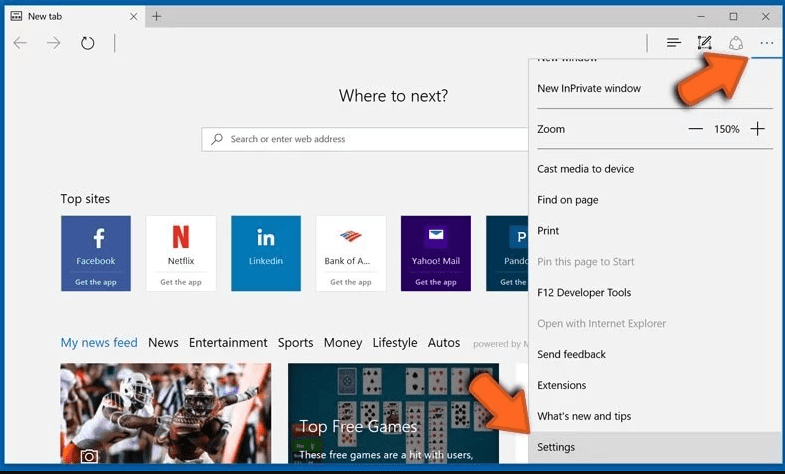
- Open the Microsoft Edge and click on the three dots on the right corner of the screen to open the menu
- Scroll down and select “Settings”
- Scroll down further to choose “view advanced settings”
- In the “Website Permission” option, click on “Manage” option
- Click on switch under every suspicious URL
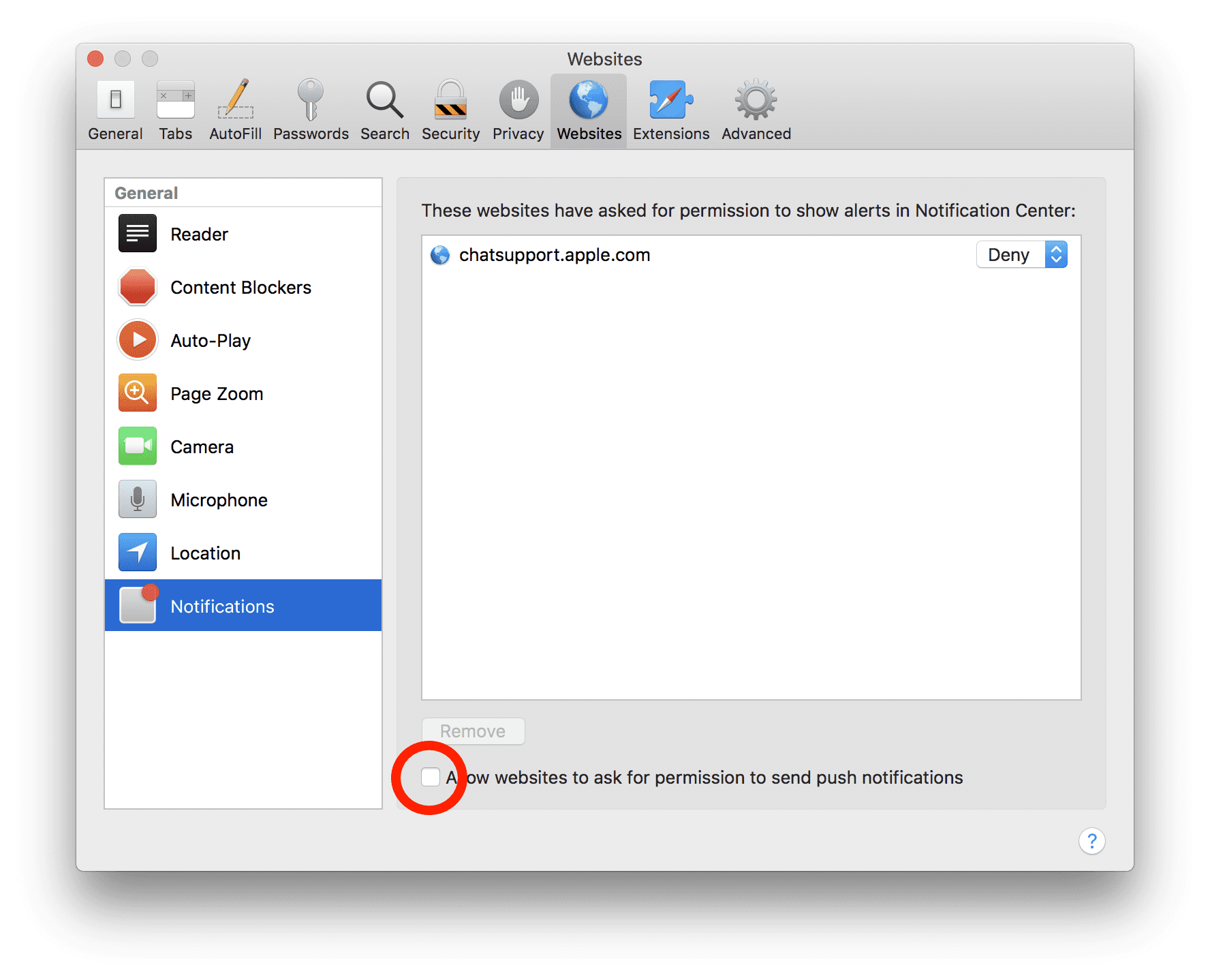
Safari (Mac):
- On the upper right side corner, click on “Safari” and then select “Preferences”
- Go to “website” tab and then choose “Notification” section on the left pane
- Search for the suspicious URLs and choose “Deny” option for each one of them
Manual Steps to Remove TroyStealer:
Remove the related items of TroyStealer using Control-Panel
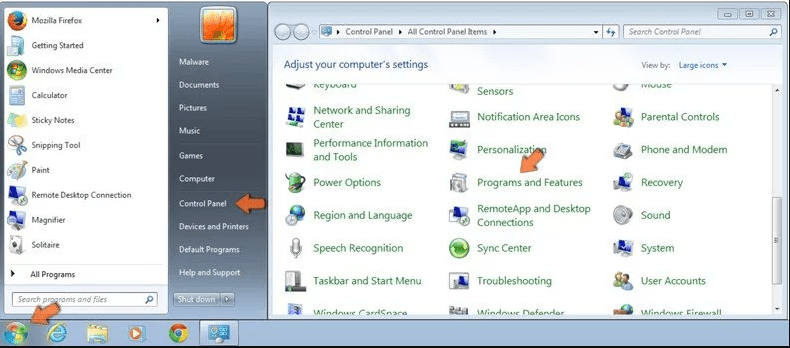
Windows 7 Users
