Fix the issue “Malware Asking Permission To Make Changes On Your Device”

If you want to remove Malware, it can be a difficult task for you if inexperienced. To completely eliminate this malware, users must uninstall all related items from their Control Panel, Registry, and system files. Additionally, clearing the browser’s cache and cookies and resetting the settings to their default state is necessary to ensure that all remnants of the parasite are eradicated. For those lacking technical skills, using a reputable anti-malware tool is the easiest way to remove Malware. This tool can scan the system and automatically eliminate the threat, making the removal process more efficient and effective.
Special Offer (For Windows)
Malware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wait for next 48 hours. If you intend to remove detected threats instantly, then you will have to buy its licenses version that will activate the software fully.
Special Offer (For Macintosh) If you are a Mac user and Malware has affected it, then you can download free antimalware scanner for Mac here to check if the program works for you.
Complete Guide To Uninstall Unwanted Software
The term “Malware Asking Permission To Make Changes On Your Device” refers to a malicious software tactic where malware seeks user consent to make alterations or perform actions on a device. This deceptive approach aims to exploit unsuspecting users by presenting seemingly legitimate requests or notifications. By asking for permission, the malware attempts to bypass security measures and gain elevated privileges. Once granted access, the malware can execute various harmful activities, such as modifying system settings, installing additional malevolent software, accessing sensitive data, or initiating unauthorized actions.
How would you define malware and in what ways does it seek permission to modify your device?
Malware encompasses a wide range of malicious software like viruses, worms, ransomware, spyware, Trojans, and adware. It can infiltrate devices through various channels, such as downloading files from unreliable sources, interacting with malicious links or attachments, visiting unsafe websites, or connecting to infected devices.
- Malware can solicit permission for device modifications in diverse ways. For instance, some malware exploits vulnerabilities in operating systems or software, gaining access without user awareness. Outdated browsers or plugins with security flaws can allow malware to execute upon visiting specific websites.
- Moreover, malware often disguises itself as genuine applications or updates, enticing users to install them unknowingly. Pop-ups mimicking antivirus software or operating system notifications may trick users into unintentionally installing malware instead.
- Certain malware seizes control of browsers or applications, presenting deceptive alerts or warnings that coerce users into taking action. Such tactics may involve messages claiming device infection or data vulnerability, urging individuals to call a number or click for resolution. However, complying could result in divulging personal information or further malware installation.
What are the risks associated with allowing malware to have permission to modify your device?
Granting permission to malware to make changes on your device can lead to severe repercussions that jeopardize both your device and your data. The implications vary depending on the specific type and objectives of the malware involved. Here are some potential consequences to consider:
- Firstly, malware may inundate your device with unwanted advertisements or redirect your browser to malicious websites. This disrupts your browsing experience and exposes you to further security risks.
- Moreover, certain types of malware are designed to monitor your online activities covertly. They can record your keystrokes or even access your webcam without your knowledge, compromising your privacy and exposing sensitive information.
- Additionally, malware can steal your personal data, including passwords, credit card numbers, and bank account details. This information can be exploited for financial gain or used for identity theft, potentially causing significant harm.
- Furthermore, some malware has the capability to delete or encrypt your files, holding them hostage and demanding a ransom for their recovery. This can result in the loss of important data or significant financial consequences if the ransom is paid.
- Malware can also severely impact your device’s performance. It may slow down its operation, cause frequent crashes, or make it unstable, disrupting your productivity and frustrating your user experience.
- Lastly, malware can serve as a gateway for further infections. It may install additional malware onto your device or allow remote access to hackers, giving them control over your system and potentially leading to more extensive damage.
Overall, granting permission to malware exposes you to a wide array of risks, ranging from intrusive advertisements and privacy breaches to data theft, financial losses, and compromised device functionality. It is crucial to prioritize security measures and remain vigilant to protect against these potential dangers.
What are the steps to resolve the issue “Malware Asking Permission To Make Changes On Your Device?”
If you suspect that malware is requesting permission to make changes on your device, it is important to take immediate action to protect your system and data. Here are the steps you should follow:
- Firstly, don’t grant consent to any suspicious requests or alerts. Close the pop-up window or notification without clicking on any links or buttons. By denying permission, you prevent the malware from gaining access to your device.
- Next, change your passwords for all your accounts, especially if you suspect that your credentials may have been compromised. Use strong, unique passwords and consider enabling two-factor authentication for an added layer of security. This helps protect your accounts from unauthorized access.
- Keeping your device’s operating system and software up to date is crucial. Check for available updates and install them promptly. Updates often include security patches that address vulnerabilities exploited by malware, reducing the risk of infection.
- Regularly backing up your data is essential in case of a malware attack. Create backups of your important files using a reliable cloud service or an external hard drive. This ensures that even if your data is compromised, you can restore it without paying a ransom or losing it permanently.
- Perform a thorough scan of your device using reputable anti-malware software such as SpyHunter 5. Ensure that the software is updated with the latest definitions to detect and remove any identified malware. Follow the software’s instructions to clean your system effectively.
By following these steps, you can effectively address the issue of Malware Asking Permission To Make Changes On Your Device, mitigating the potential risks and protecting your device and data from further harm.
Threat Summary |
| Name: Malware |
| Category: Browser hijacker |
|
Features: Alters the user’s browsing experience by changing the default search engine and homepage, displays unwanted ads, and redirects the user to malicious websites. |
| Danger Level: Medium |
|
Symptoms: The unwanted application can cause several adverse effects, such as displaying intrusive pop-up ads and slowing down internet browsing. The threat can manipulate the settings of an internet browser. This manipulation forces users to visit the hijacker’s website and conduct internet searches using their search engine. |
|
Distribution: Browser hijackers or adware such as Malware can spread through deceptive pop-up ads, free software installers that are bundled with malware, and fake Flash Player installers. |
|
Removal: To remove the threat, scan your system with powerful SpyHunter anti-malware software |
What harms Malware can cause?

Malware is a type of malicious software that can take control of your web browser and modify its settings without your consent. Such apps are typically designed to redirect your web traffic to other sites, display unwanted advertisements, and collect your personal information. Browser hijackers can be very harmful, and can cause a wide range of problems for your computer and your privacy. Below, we will discuss some of the harms that Malware can cause.
- Modify Your Browser Settings: It can modify your browser settings, such as your homepage, default search engine, and new tab page. This can be very frustrating, as it can take a long time to reset these settings back to their original state.
- Display Annoying Ads: This hijacking app often displays unwanted ads, pop-ups, and banners on your screen. These ads can be very annoying, and can even lead to more harmful content if you click on them. In some cases, the ads may even be used to trick you into downloading more malware.
- Redirect Your Web Traffic: It can redirect your web traffic to other sites, even if you didn’t intend to visit those sites. This can be very dangerous, as the sites you are redirected to may contain harmful content, such as malware, phishing scams, or other types of scams.
- Slow Down Your Computer: One of the most obvious harms of hijackers or adware like Malware is that they can slow down your computer. This is because they are constantly running in the background, using up valuable system resources. This can cause your device to become sluggish, unresponsive, and even crash.
- Cause Browser Crashes: Malware can also cause your browser to crash or freeze. This can be very frustrating, as it can cause you to lose any work you were doing, or even cause you to lose important data if you haven’t saved your work.
- Decrease Your Online Privacy: This undesired software piece can decrease your online privacy by tracking your browsing habits, collecting your personal information, and displaying unwanted ads. This can be very harmful, as it can expose you to identity theft, fraud, and other types of cybercrime.
In short, Malware can cause a wide range of harms to your device and your privacy. Therefore, it is important to take steps to protect your computer from this hijacking application, such as using antivirus software, keeping your browser and operating system up to date.
Is Malware a dangerous virus?
Malware is a type of malware that can cause a lot of unkind issues inside the compromised systems. While many don’t consider it as a destructive virus in the sense that it is not intended to damage the device, it can be a nuisance and potentially compromise the user’s online security. Additioanlly, it may indirectly expose their system to more dangerous form of viruses and malware.
Browser hijackers or adware can make your computer more vulnerable to other types of attacks. This is because they often disable your antivirus software, firewall, and other security measures that are designed to protect your system from malware and other types of attacks.
