How to remove Ramsay
Easy guide to delete Ramsay
Ramsay is a huge risk computer infection. It bears the potential to scan the compromised device, remove drives and network, share/drive isolated from unprotected networks like public Internet, unsecured local area network for MS Office Documents, PDF documents, ZIP archives or other similar files. In other word, this threat can steal files from the infected device. In addition, it can spread itself on other computers and thus you should perform its removal without much delay.
More about Ramsay
Ramsay can ex-filtrate the stolen files through the components that were dropped from network share, removal drive and/or local system. Once the infected drive is connected to a computer with Internet connection, the ex-filtration of the files by the malware will take place. Researchers’ analysis show, there are total three versions of this malware possible -one of which cannot spread the files while the other two can.
The stolen files could be Microsoft Documents, PDF Documents and ZIP archives. These files could contain data like login credentials (usernames, passwords). Credit card details, email addresses. This might result in identity theft, monetary loss, online privacy issues, browsing safety problems and other related troubles. Either way, if there is a reason to think Ramsay infection on the device, you should perform elimination process as soon as possible.
Threat Summary:
Name: Ramsay
Threat Type: Trojan, Spyware, File stealer
Detected Names: Avast (Win32:Trojan-gen), BitDefender (Trojan.GenericKD.42916371), ESET-NOD32 (A Variant Of Win32/Ramsay.D), Kaspersky (HEUR:Trojan.Win32.Generic), and others
Symptoms: Trojans run on the victims’ system background silently and therefore no particular symptoms are clearly visible on the compromised PC
Distribution methods: Infected email attachments, malicious online advertisements, social engineering, and software cracks
Damage: Stolen passwords, and banking information, identity theft, the victims’ computer added to a botnet
Malware Removal: To eliminate possible malware infections, run a scan to your device with some reputable antivirus software or follow manual instructions provided below the post
System damage and other malware intrusion risks