Click “Start” (the windows logo at the bottom left corner of the desktop screen), select “Control Panel”. Locate the “Programs” and then followed by clicking on “Uninstall Program”
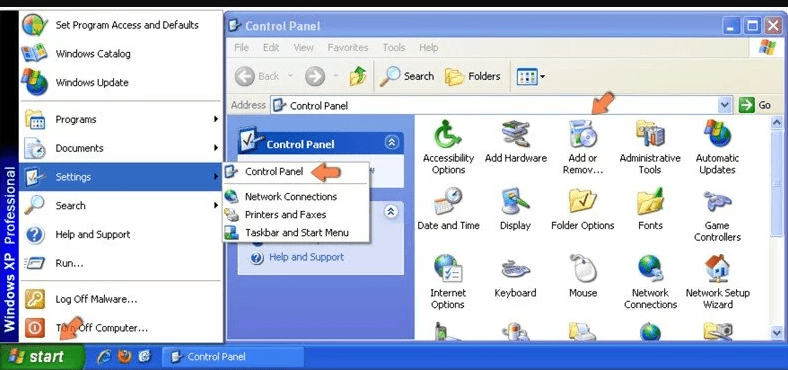
Windows XP Users
Click “Start” and then choose “Settings” and then click “Control Panel”. Search and click on “Add or Remove Program’ option
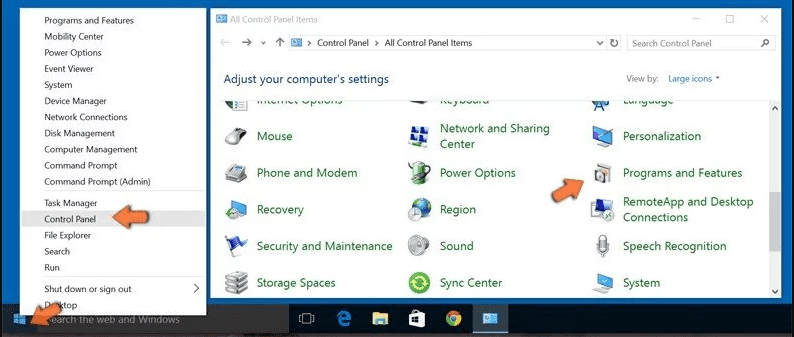
Windows 10 and 8 Users:
Go to the lower left corner of the screen and right-click. In the “Quick Access” menu, choose “Control Panel”. In the newly opened window, choose “Program and Features”
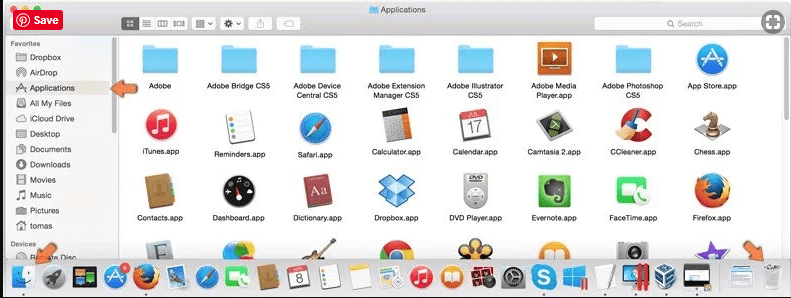
Mac OSX Users
Click on “Finder” option. Choose “Application” in the newly opened screen. In the “Application” folder, drag the app to “Trash”. Right click on the Trash icon and then click on “Empty Trash”.