Malware can also be used to install other types of malware on your computer, such as adware, spyware, and even ransomware. These types of malware can cause even more harm, such as stealing your files, encrypting them, and demanding a ransom to unlock them.
In addition to that, such browser-based infections are often designed to collect users’ personal data, such as their browsing history, search queries, and even their login credentials. This information can be used for identity theft, fraud, and other malicious activities.
For these reasons, Malware can still be considered a dangerous computer virus, and must be eliminated from the system as early as possible.
Common FAQ Regarding Malware
What is the purpose of a browser hijacker?
In general terms, a browser hijacker is possibly meant to hijack all browser variants installed on targeted device. During this process, it use to replace its default set values for homepage, new tab, and search engine settings. These modifications often redirect users to surf dubious online sources or phishing pages. These redirected pages often promote some rogue software download options, malicious links, and even more. Interaction with such options can lead to serious chaos to users, however the offerings on such pages help its creators to earn profit either in terms of money or data.
Should I continue using infected browser?
If you suspect your browser is infected by an adware or browser, then you should probably never ignore such impacts. Such infectious object not just alter browser settings to cause redirects or pop up eruption, but also records all your inputs, search preferences, and other sensitive details to allow criminals misusing them for their sake. it’s better to to discontinue usage of infected browser and seek help to eliminate present malware trait soon.
What should I do to protect my device against malware?
Probably, you should aware of malware intrusion methods which we have discussed in the article, and you must avoid interacting with all possible web resources that may transit malicious codes on a device. In addition, do make sure to secure your device using a powerful security application, which also created a great extra layer to your device to assure its efficiency and safety.
Malware Redirection Leads to Unsafe Sites
The redirection chain triggered by Malware may force the browser to send the user to a variety of different webpages. Nonetheless, it’s pertinent to note that most of the websites it sends people to are malicious and even dangerous and may pose a serious threat to the device and the browser. This undesired software piece may take users to following sites:
Tech Support Scam Sites
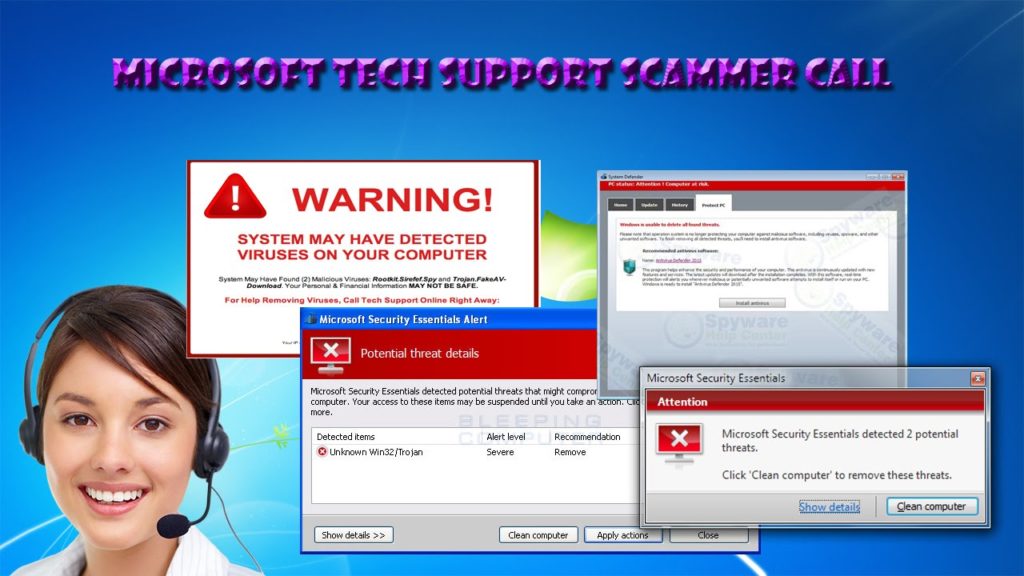
Many people are falling victim to tech support scam websites that have become increasingly widespread. These sites often imitate the appearance of legitimate operating system error messages, making it difficult for individuals to discern whether the message is genuine or a scam. As a result, users are easily fooled into giving scammers access to their personal information or paying for unnecessary and expensive services.
Unsafe Dating Website
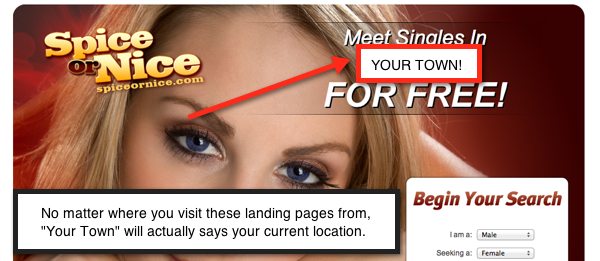
Malware pop-ups may lead you to dubious dating sites that are entirely controlled by robots. Such websites often display deceptive notifications and pop-ups that mislead users into believing that they have multiple chat requests or messages waiting for them. These false alerts may be designed to look convincing and may even use persuasive language to create a sense of urgency, tricking users into clicking on them. In reality, these notifications are usually a tactic employed by scammers to lure individuals into interacting with their fraudulent websites or downloading malicious software.
Websites Showing Fake Virus Alert:

These sites tend to display fake security alerts claiming that users’ PCs are infected with several viruses. They are designed to trick visitors into believing that they are in trouble of having their computers infected and to compel them into taking immediate actions. Scammers behind these deceptions aim to mislead users into downloading and installing malicious software or extracting money from them for useless services.
Drive-by Download Malware Sites

Users may also be taken to drive-by download websites, which is a type of cyberattack in which malware is automatically downloaded to a computer without the user’s knowledge or consent. Drive-by downloads are a serious security threat, as they can result in the installation of viruses, spyware, or other types of malicious software, which can compromise the security and privacy of your computer and personal data.
Fake Giveaway Survey Websites
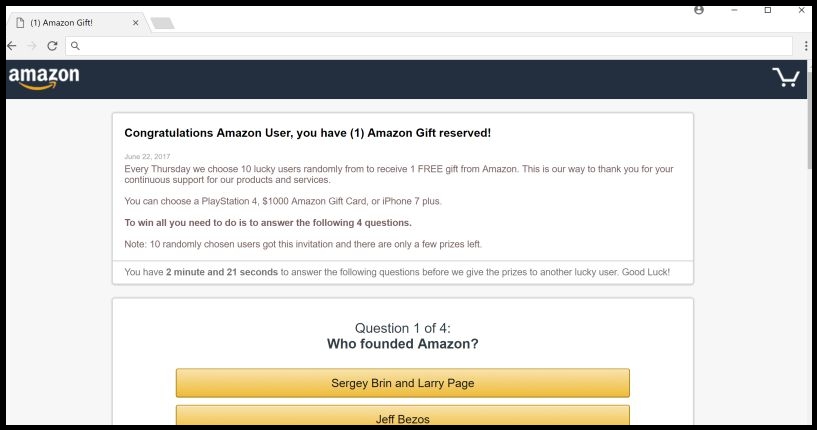
These dubious sites tend to promote bogus surveys aiming to trick users into stealing their personal information such as their credit card details, banking credentials, etc. This sort of information could later be used for various malicious purposes and may lead to a number of unpleasant issues.
Unsafe Pop-Ups Causes Online Scam

Unsafe pop-ups are a common method used by online scammers to deceive unsuspecting internet users. These pop-ups can appear on users’ browser when their system is contaminated with an unwanted application; they visit a website or click on a link, and often try to convince them to take some action, such as downloading a program or providing personal information.
Once users interact with the pop-up, they can be redirected to a fraudulent website that looks legitimate, but is actually designed to steal their sensitive data or money. For example, a Malware pop-up might claim that users’ device is infected with a virus and prompt them to download software that is actually malware.
Other pop-ups might offer a prize or gift in exchange for the user’s personal information, such as their name, address, and credit card number. Once the scammers have this information, they can employ it to make unauthorized purchases or commit identity theft. This can lead to serious privcay issues, identity fraud, high-risk system infections, and even significant monetary losses.
How did Malware Attack my device?
Browser-based parasites like Malware can infect PC systems through a number of deceptive ways. Below are some key points on how these types of malware can sneak into the targeted devices:
- Bundled Software: Adware and browser hijackers are often bundled with legitimate software that users download from the internet. This could be a free utility or game that is made available for download from a website. The site may offer the program for free, but it will be bundled with additional software that the user may not be aware of. When the user download and installs the program, the bundled software will also be installed on their system without their knowledge or consent. This bundled software may include a browser hijacker or adware that will modify the user’s web browser settings.