The Ramsay is in its initial developing state and may be upgraded into a more powerful, complex malware with more capability. It may be used later on in distribution various other malware like Ransomware or cryptocurreny miner or other similar malware injection. Ransomware type of malware encrypts stored files and demand ransom payment. Typically, crooks design it to put ransom demands. In most case, these people do not provide the files in the decrypted form even if all their demands are met. Cryptocurrency miners are designed to generate cryptocurrency by utilizing the CPU and GPU resources that diminish the general working performance of the device and might lead it to permanently getting crashed or freeze.
How did Ramsay infiltrate in?
Researchers show, Ramsay lands on computers through exploit for Word vulnerabilities from 2017 and malicious RTF files. Such documents designed to distribute malware are disturbed in spam email campaigns. Crooks attempt to trick people into installing the malicious software through the malicious attachments or website links that they send via email. The users often get tricked into malware installing when crooks distribute it through untrustworthy software downloading channels such as unofficial activation tools, fake updates.
Peer-to-peer networks such as torrent clients, eMule, third party downloaders, free file hosting sites, free download pages are some common examples that can be used to spread malware by presenting it as legit and important software. Activation tools infect system by supposedly bypassing activation key for paid software. Fake software updaters cause infection by installing malicious software instead of updating installed one, or by exploiting bugs/flaws of outdated software.
How to prevent malware intrusion?
Attachments and website links in irrelevant emails send from unknown, suspicious addresses should never be opened. Files and programs should be downloaded only from official websites and direct download links. All other channels mentioned above the paragraph should be avoided. Installed software must always be activated or updated only through tools and/or functions designed by official software developers. Finally, the device should regularly be scanned for threats with some reputable antivirus tool. Any detected threats should be removed with any deal. Also, some reputable antivirus tool should be kept on the device for the adequate protection.