In the uninstall programs window, search for the PUAs. Choose all the unwanted and suspicious entries and click on “Uninstall” or “Remove”.
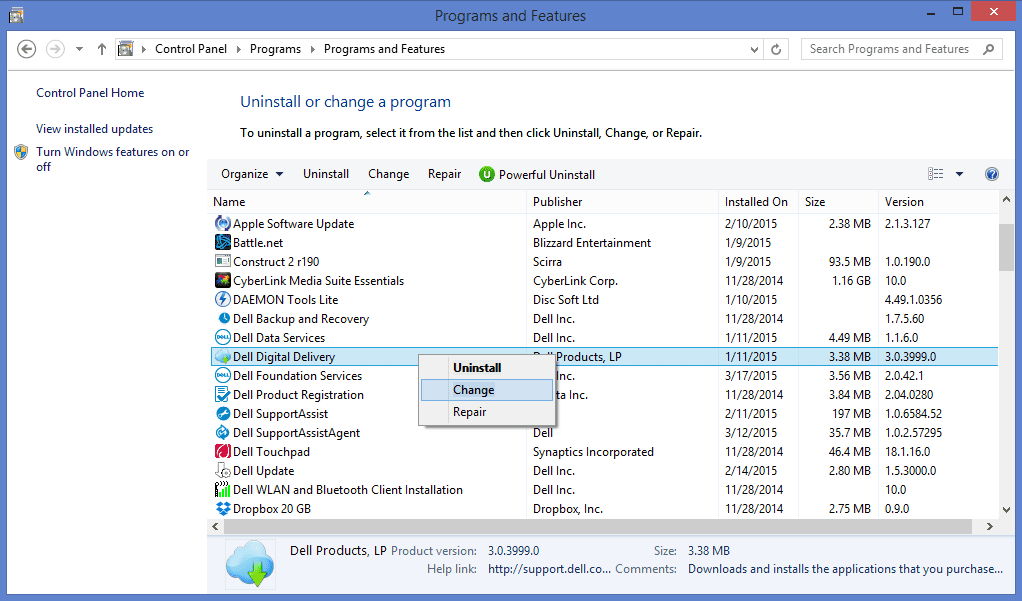
After you uninstall all the potentially unwanted program causing TroyStealer issues, scan your computer with an anti-malware tool for any remaining PUPs and PUAs or possible malware infection. To scan the PC, use the recommended the anti-malware tool.
Special Offer (For Windows)
TroyStealer can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Special Offer (For Macintosh) If you are a Mac user and TroyStealer has affected it, then you can download free antimalware scanner for Mac here to check if the program works for you.
How to Remove Adware (TroyStealer) from Internet Browsers
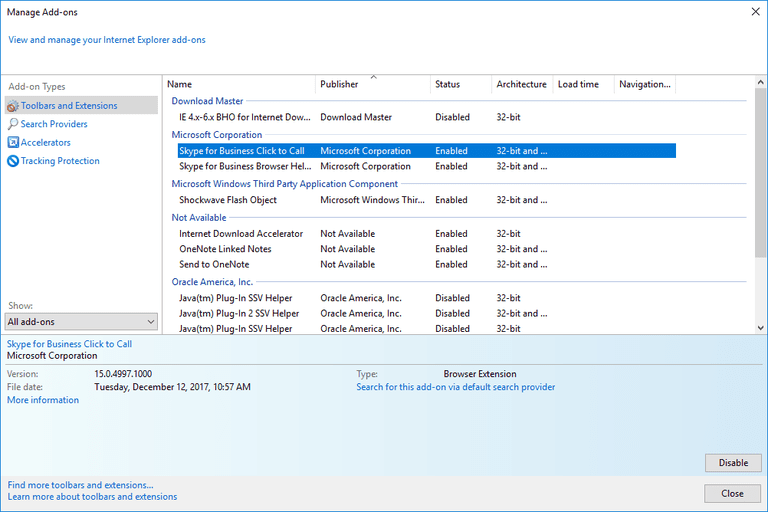
Delete malicious add-ons and extensions from IE
Click on the gear icon at the top right corner of Internet Explorer. Select “Manage Add-ons”. Search for any recently installed plug-ins or add-ons and click on “Remove”.