- Malicious Websites: Malware can also spread through malicious websites. These sites are designed to trick users into downloading and installing software or visiting other harmful web places. People visit a malicious website often by clicking on a link in a spam email, a social post, or a search engine result. The site contains code that automatically downloads and installs the undesired software piece onto the users’ computer without their knowledge or approval.
- Exploits: Other way through which PUPs like Malware can enter the computer systems is exploits. Exploits are vulnerabilities in software that can be exploited by attackers to gain unauthorized access to a computer system or to install malware or adware. Threat actors find a vulnerability in the user’s web browser, operating system, or a plugin, such as Java or Flash. After that, they create a website that contains code that exploits the vulnerability when the user visits the site. The exploit downloads and installs the parasite onto the PC without users’ awareness or consent.
- Social Engineering: Malware can make its way into the device through social engineering as well, which is a technique used by hackers to trick users into downloading and installing malware. These internet criminals create a fake advertisement or pop-up message that claims the user needs to update their software or install a new plugin to view content on a website. The pop-up message may contain a convincing message, such as “Your Flash Player is out of date, please click here to update it” or “Your computer is infected, click here to remove the virus.” When users click on the pop-up message, they end up downloading and installing the unwanted program without realizing it.
Special Offer (For Windows)
Malware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wait for next 48 hours. If you intend to remove detected threats instantly, then you will have to buy its licenses version that will activate the software fully.
Special Offer (For Macintosh) If you are a Mac user and Malware has affected it, then you can download free antimalware scanner for Mac here to check if the program works for you.
Antimalware Details And User Guide
Click Here For Windows Click Here For Mac