Remove Ramsay
Manual malware removal guide is provided below in step by step manner. Follow it so that you will not find any trouble during removal process. You can use some reputable antivirus tool to automatically remove Ramsay from the system.
Special Offer (For Windows)
Ramsay can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Special Offer (For Macintosh) If you are a Mac user and Ramsay has affected it, then you can download free antimalware scanner for Mac here to check if the program works for you.
Antimalware Details And User Guide
Click Here For Windows Click Here For Mac
Important Note: This malware asks you to enable the web browser notifications. So, before you go the manual removal process, execute these steps.
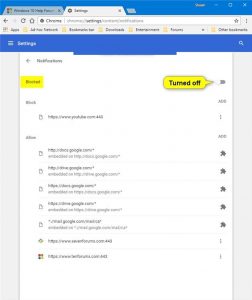
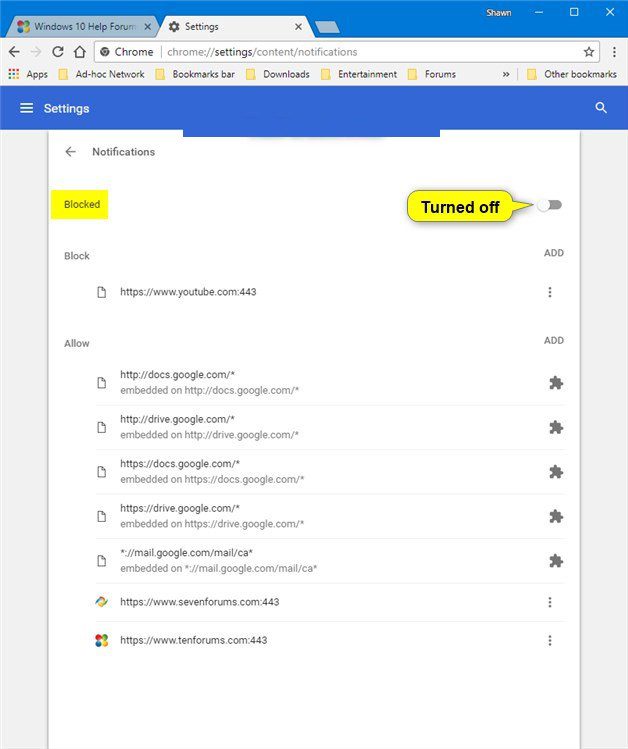
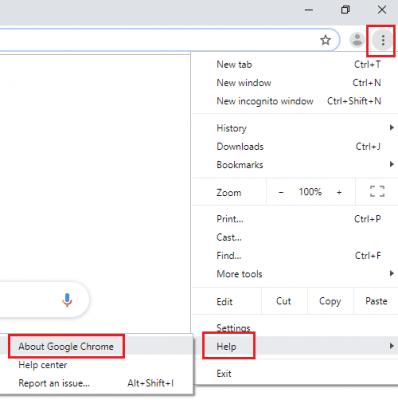
Google Chrome (PC)
- Go to right upper corner of the screen and click on three dots to open the Menu button
- Select “Settings”. Scroll the mouse downward to choose “Advanced” option
- Go to “Privacy and Security” section by scrolling downward and then select “Content settings” and then “Notification” option
- Find each suspicious URLs and click on three dots on the right side and choose “Block” or “Remove” option
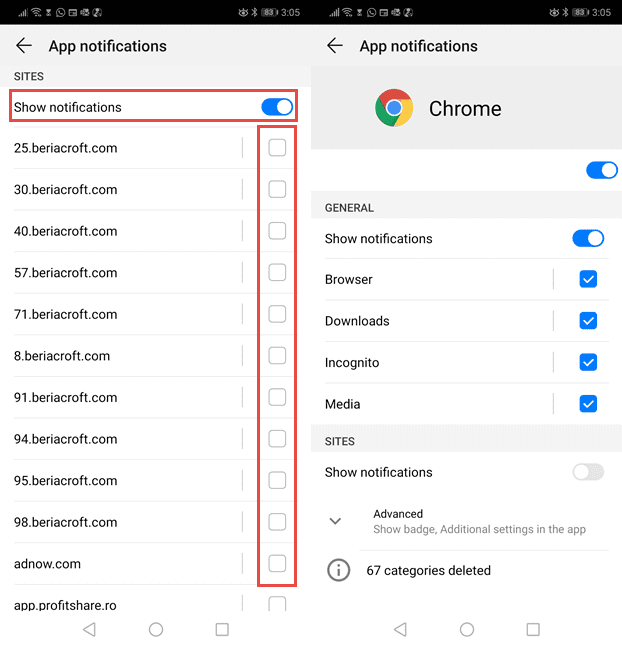
Google Chrome (Android)
- Go to right upper corner of the screen and click on three dots to open the menu button and then click on “Settings”
- Scroll down further to click on “site settings” and then press on “notifications” option
- In the newly opened window, choose each suspicious URLs one by one
- In the permission section, select “notification” and “Off” the toggle button
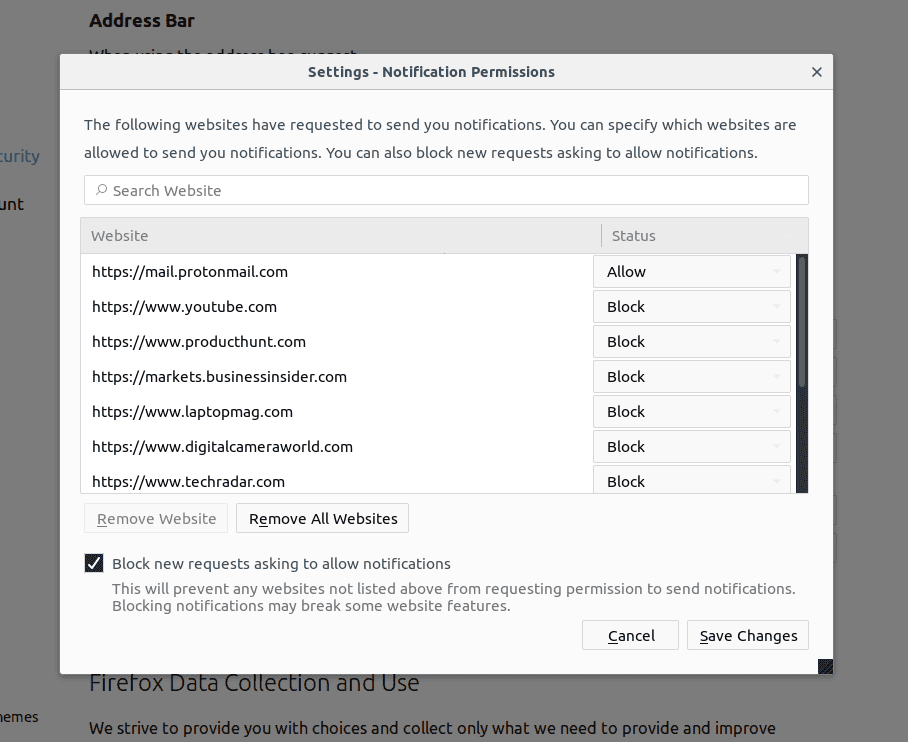
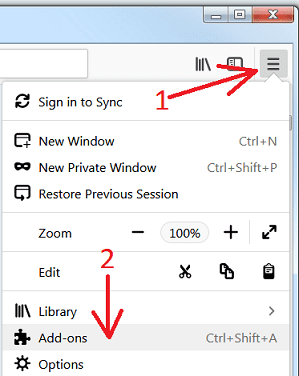
Mozilla Firefox
- On the right corner of the screen, you will notice three dots which is the “Menu” button
- Select “Options” and choose “Privacy and Security” in the toolbar present in the left side of the screen
- Slowly scroll down and go to “Permission” section then choose “Settings” option next to “Notifications”