Additional Option
If you still face issues related to TroyStealer removal, you can reset the Internet Explorer to its default setting.
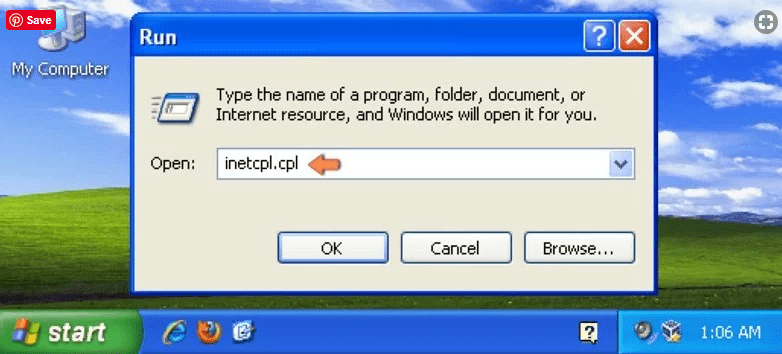
Windows XP users: Press on “Start” and click “Run”. In the newly opened window, type “inetcpl.cpl” and click on the “Advanced” tab and then press on “Reset”.
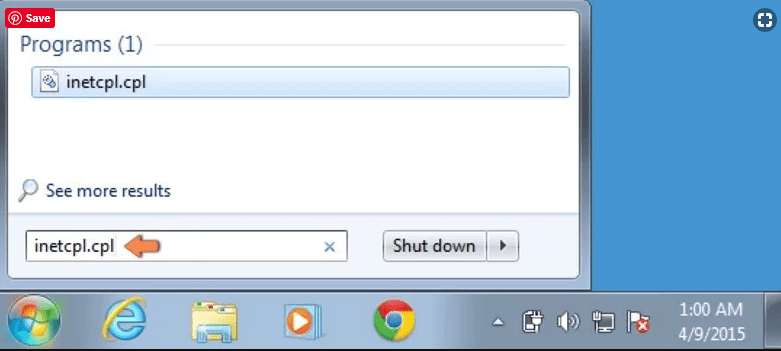
Windows Vista and Windows 7 Users: Press the Windows logo, type inetcpl.cpl in the start search box and press enter. In the newly opened window, click on the “Advanced Tab” followed by “Reset” button.
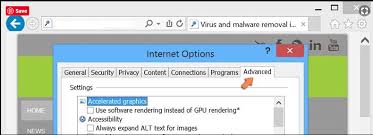
For Windows 8 Users: Open IE and click on the “gear” icon. Choose “Internet Options”
Select the “Advanced” tab in the newly opened window
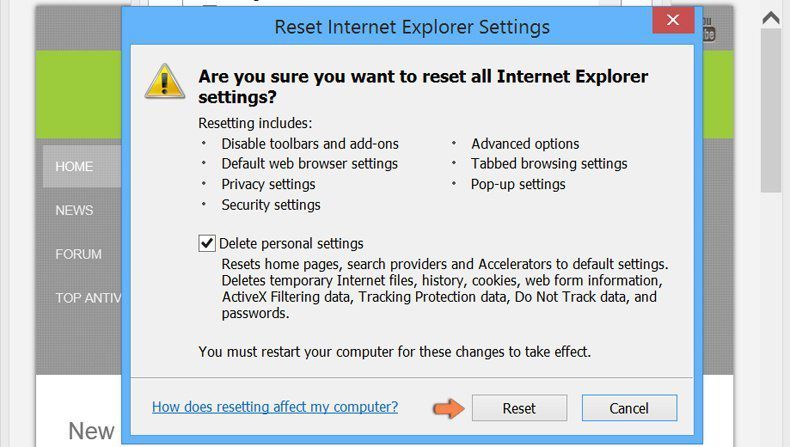
Press on “Reset” option