Important Note: This malware asks you to enable the web browser notifications. So, before you go the manual removal process, execute these steps.
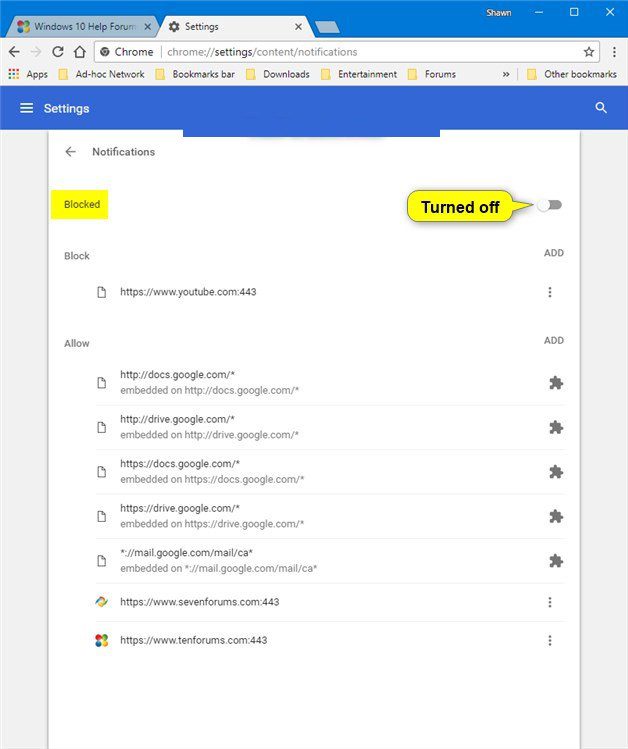
Google Chrome (PC)
- Go to right upper corner of the screen and click on three dots to open the Menu button
- Select “Settings”. Scroll the mouse downward to choose “Advanced” option
- Go to “Privacy and Security” section by scrolling downward and then select “Content settings” and then “Notification” option
- Find each suspicious URLs and click on three dots on the right side and choose “Block” or “Remove” option
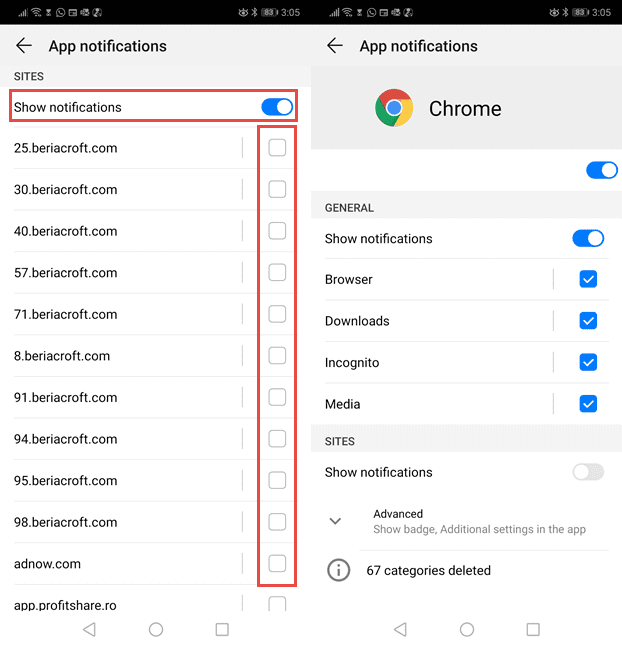
Google Chrome (Android)
- Go to right upper corner of the screen and click on three dots to open the menu button and then click on “Settings”
- Scroll down further to click on “site settings” and then press on “notifications” option
- In the newly opened window, choose each suspicious URLs one by one
- In the permission section, select “notification” and “Off” the toggle button
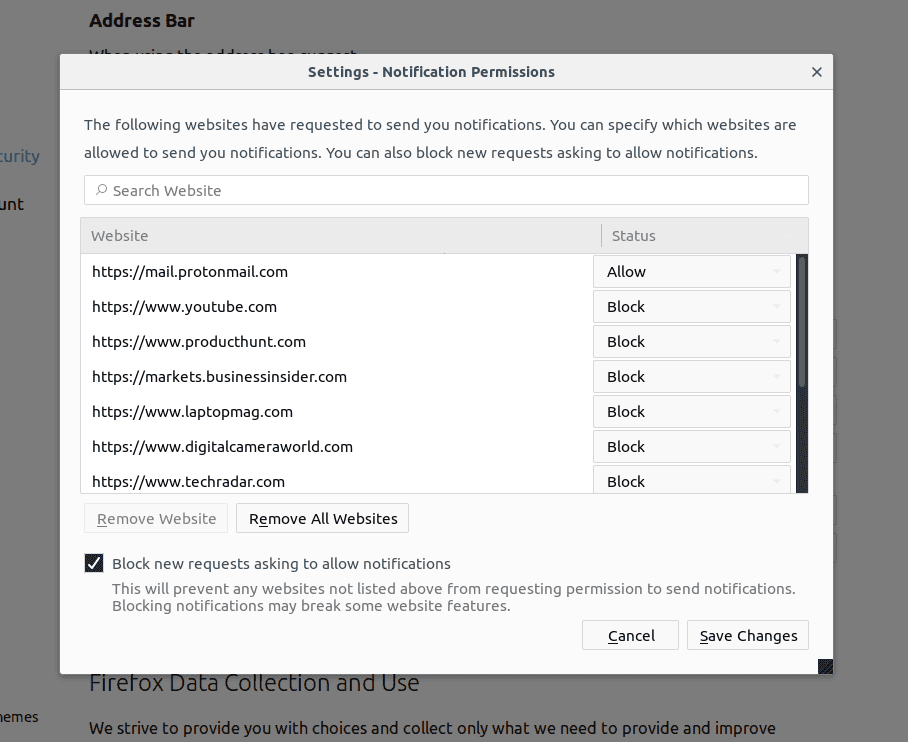
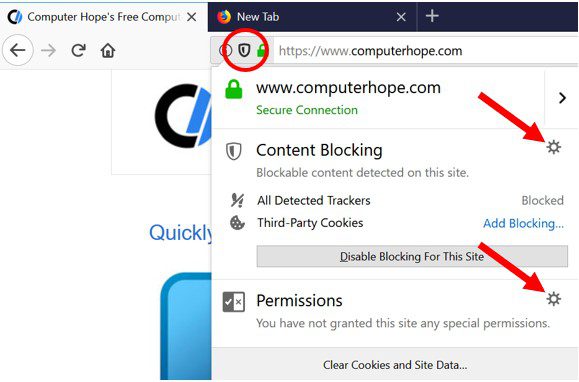
Mozilla Firefox
- On the right corner of the screen, you will notice three dots which is the “Menu” button
- Select “Options” and choose “Privacy and Security” in the toolbar present in the left side of the screen
- Slowly scroll down and go to “Permission” section then choose “Settings” option next to “Notifications”
- In the newly opened window, select all the suspicious URLs. Click on the drop-down menu and select “Block”
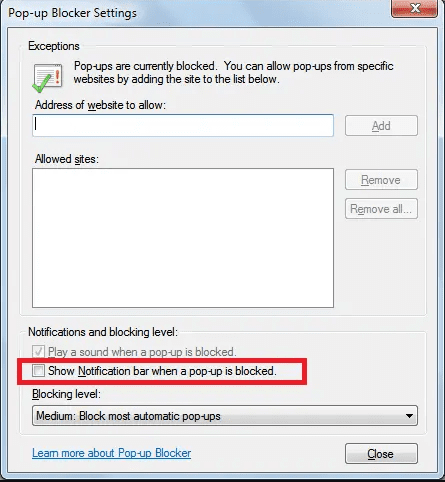
Internet Explorer
- In the Internet Explorer window, select the Gear button present on the right corner
- Choose “Internet Options”
- Select “Privacy” tab and then “Settings” under the “Pop-up Blocker” section
- Select all the suspicious URLs one by one and click on the “Remove” option
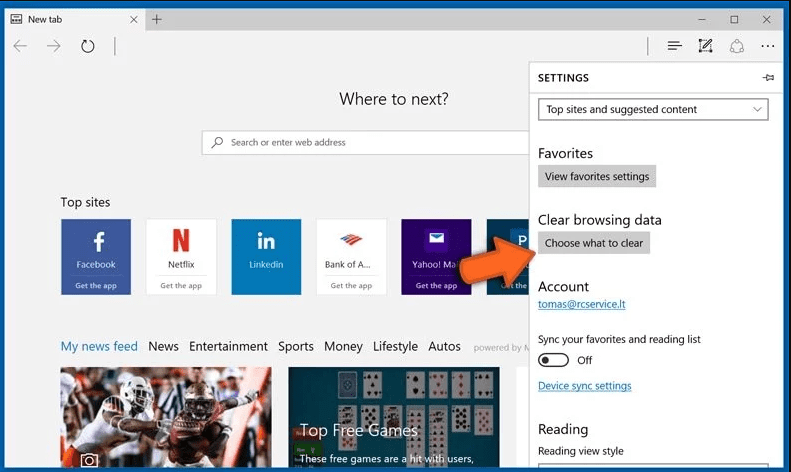
Microsoft Edge
- Open the Microsoft Edge and click on the three dots on the right corner of the screen to open the menu
- Scroll down and select “Settings”
- Scroll down further to choose “view advanced settings”
- In the “Website Permission” option, click on “Manage” option
- Click on switch under every suspicious URL
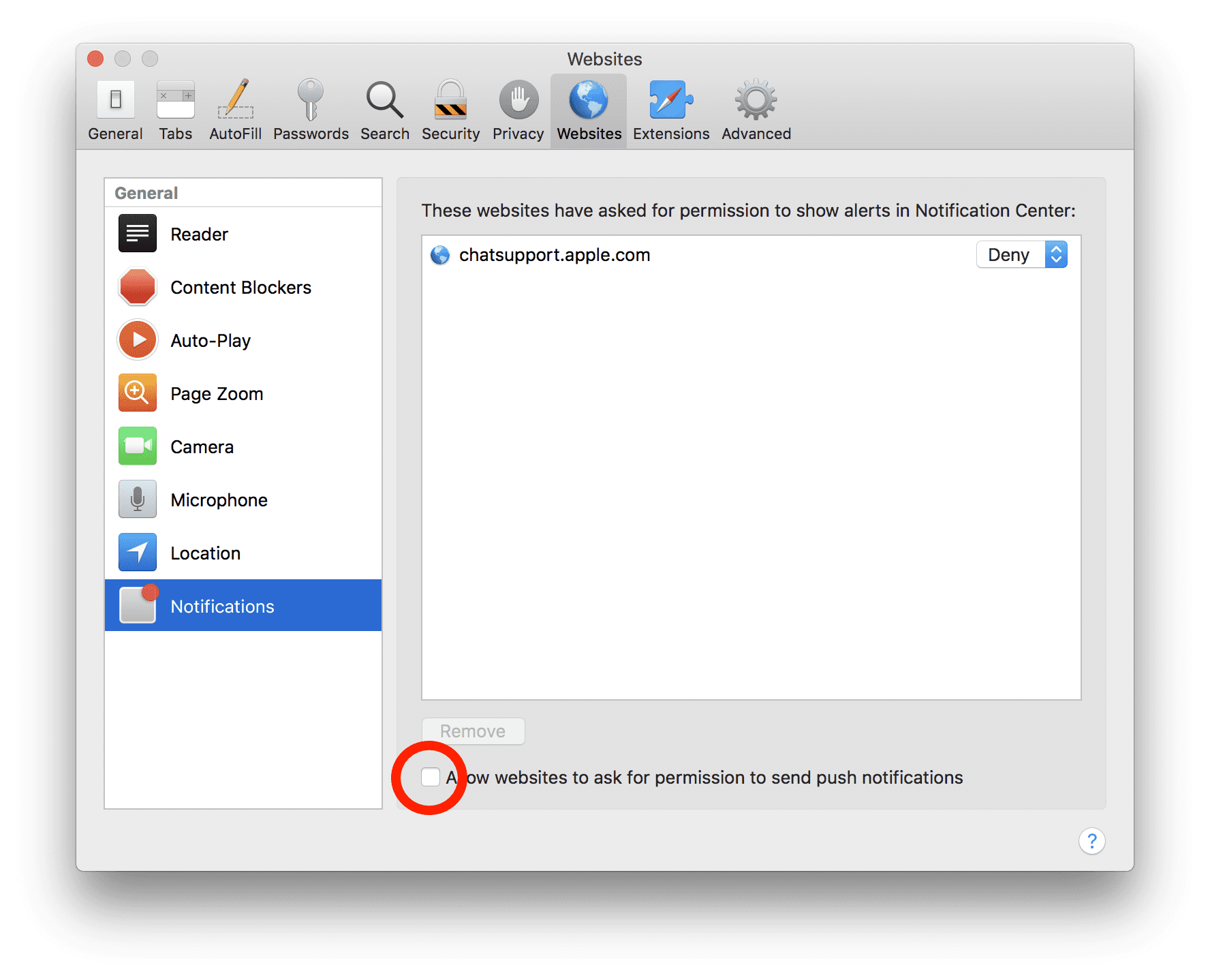
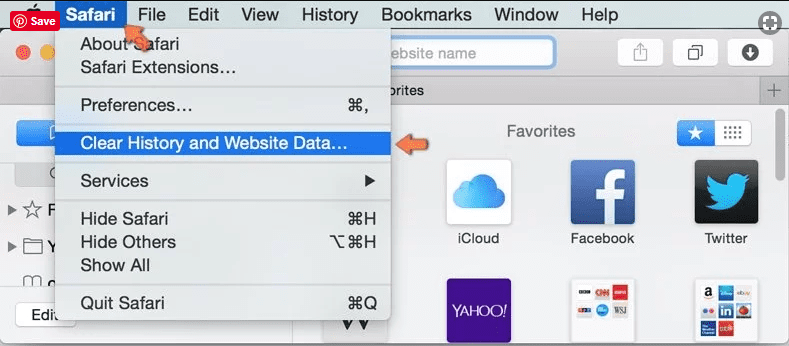
Safari (Mac):
- On the upper right side corner, click on “Safari” and then select “Preferences”