- In the newly opened window, select all the suspicious URLs. Click on the drop-down menu and select “Block”
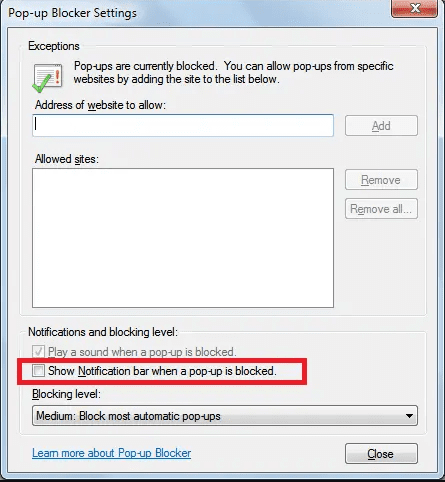
Internet Explorer
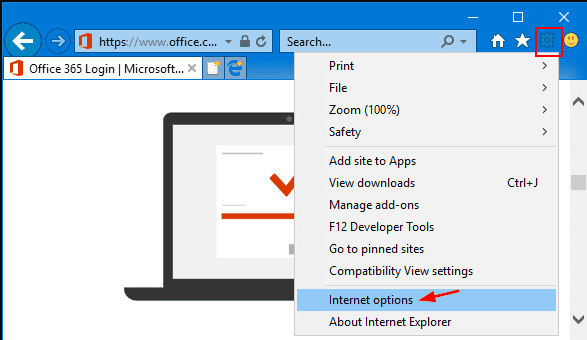
- In the Internet Explorer window, select the Gear button present on the right corner
- Choose “Internet Options”
- Select “Privacy” tab and then “Settings” under the “Pop-up Blocker” section
- Select all the suspicious URLs one by one and click on the “Remove” option
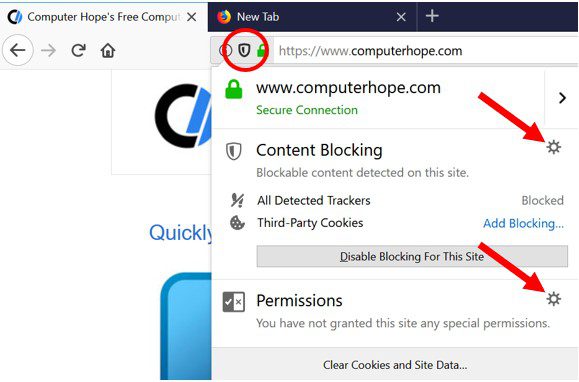
Microsoft Edge
- Open the Microsoft Edge and click on the three dots on the right corner of the screen to open the menu
- Scroll down and select “Settings”
- Scroll down further to choose “view advanced settings”
- In the “Website Permission” option, click on “Manage” option
- Click on switch under every suspicious URL
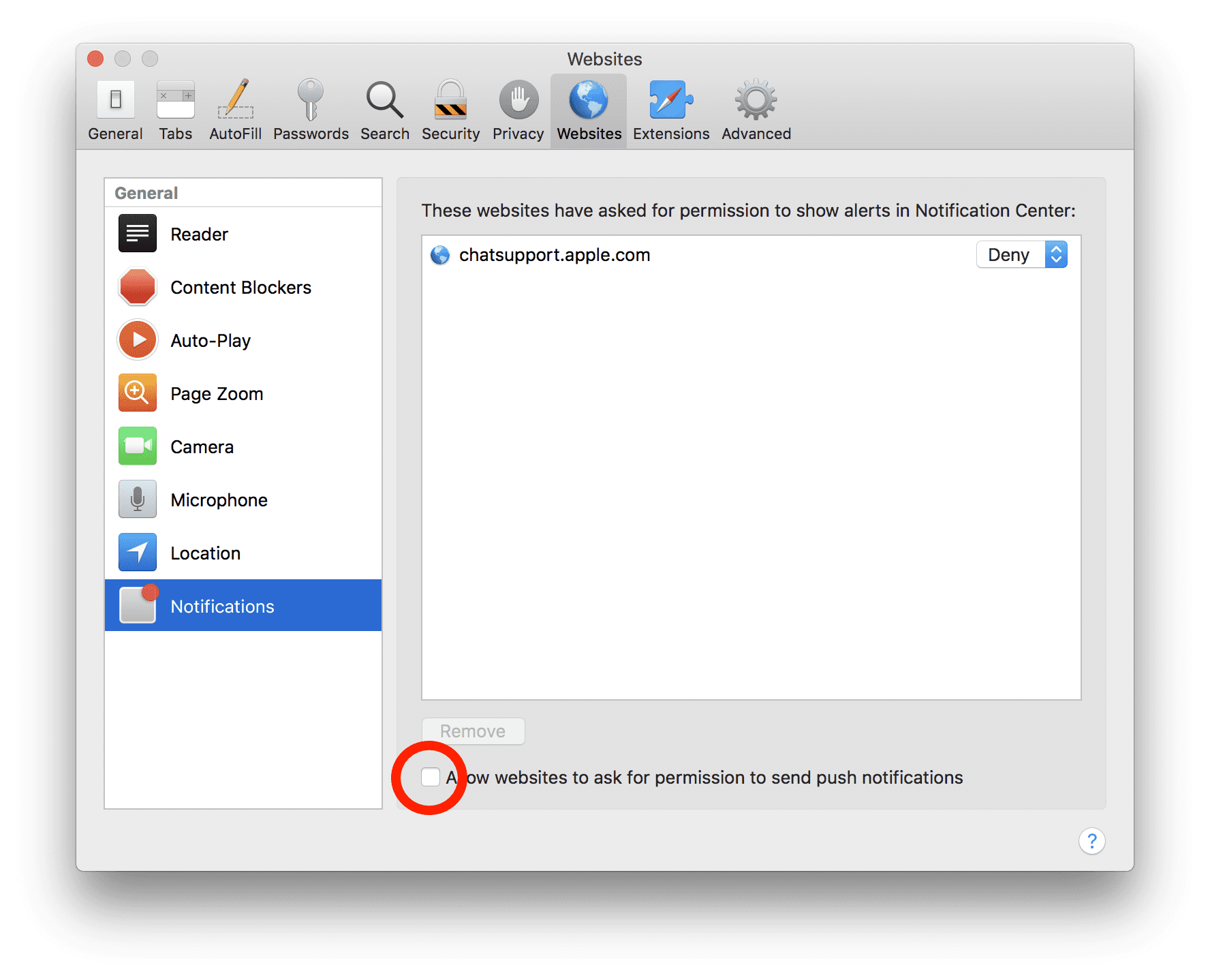
Safari (Mac):
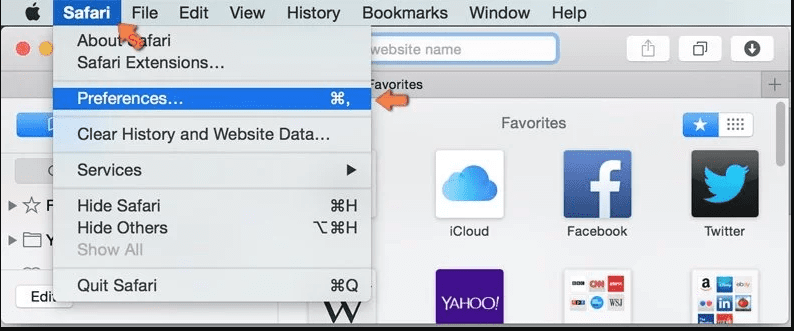
- On the upper right side corner, click on “Safari” and then select “Preferences”
- Go to “website” tab and then choose “Notification” section on the left pane
- Search for the suspicious URLs and choose “Deny” option for each one of them
Manual Steps to Remove Ramsay:
Remove the related items of Ramsay using Control-Panel
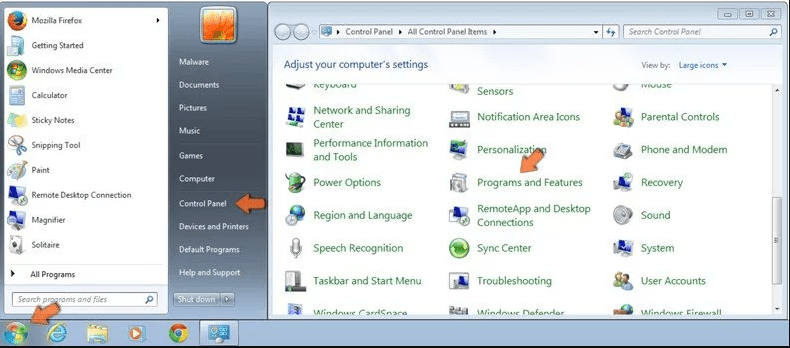
Windows 7 Users
Click “Start” (the windows logo at the bottom left corner of the desktop screen), select “Control Panel”. Locate the “Programs” and then followed by clicking on “Uninstall Program”
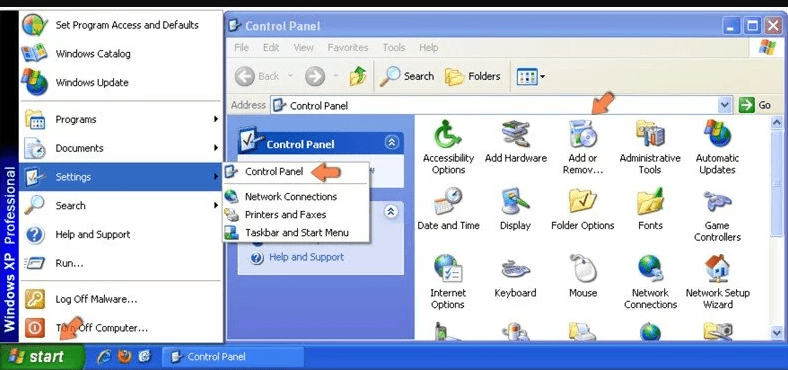
Windows XP Users
Click “Start” and then choose “Settings” and then click “Control Panel”. Search and click on “Add or Remove Program’ option
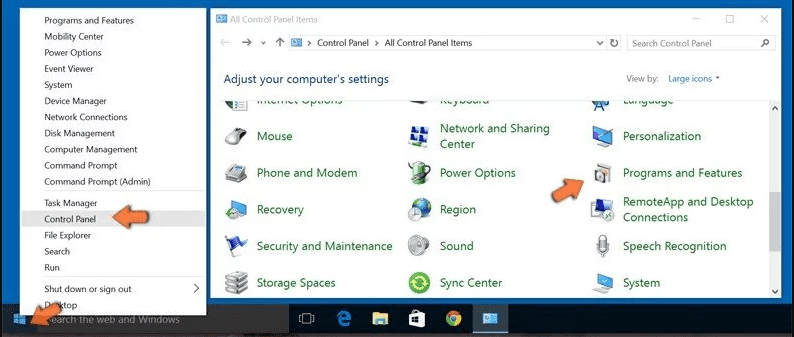
Windows 10 and 8 Users:
Go to the lower left corner of the screen and right-click. In the “Quick Access” menu, choose “Control Panel”. In the newly opened window, choose “Program and Features”
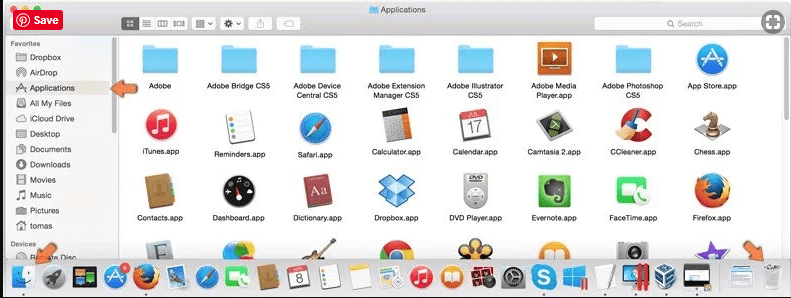
Mac OSX Users
Click on “Finder” option. Choose “Application” in the newly opened screen. In the “Application” folder, drag the app to “Trash”. Right click on the Trash icon and then click on “Empty Trash”.
In the uninstall programs window, search for the PUAs. Choose all the unwanted and suspicious entries and click on “Uninstall” or “Remove”.