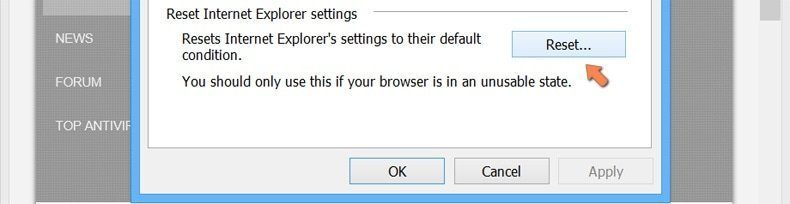
You have to press on the “Reset” button again to confirm that you really want to reset the IE
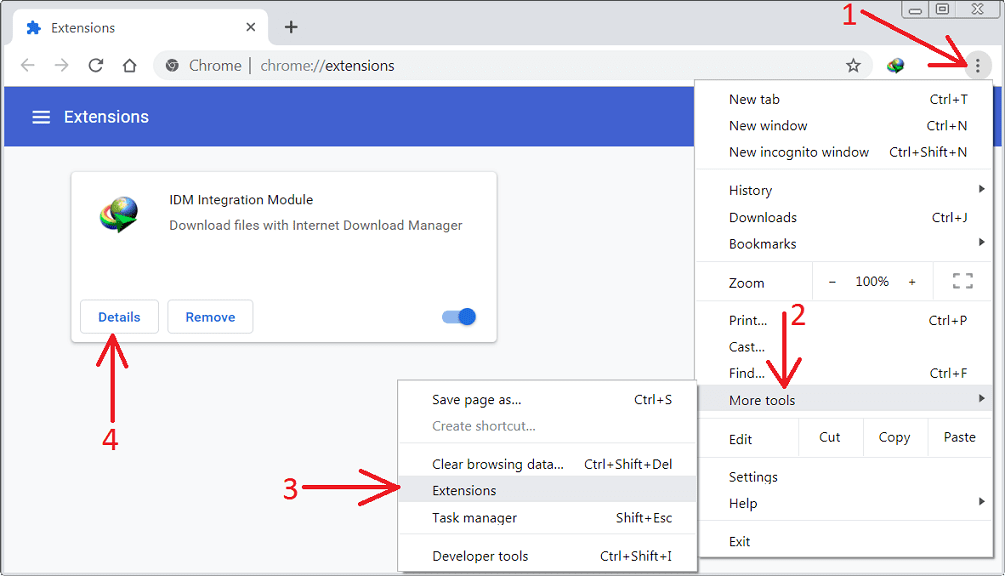
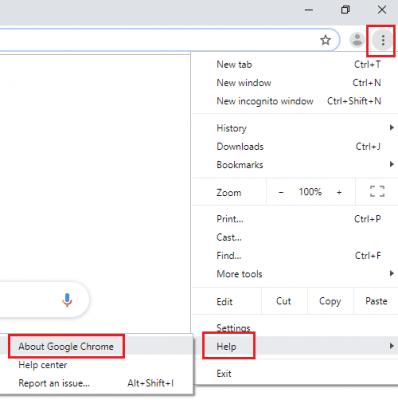
Remove Doubtful and Harmful Extension from Google Chrome
Go to menu of Google Chrome by pressing on three vertical dots and select on “More tools” and then “Extensions”. You can search for all the recently installed add-ons and remove all of them.
Optional Method
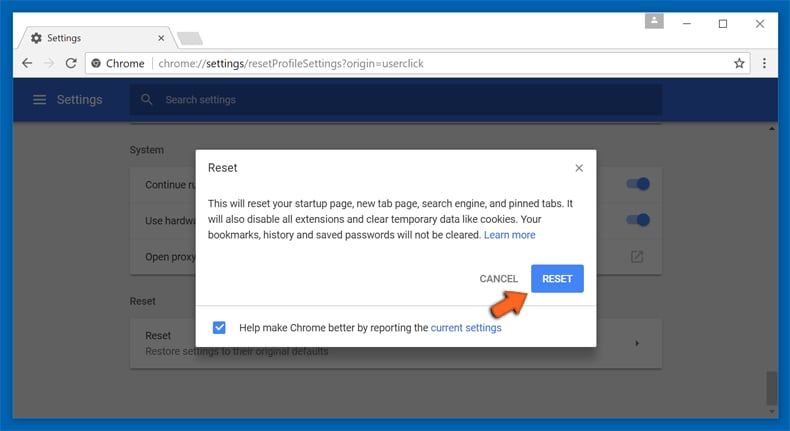
If the problems related to TroyStealer still persists or you face any issue in removing, then it is advised that your reset the Google Chrome browse settings. Go to three dotted points at the top right corner and choose “Settings”. Scroll down bottom and click on “Advanced”.