- Go to “website” tab and then choose “Notification” section on the left pane
- Search for the suspicious URLs and choose “Deny” option for each one of them
Manual Steps to Remove Malware:
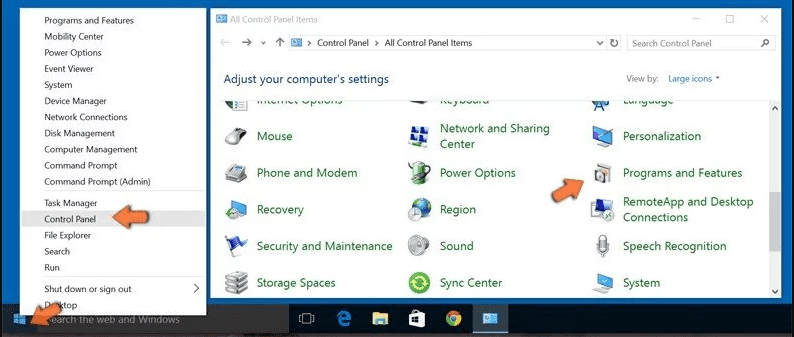
Remove the related items of Malware using Control-Panel
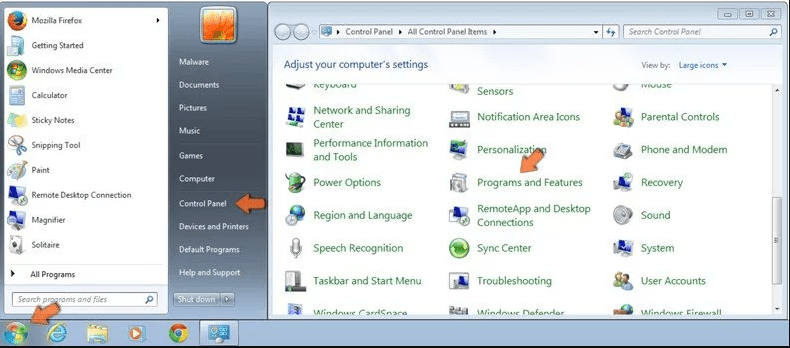
Windows 7 Users
Click “Start” (the windows logo at the bottom left corner of the desktop screen), select “Control Panel”. Locate the “Programs” and then followed by clicking on “Uninstall Program”
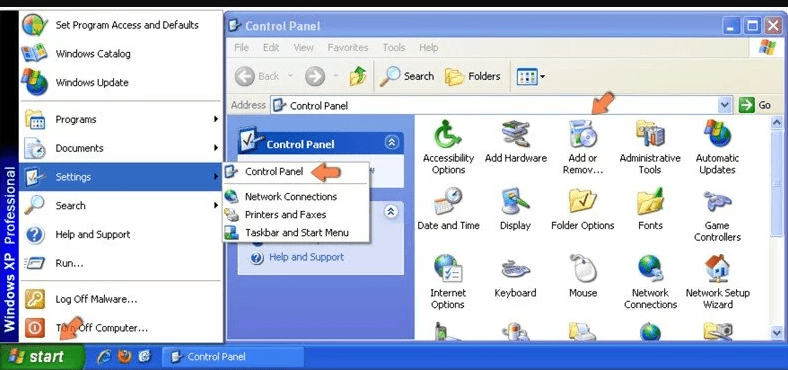
Windows XP Users
Click “Start” and then choose “Settings” and then click “Control Panel”. Search and click on “Add or Remove Program’ option
Windows 10 and 8 Users:
Go to the lower left corner of the screen and right-click. In the “Quick Access” menu, choose “Control Panel”. In the newly opened window, choose “Program and Features”
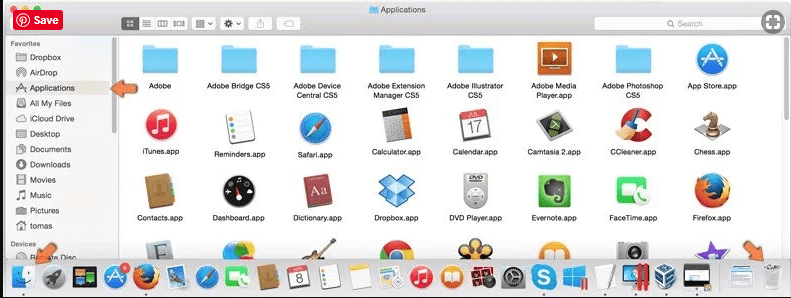
Mac OSX Users
Click on “Finder” option. Choose “Application” in the newly opened screen. In the “Application” folder, drag the app to “Trash”. Right click on the Trash icon and then click on “Empty Trash”.
In the uninstall programs window, search for the PUAs. Choose all the unwanted and suspicious entries and click on “Uninstall” or “Remove”.
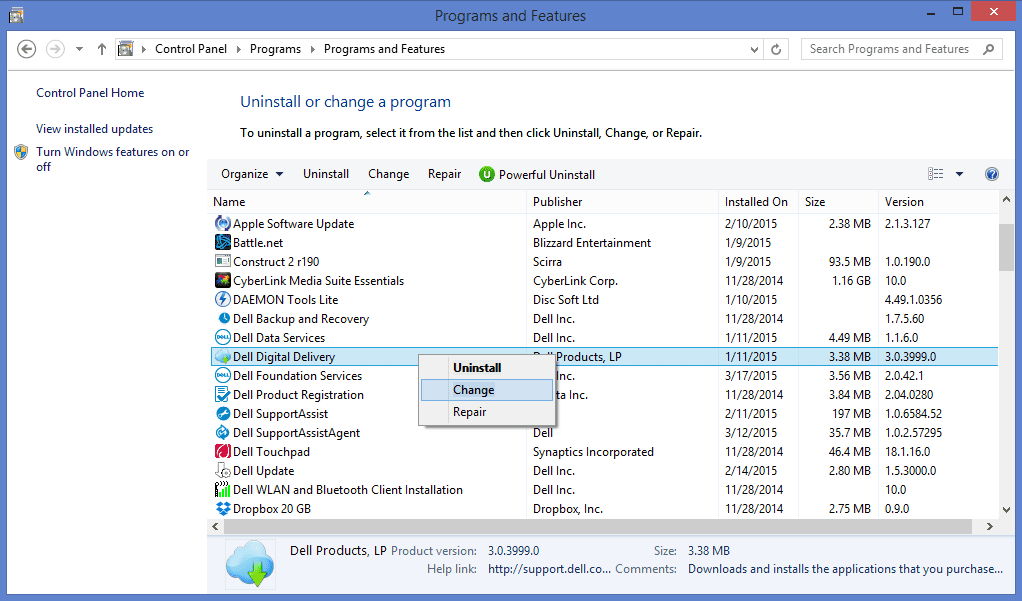
After you uninstall all the potentially unwanted program causing Malware issues, scan your computer with an anti-malware tool for any remaining PUPs and PUAs or possible malware infection. To scan the PC, use the recommended the anti-malware tool.
Special Offer (For Windows)
Malware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wait for next 48 hours. If you intend to remove detected threats instantly, then you will have to buy its licenses version that will activate the software fully.
Special Offer (For Macintosh) If you are a Mac user and Malware has affected it, then you can download free antimalware scanner for Mac here to check if the program works for you.
How to Remove Adware (Malware) from Internet Browsers
Delete malicious add-ons and extensions from IE
Click on the gear icon at the top right corner of Internet Explorer. Select “Manage Add-ons”. Search for any recently installed plug-ins or add-ons and click on “Remove”.