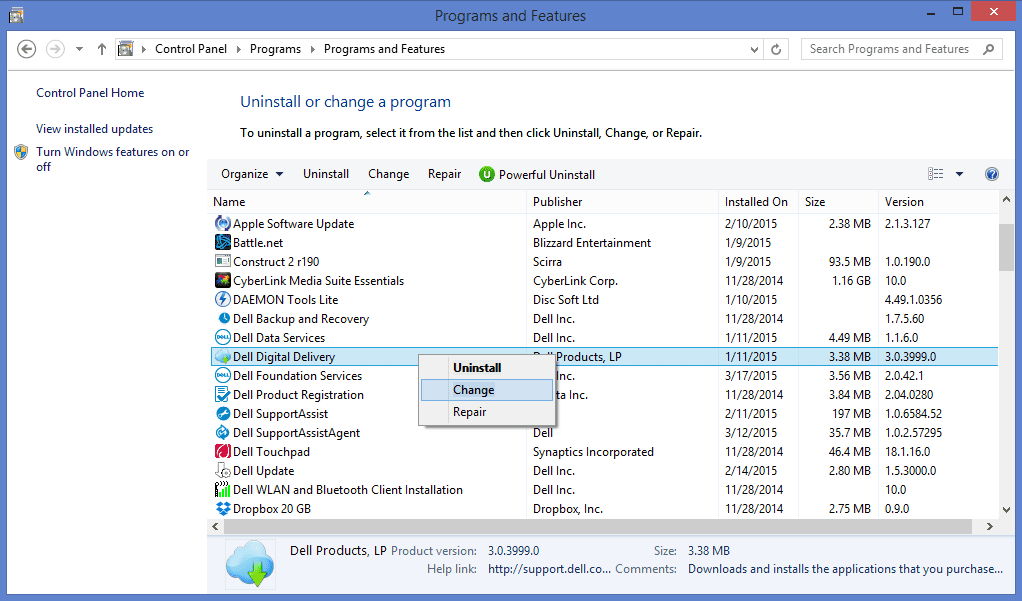
After you uninstall all the potentially unwanted program causing Ramsay issues, scan your computer with an anti-malware tool for any remaining PUPs and PUAs or possible malware infection. To scan the PC, use the recommended the anti-malware tool.
Special Offer (For Windows)
Ramsay can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Special Offer (For Macintosh) If you are a Mac user and Ramsay has affected it, then you can download free antimalware scanner for Mac here to check if the program works for you.
How to Remove Adware (Ramsay) from Internet Browsers
Delete malicious add-ons and extensions from IE
Click on the gear icon at the top right corner of Internet Explorer. Select “Manage Add-ons”. Search for any recently installed plug-ins or add-ons and click on “Remove”.
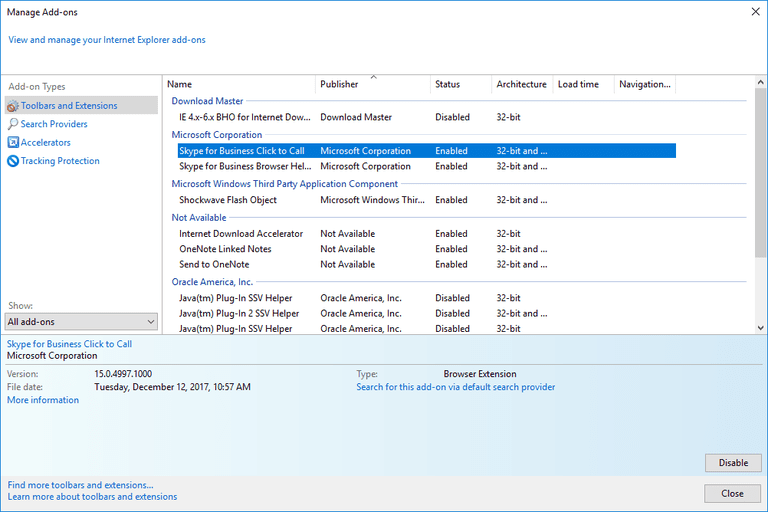
Additional Option
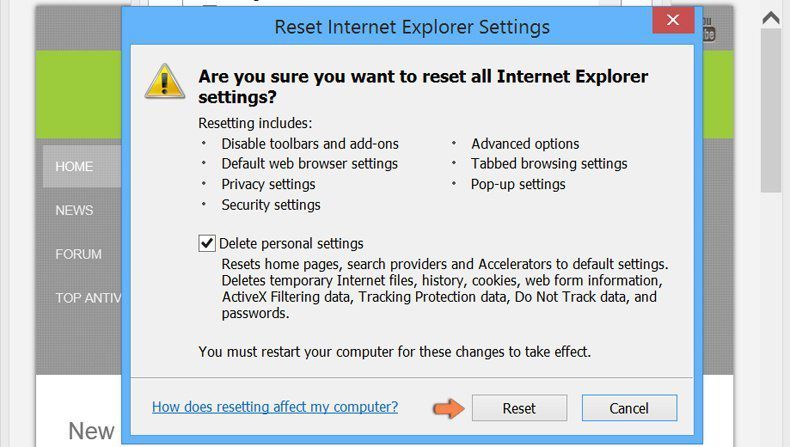
If you still face issues related to Ramsay removal, you can reset the Internet Explorer to its default setting.
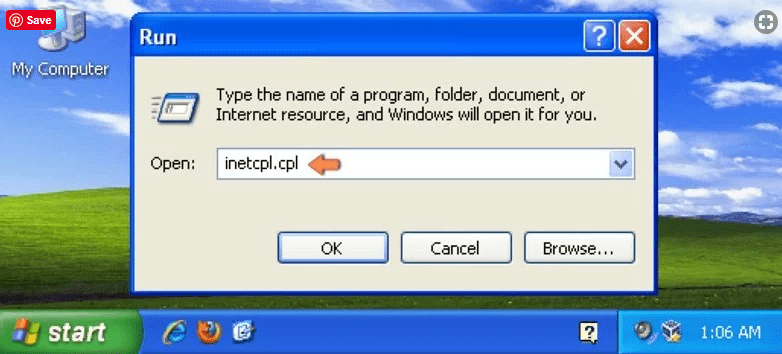
Windows XP users: Press on “Start” and click “Run”. In the newly opened window, type “inetcpl.cpl” and click on the “Advanced” tab and then press on “Reset”.