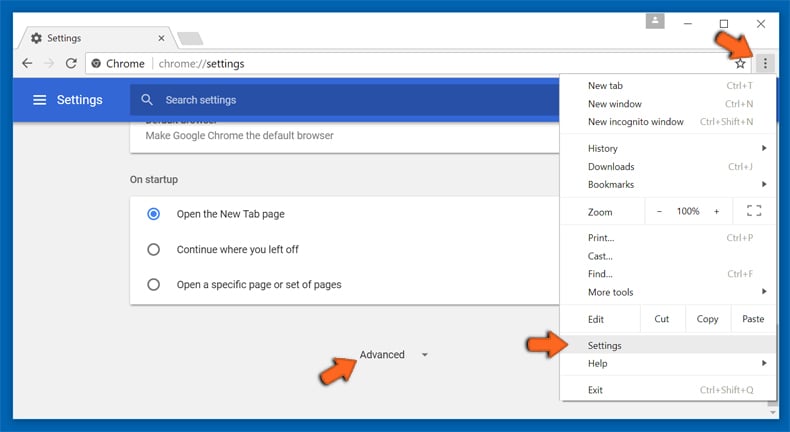
At the bottom, notice the “Reset” option and click on it.
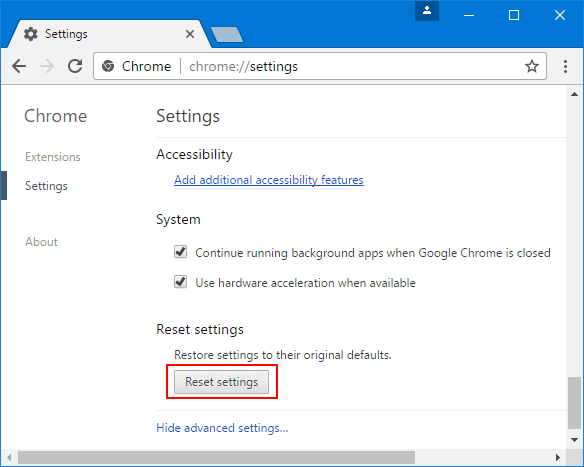
In the next opened window, confirm that you want to reset the Google Chrome settings by click on the “Reset” button.
Remove TroyStealer plugins (including all other doubtful plug-ins) from Firefox Mozilla
Open the Firefox menu and select “Add-ons”. Click “Extensions”. Select all the recently installed browser plug-ins.
Optional Method
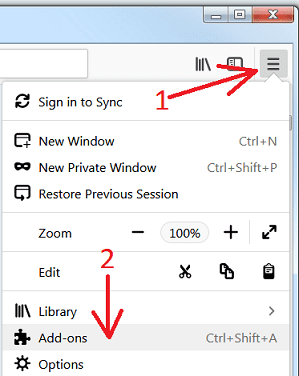
If you face problems in TroyStealer removal then you have the option to rese the settings of Mozilla Firefox.
Open the browser (Mozilla Firefox) and click on the “menu” and then click on “Help”.
Choose “Troubleshooting Information”
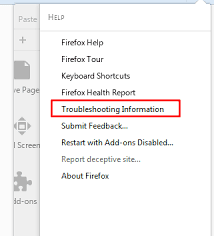
In the newly opened pop-up window, click “Refresh Firefox” button
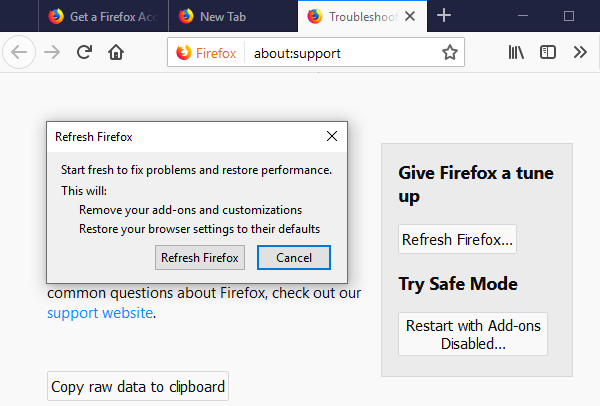
The next step is to confirm that really want to reset the Mozilla Firefox settings to its default by clicking on “Refresh Firefox” button.