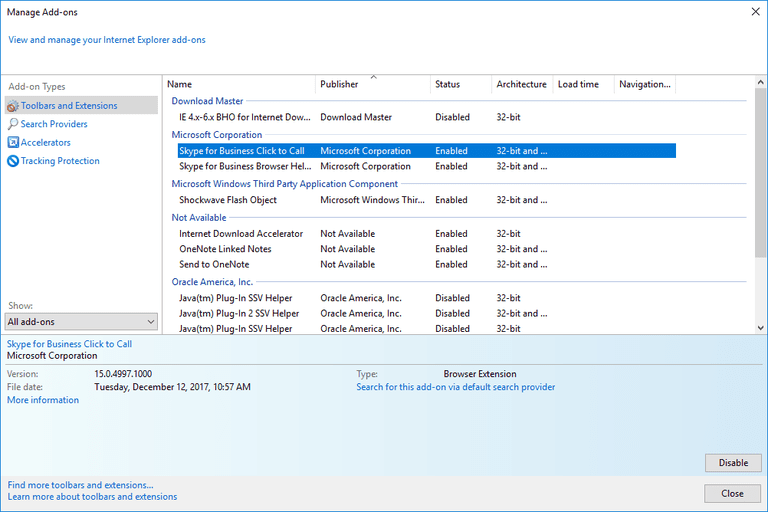
Additional Option
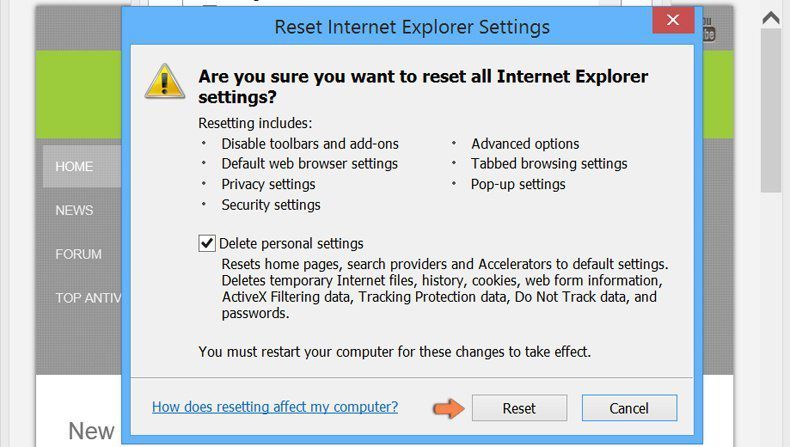
If you still face issues related to Malware removal, you can reset the Internet Explorer to its default setting.
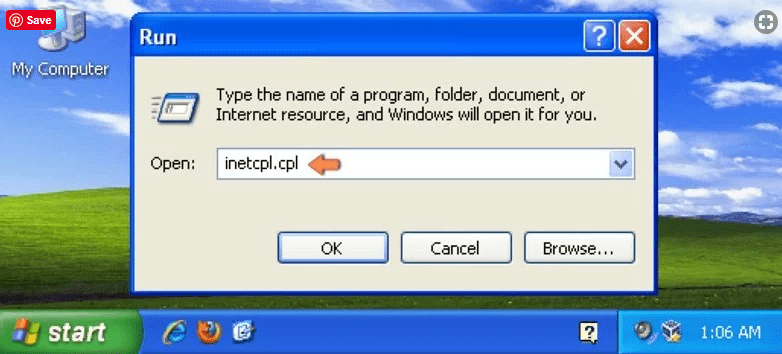
Windows XP users: Press on “Start” and click “Run”. In the newly opened window, type “inetcpl.cpl” and click on the “Advanced” tab and then press on “Reset”.
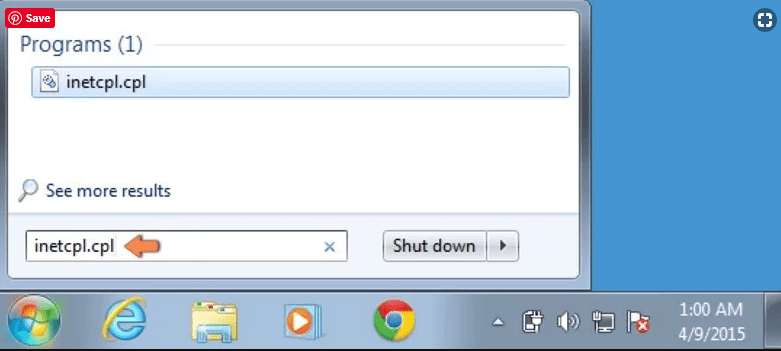
Windows Vista and Windows 7 Users: Press the Windows logo, type inetcpl.cpl in the start search box and press enter. In the newly opened window, click on the “Advanced Tab” followed by “Reset” button.
For Windows 8 Users: Open IE and click on the “gear” icon. Choose “Internet Options”
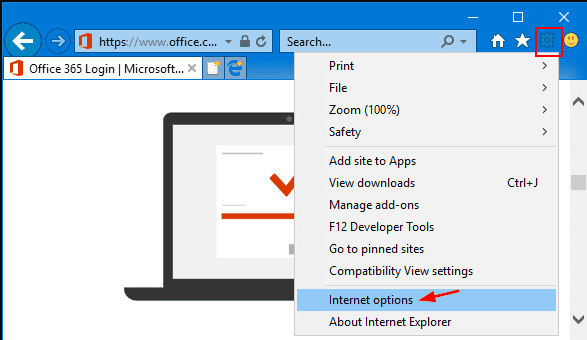
Select the “Advanced” tab in the newly opened window
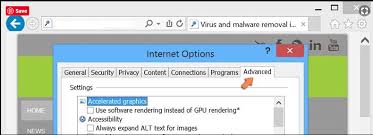
Press on “Reset” option
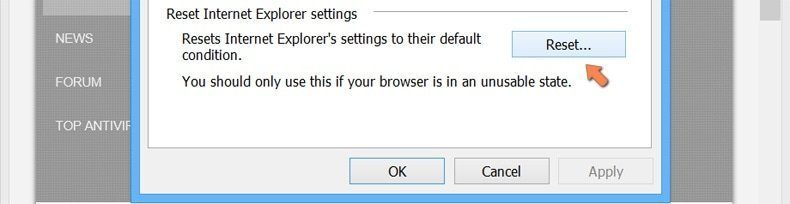
You have to press on the “Reset” button again to confirm that you really want to reset the IE
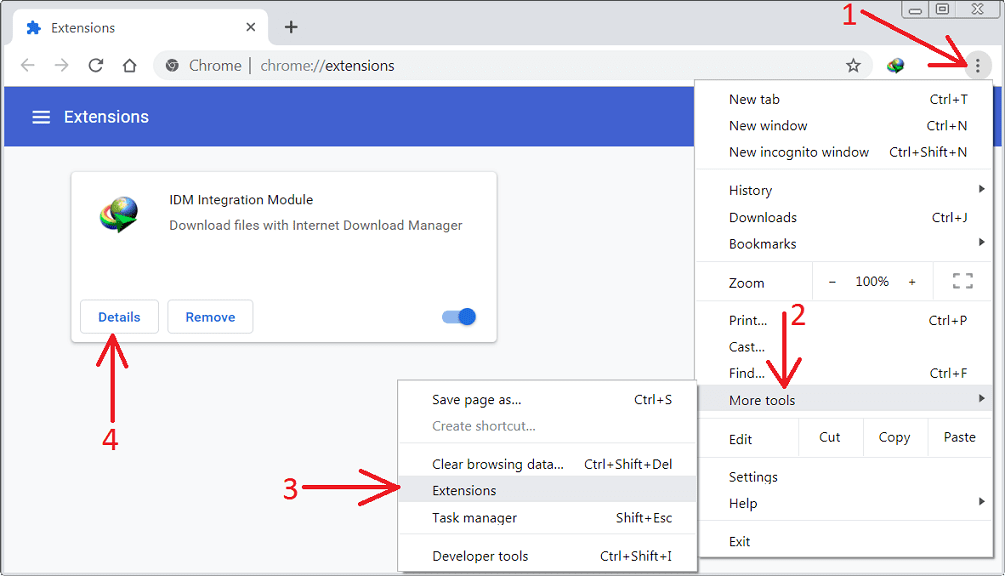
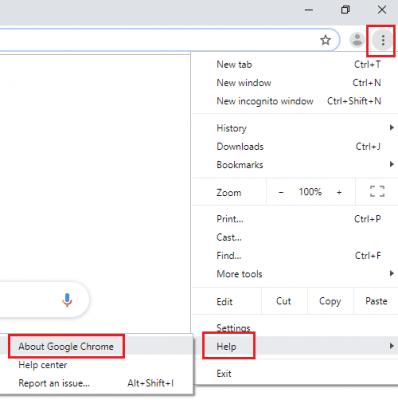
Remove Doubtful and Harmful Extension from Google Chrome
Go to menu of Google Chrome by pressing on three vertical dots and select on “More tools” and then “Extensions”. You can search for all the recently installed add-ons and remove all of them.
Optional Method
If the problems related to Malware still persists or you face any issue in removing, then it is advised that your reset the Google Chrome browse settings. Go to three dotted points at the top right corner and choose “Settings”. Scroll down bottom and click on “Advanced”.