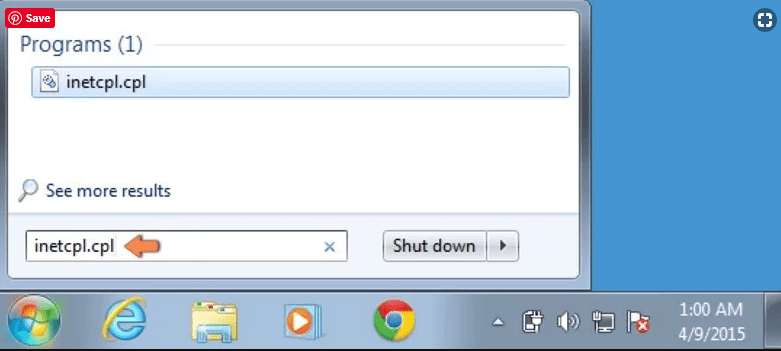
Windows Vista and Windows 7 Users: Press the Windows logo, type inetcpl.cpl in the start search box and press enter. In the newly opened window, click on the “Advanced Tab” followed by “Reset” button.
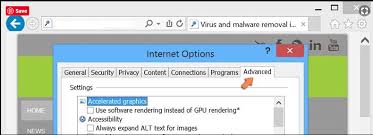
For Windows 8 Users: Open IE and click on the “gear” icon. Choose “Internet Options”
Select the “Advanced” tab in the newly opened window
Press on “Reset” option
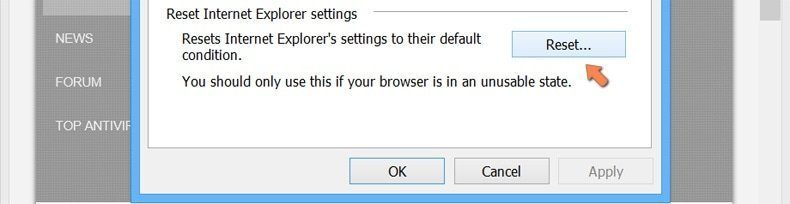
You have to press on the “Reset” button again to confirm that you really want to reset the IE
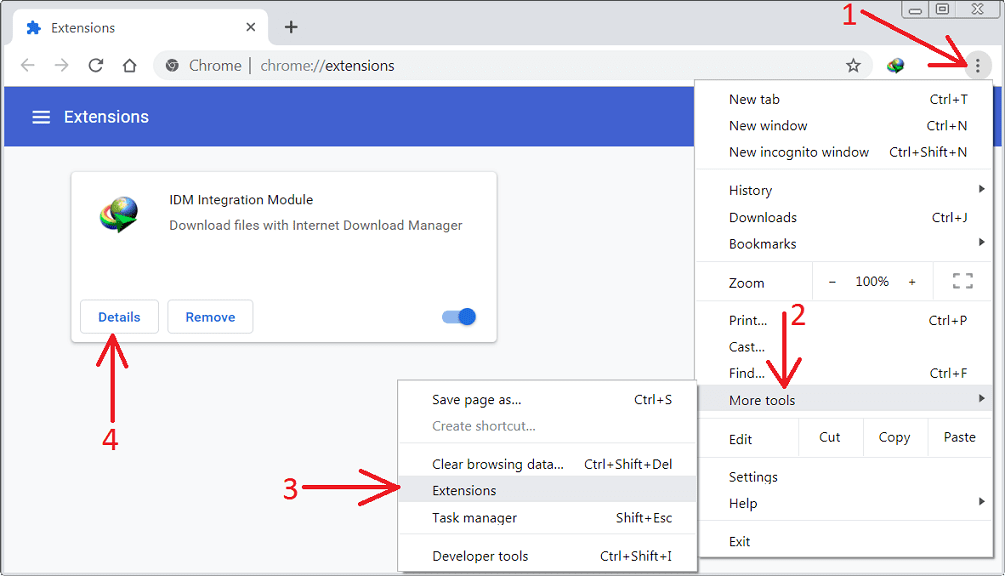
Remove Doubtful and Harmful Extension from Google Chrome
Go to menu of Google Chrome by pressing on three vertical dots and select on “More tools” and then “Extensions”. You can search for all the recently installed add-ons and remove all of them.
Optional Method
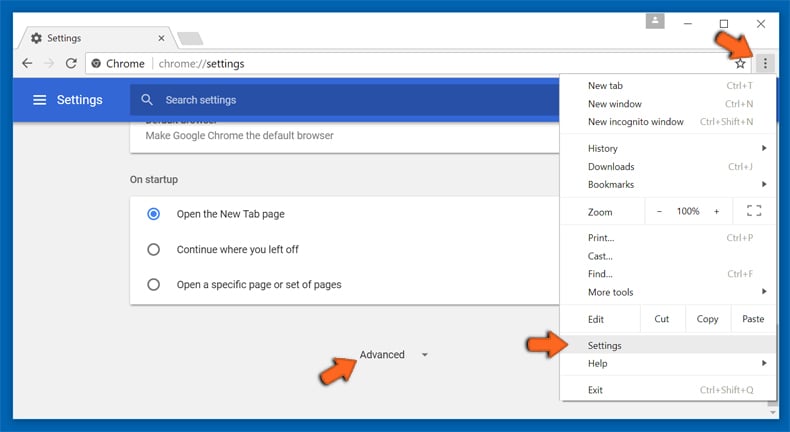
If the problems related to Ramsay still persists or you face any issue in removing, then it is advised that your reset the Google Chrome browse settings. Go to three dotted points at the top right corner and choose “Settings”. Scroll down bottom and click on “Advanced”.
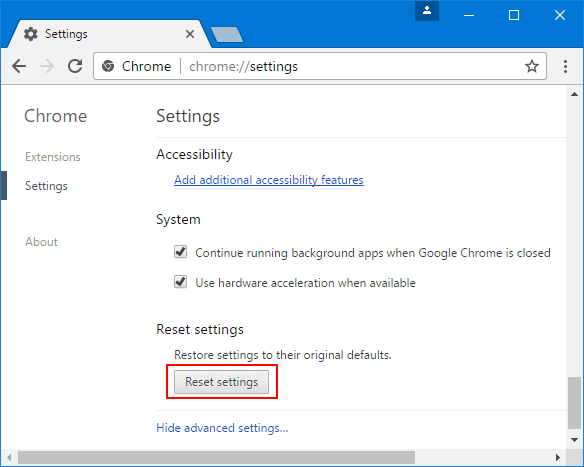
At the bottom, notice the “Reset” option and click on it.