Remove Malicious Extension from Safari
Open the Safari and go to its “Menu” and select “Preferences”.
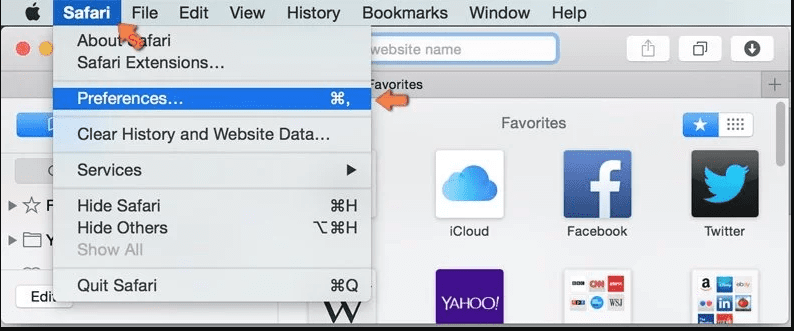
Click on the “Extension” and select all the recently installed “Extensions” and then click on “Uninstall”.
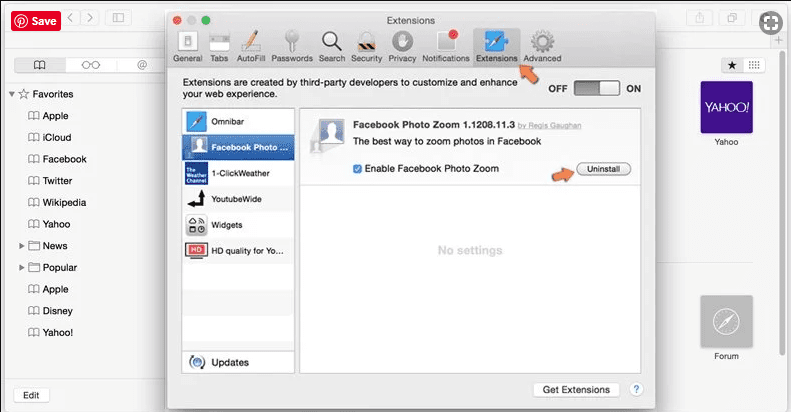
Optional Method
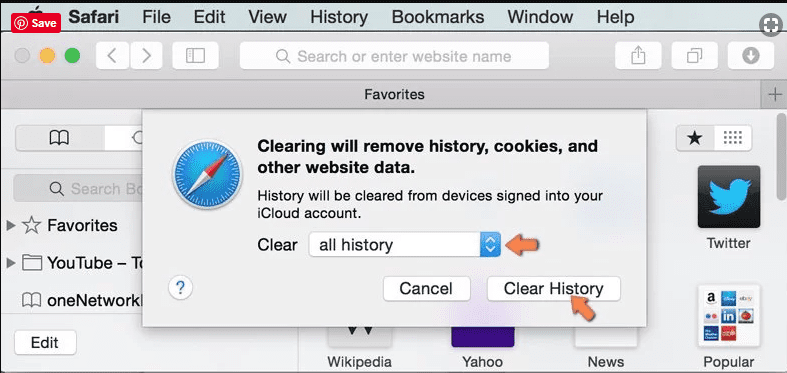
Open the “Safari” and go menu. In the drop-down menu, choose “Clear History and Website Data”.
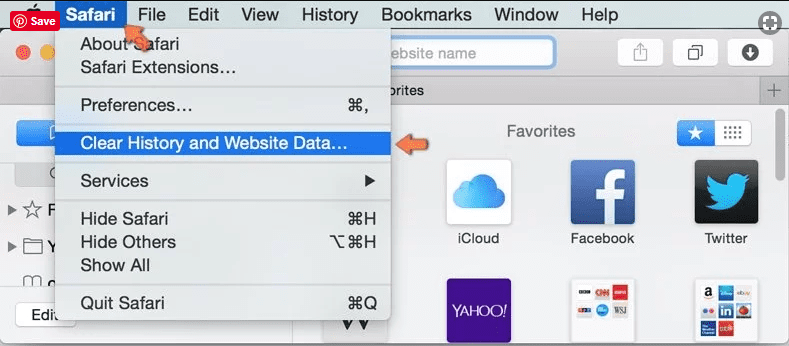
In the newly opened window, select “All History” and then press on “Clear History” option.