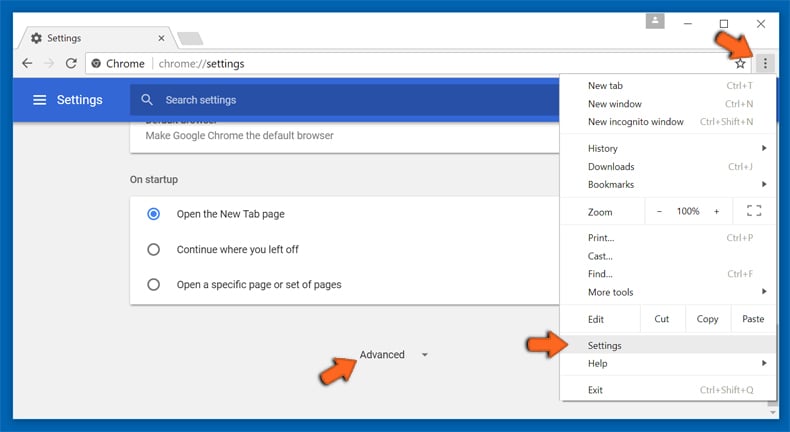
At the bottom, notice the “Reset” option and click on it.
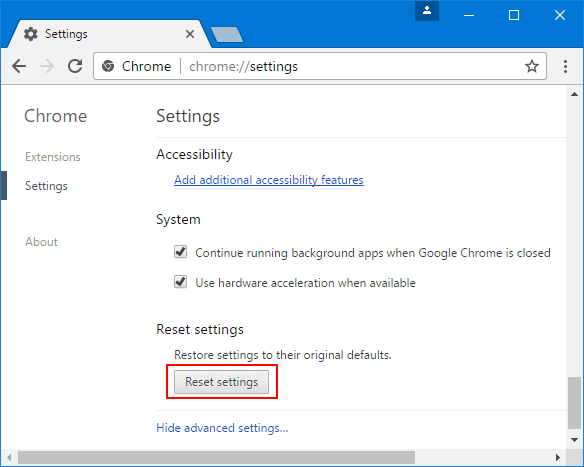
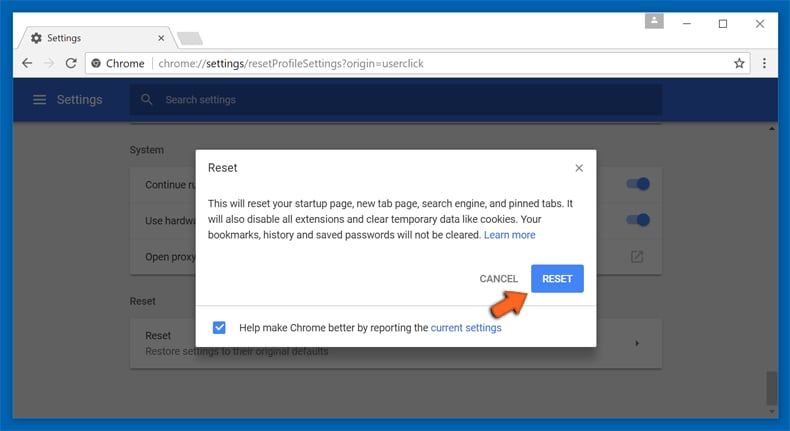
In the next opened window, confirm that you want to reset the Google Chrome settings by click on the “Reset” button.
Remove Malware plugins (including all other doubtful plug-ins) from Firefox Mozilla
Open the Firefox menu and select “Add-ons”. Click “Extensions”. Select all the recently installed browser plug-ins.
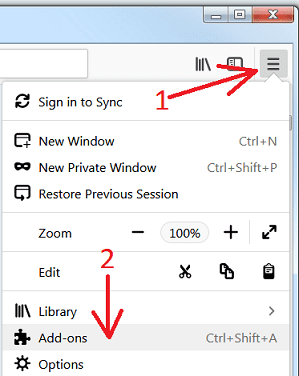
Optional Method
If you face problems in Malware removal then you have the option to rese the settings of Mozilla Firefox.
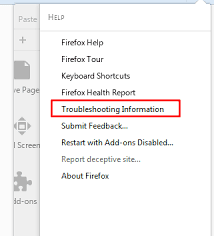
Open the browser (Mozilla Firefox) and click on the “menu” and then click on “Help”.
Choose “Troubleshooting Information”
In the newly opened pop-up window, click “Refresh Firefox” button
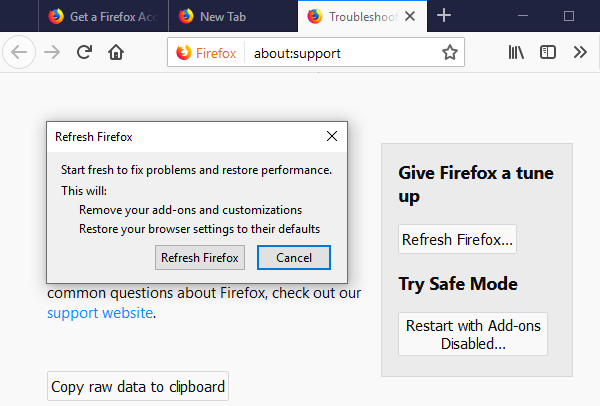
The next step is to confirm that really want to reset the Mozilla Firefox settings to its default by clicking on “Refresh Firefox” button.
Remove Malicious Extension from Safari
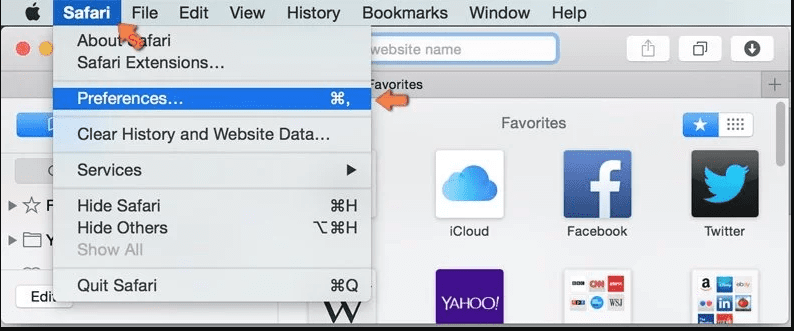
Open the Safari and go to its “Menu” and select “Preferences”.
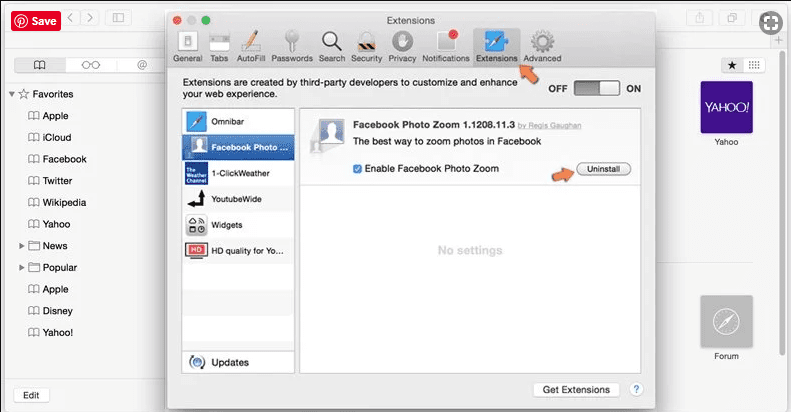
Click on the “Extension” and select all the recently installed “Extensions” and then click on “Uninstall”.
Optional Method
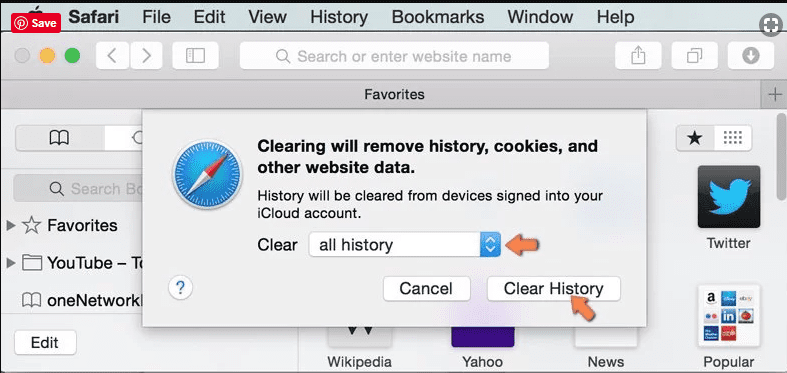
Open the “Safari” and go menu. In the drop-down menu, choose “Clear History and Website Data”.