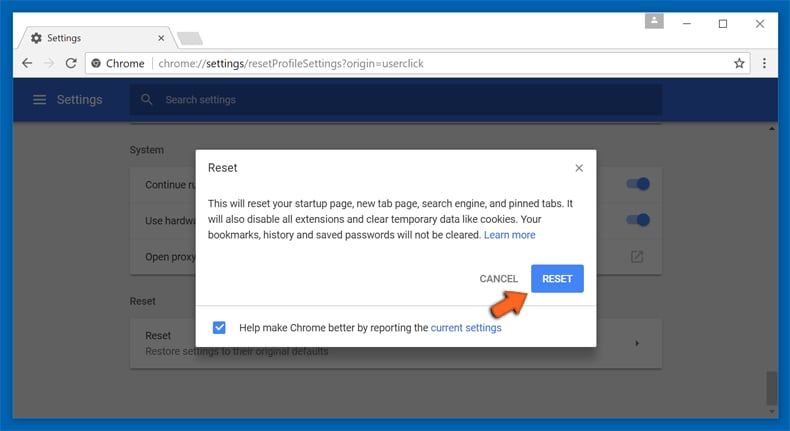
In the next opened window, confirm that you want to reset the Google Chrome settings by click on the “Reset” button.
Remove Ramsay plugins (including all other doubtful plug-ins) from Firefox Mozilla
Open the Firefox menu and select “Add-ons”. Click “Extensions”. Select all the recently installed browser plug-ins.
Optional Method
If you face problems in Ramsay removal then you have the option to rese the settings of Mozilla Firefox.
Open the browser (Mozilla Firefox) and click on the “menu” and then click on “Help”.
Choose “Troubleshooting Information”
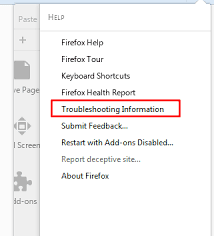
In the newly opened pop-up window, click “Refresh Firefox” button
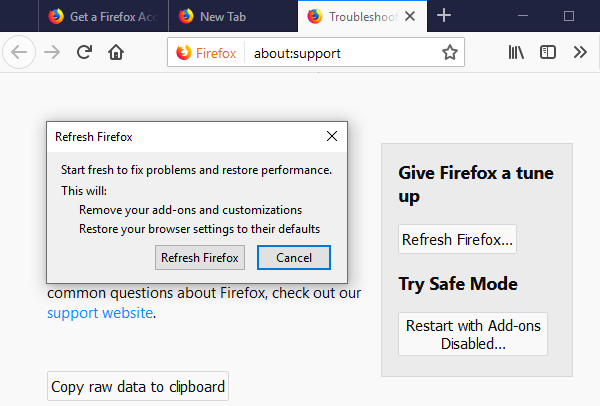
The next step is to confirm that really want to reset the Mozilla Firefox settings to its default by clicking on “Refresh Firefox” button.
Remove Malicious Extension from Safari
Open the Safari and go to its “Menu” and select “Preferences”.
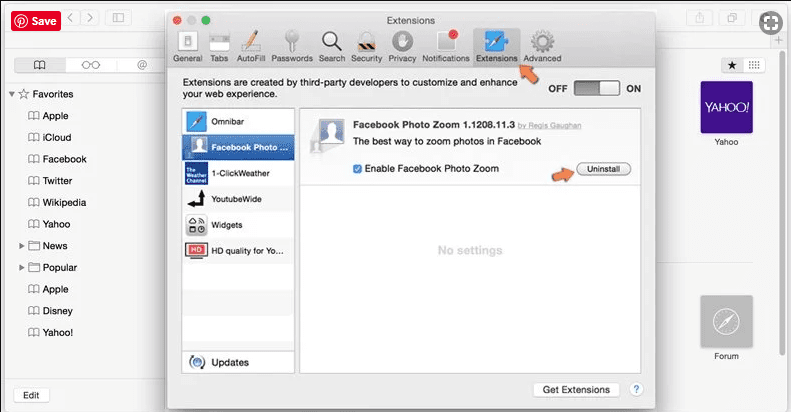
Click on the “Extension” and select all the recently installed “Extensions” and then click on “Uninstall”.
Optional Method
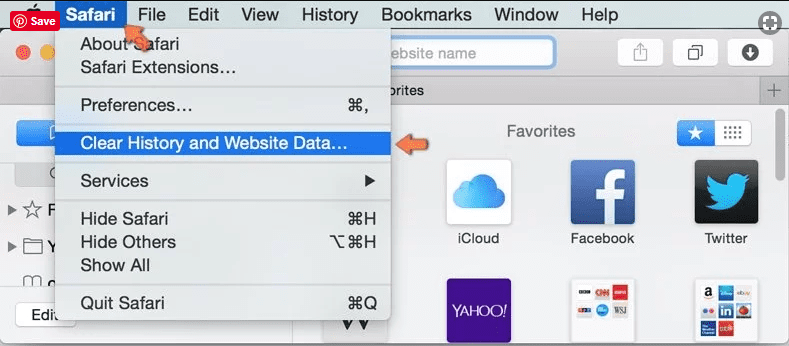
Open the “Safari” and go menu. In the drop-down menu, choose “Clear History and Website Data”.
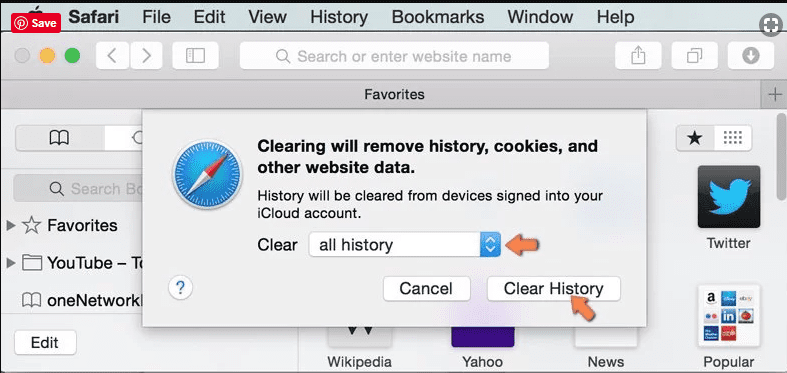
In the newly opened window, select “All History” and then press on “Clear History” option.