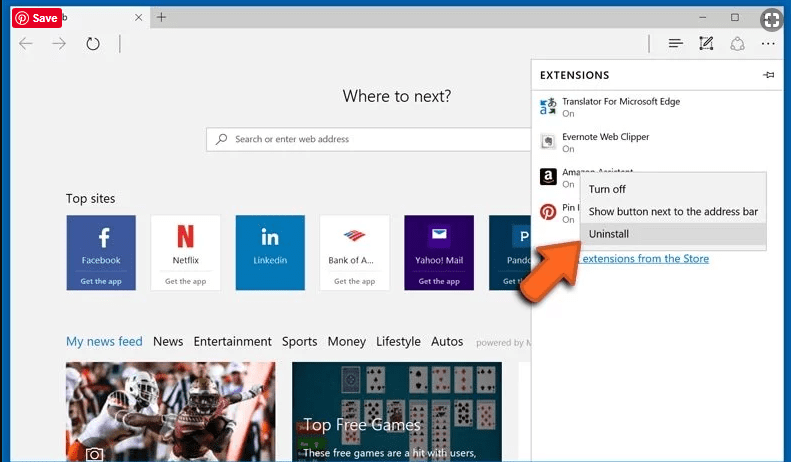
Delete TroyStealer (malicious add-ons) from Microsoft Edge
Open Microsoft Edge and go to three horizontal dot icons at the top right corner of the browser. Select all the recently installed extensions and right click on the mouse to “uninstall”
Optional Method
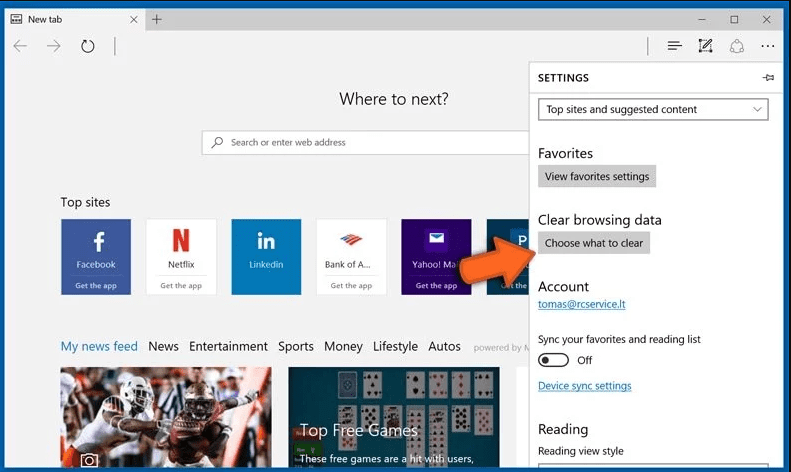
Open the browser (Microsoft Edge) and select “Settings”
Next steps is to click on “Choose what to clear” button
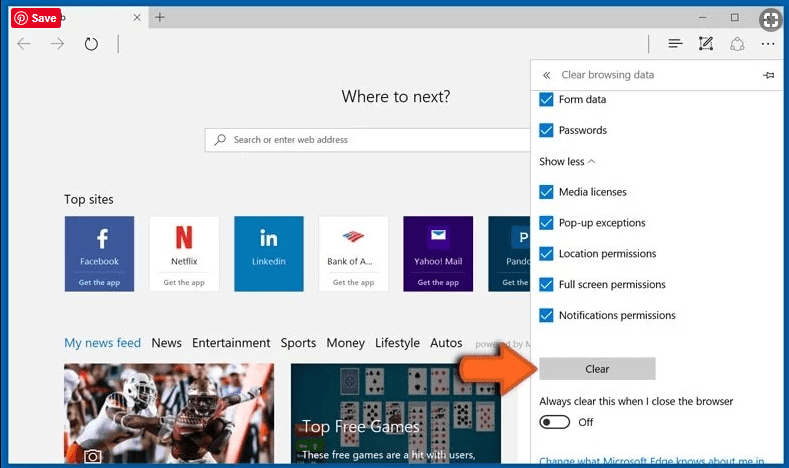
Click on “show more” and then select everything and then press on “Clear” button.
Conclusion
In most cases, the PUPs and adware gets inside the marked PC through unsafe freeware downloads. It is advised that you should only choose developers website only while downloading any kind of free applications. Choose custom or advanced installation process so that you can trace the additional PUPs listed for installation along with the main program.
Special Offer (For Windows)
TroyStealer can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Special Offer (For Macintosh) If you are a Mac user and TroyStealer has affected it, then you can download free antimalware scanner for Mac here to check if the program works for you.