In the newly opened window, select “All History” and then press on “Clear History” option.
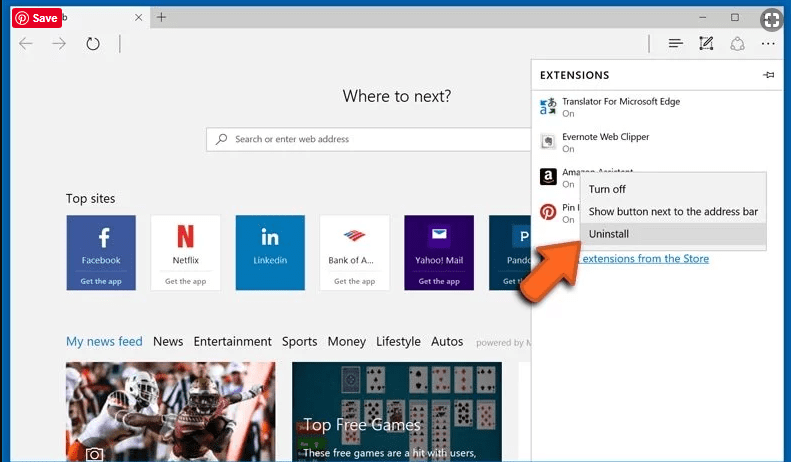
Delete Malware (malicious add-ons) from Microsoft Edge
Open Microsoft Edge and go to three horizontal dot icons at the top right corner of the browser. Select all the recently installed extensions and right click on the mouse to “uninstall”
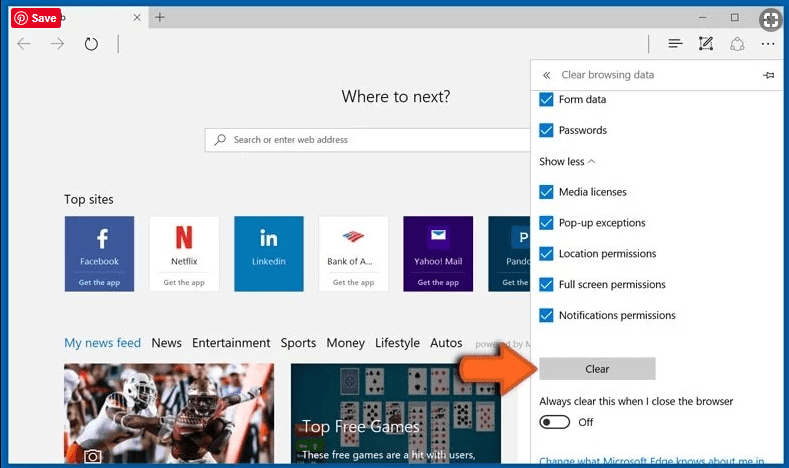
Optional Method
Open the browser (Microsoft Edge) and select “Settings”
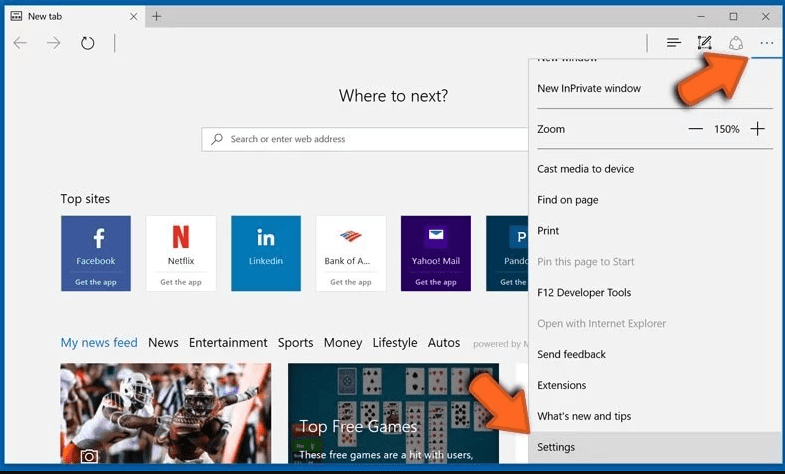
Next steps is to click on “Choose what to clear” button
Click on “show more” and then select everything and then press on “Clear” button.
How to prevent Malware infection?
As soon as Malware infiltrates the PC system, it starts carrying out malicious activities in the background and may lead to a number of unpleasant issues. To avoid getting infected with such browser-based pests, below are some steps you can take:
- Download software from reputable sources: Only download software from reputable websites, such as the official page of the software vendor or well-known download portals. Avoid downloading software from third-party websites or peer-to-peer networks, as these are often sources of bundled adware.
- Pay attention during the installation process: When installing software, pay attention to each step of the installation process. Look for the checkboxes that may indicate the installation of additional software, such as adware or browser extensions. Uncheck these boxes if you don’t want to install the additional software.
- Choose custom installation: During the installation process, choose the custom installation option instead of the default or express installation. This will allow you to select which components to install and to opt-out of installing any bundled adware or other unwanted software.
- Read the End User License Agreement (EULA): Read the EULA carefully before installing any software. Look for clauses that may allow the installation of additional software or adware like Malware. If EULA contains such clauses, reconsider installing the software.
- Use a reputable web browser: Choose a reputable web browser, such as Google Chrome or Mozilla Firefox, and keep it up-to-date with the latest security patches.
- Install ad-blockers and pop-up blockers: You should use ad-blockers and pop-up blockers to prevent unwanted ads and pop-ups from appearing on your computer screen. Some web browsers have built-in ad-blocker and pop-up blockers, or you can install browser extensions that provide this functionality.
- Be careful when clicking on links: Don’t click on links in emails or on websites unless you are sure they are legitimate. Check the URL and ensure it is spelled correctly and is the correct website. Be wary of shortened URLs or URLs that lead to suspicious or unknown websites.
- Keep your web browser and operating system up-to-date: Regularly install software updates and security patches for your web browser and operating system. This will help to close any security vulnerabilities that adware, hijacker and other malware may exploit.
- Use a reputable antivirus program: A good antivirus program can detect and block infections like Malware and other malware before they can infect your computer. Make sure you choose a reliable antivirus suite and keep it up-to-date with the latest virus definitions.
By following these steps, you can minimize the risk of potentially unwanted program intrusion and keep your PC system safe and secure.
Conclusion:
To sum up, Malware can cause significant problems for computer users, including unwanted browser redirects, changes to homepage and search engine settings, and even the installation of additional malware. These infections typically result from downloading and installing software from untrusted sources or clicking on suspicious links. To prevent browser hijackers or adware, it is important to be cautious when downloading and installing software, use reputable antivirus tool, and keep browsers and operating systems updated with the latest security patches.
Related FAQs about Malware
What are the Symptoms of Browser-hijacker (Malware)?
The common symptoms of Malware infection include changes to the default homepage and search engine, unwanted toolbars and extensions, pop-up ads, and redirects to unfamiliar websites. Additionally, the browser may slow down or crash frequently, and search results may be manipulated or irrelevant to the query.
What Should I do if my PC gets infected with virus like Malware?
If your computer is infected with this browser-based threat, you should immediately run a virus scan using reputable antivirus software. If the software detects the malware, you should follow the removal instructions provided by it to eliminate the infection and restore your browser settings to default.
How can I protect my password and other personal credentials from Malware?
To protect your password and other sensitive information from Malware, you should employ reputable antivirus suite, enable two-factor authentication on all accounts, and use strong and unique passwords for each account. Also, you should avoid clicking on suspicious links or downloading software from untrusted sources.
Why I should trust your research conducted on Malware?
It’s important to mention that our research is conducted independently and with the assistance of unbiased security experts, who provide us with daily updates on the latest definitions and threats related to malware, adware, and browser hijackers. Moreover, our study on the Malware threat is supported by VirusTotal.
Special Offer (For Windows)
Malware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wait for next 48 hours. If you intend to remove detected threats instantly, then you will have to buy its licenses version that will activate the software fully.
Special Offer (For Macintosh) If you are a Mac user and Malware has affected it, then you can download free antimalware scanner for Mac here to check if the program works for you.