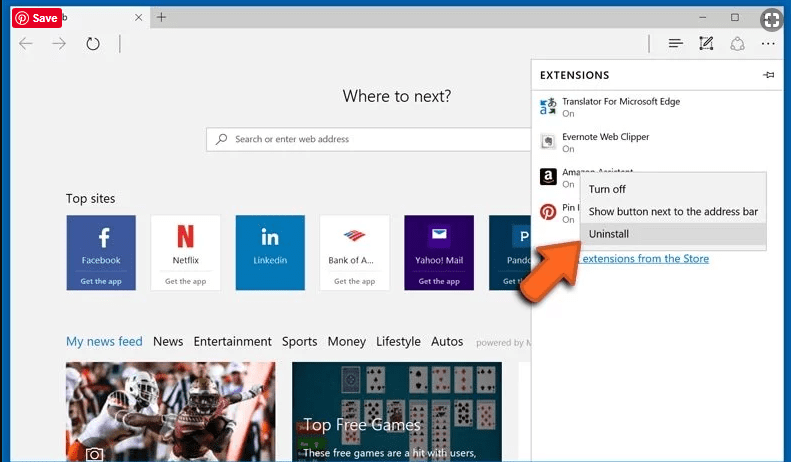
Delete Ramsay (malicious add-ons) from Microsoft Edge
Open Microsoft Edge and go to three horizontal dot icons at the top right corner of the browser. Select all the recently installed extensions and right click on the mouse to “uninstall”
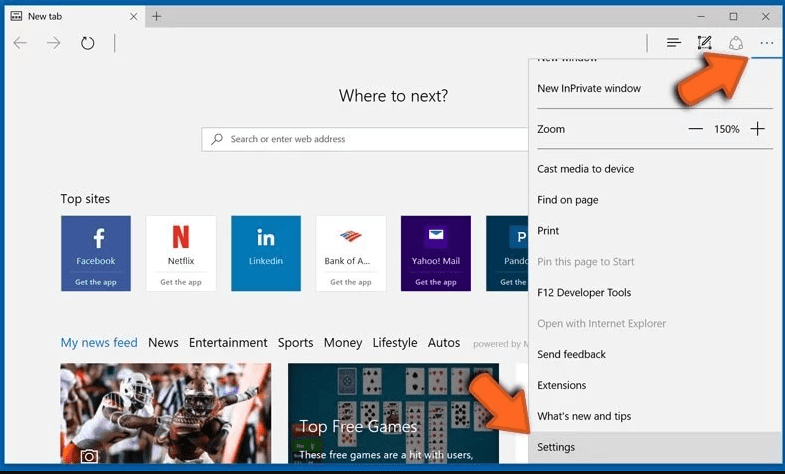
Optional Method
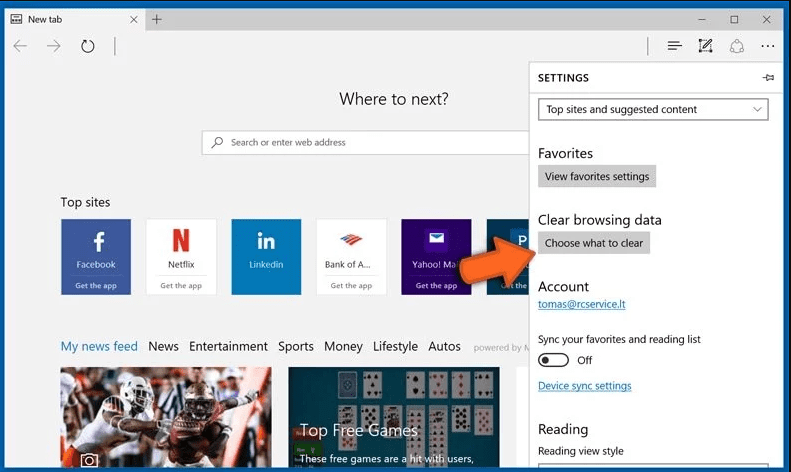
Open the browser (Microsoft Edge) and select “Settings”
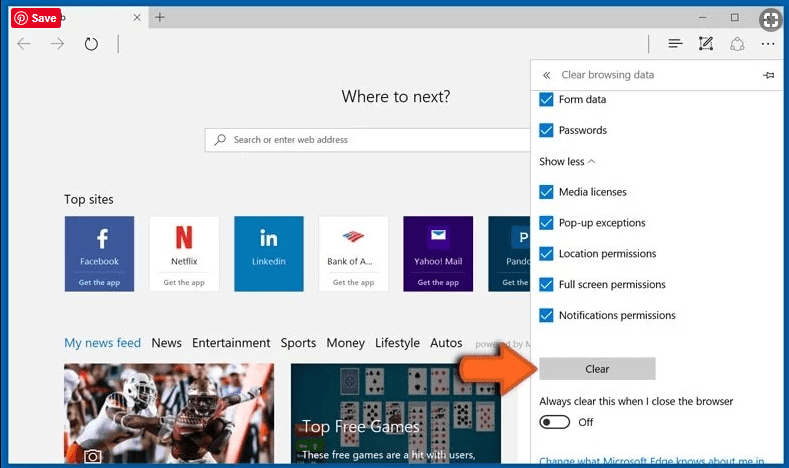
Next steps is to click on “Choose what to clear” button
Click on “show more” and then select everything and then press on “Clear” button.
Conclusion
In most cases, the PUPs and adware gets inside the marked PC through unsafe freeware downloads. It is advised that you should only choose developers website only while downloading any kind of free applications. Choose custom or advanced installation process so that you can trace the additional PUPs listed for installation along with the main program.
Special Offer (For Windows)
Ramsay can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Special Offer (For Macintosh) If you are a Mac user and Ramsay has affected it, then you can download free antimalware scanner for Mac here to check if the program works for you.