Remove Erica ransomware [File Recovery Instructions]
Easy methods to delete Erica ransomware
Erica ransomware is the name of data encrypting malware that was discovered by Petrovic. It is operated by the cyber criminal with the main intention to lock down the target system and encrypted files until a ransom is paid. It has been infected millions of Windows based operating system all over the world. During the encryption process, all affected files are renamed with a random character string.
Once encrypted successfully, it drops ransom demanding messages named “Readme.[random_string].txt and dropped into compromised folders. The created ransom demanding message states victims that their device has been encrypted and the files stored on them have been encrypted and makes them totally useless. In order to restore the files, users are instructed to contact the cyber criminals through the provided email addresses.
Victims are also warned to contact criminals on the given time otherwise every fifteen minutes, a file is deleted. According to the message, the deletion feature can be disabled by pressing Alt + F9 keys. The note also states that cyber criminals are only interested in devices that store more than ten thousand files. Victims are also offered free decryption test of some encrypted files but there is no guarantee that this claim is true.
Unluckily, in most cases of ransomware infections decryption cannot be done without the involvement of cyber criminals. It might be possible if malicious program is still in development or has bugs or flaws. Whatever the case, it is expressly advised against meeting the ransom demands. Often despite paying money, users do not receive the promised decryption tools/software. Thus, they might experience financial loss and their data remains encrypted.
How to decrypt files without paying money?
There is no any tool available which can recover your files. It is only a trick to makes illegal money by making fool to innocent users. The only way to decrypt files is to remove Erica ransomware completely from the computer. To delete this malware, users are recommended to use some reliable antivirus removal tool. After finishing the removal process, users can easily recover files by using the backup file available or using third party recovery software.
How Erica ransomware infect my system?
Ransomware and other malware are distributed via various sources. Some of them are spam campaigns, untrustworthy download channels, trojans, illegal activation tools and illegitimate updates. Among all, the spam campaigns are the most common and most used methods. spam campaigns are mass scale operations during which hundreds or thousands of scam emails are sent to the recipients. These emails contain infectious attachments or download links of suspicious files. When the files are opened or executed, malware gets downloaded or installed. Secondly, cracking tools can cause infections instead of activating licensed products. Thirdly, fake updater’s infect PC by exploiting flaws of outdated programs or by installing malicious software rather than the actual updates.
Remove Erica ransomware
Complete removal instructions have been discussed below under this post. Follow it so that you will not find any trouble when performing virus removal process. Users are recommended to use some reliable antivirus removal tool that has the capability to remove Erica ransomware completely and safely from the system.
Text presented in Erica ransomware’s text file (“Readme.[random_string].txt”):
I знову здрастуйте. Ми повернулися пiсля тривалого часу, щоб довести, що можна залишатися безкарним.
And hello again. We returned after a long time to prove that we can go unpunished.
Erica $$$
Key (Do not change it)
–
Your computer/network has been encrypted!
If you want to return the files, then write to the mail.
One file will be deleted every 15 minutes. Hurry up. Disabled by pressing Alt + F9.
[email protected] – Contact us
[email protected] – Contact us
[email protected] – Contact us
[email protected] – Contact us
[email protected] – Contact us
[email protected] – Contact us
[email protected] – Contact us
[email protected] – Reserve
[email protected] – Reserve
[email protected] – Reserve
We are not interested in computers that have less than 10,000 thousand files that we need.
If you have less, then write to us and we will decrypt your network for free. The number of encrypted files on your computer or your network 16172.
We value our reputation and are not going to deceive you.
If you do not pay us, we will give all the data to your competitors!!!
Special Offer (For Windows)
Erica ransomware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Data Recovery Offer
We Suggest you to choose your lately created backup files in order to restore your encrypted files, however in case if you don’t have any such backups, you can try a data recovery tool to check if you can restore your lost data.
Antimalware Details And User Guide
Step 1: Remove Erica ransomware through “Safe Mode with Networking”
Step 2: Delete Erica ransomware using “System Restore”
Step 1: Remove Erica ransomware through “Safe Mode with Networking”
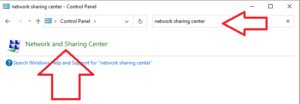
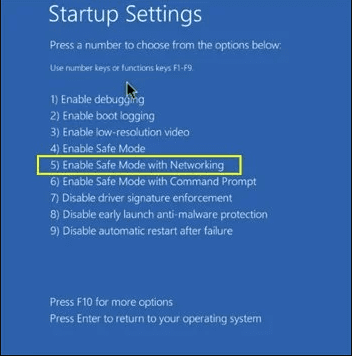
For Windows XP and Windows 7 users: Boot the PC in “Safe Mode”. Click on “Start” option and continuously press on F8 during the start process until the “Windows Advanced Option” menu appears on the screen. Choose “Safe Mode with Networking” from the list.
Now, a windows homescreen appears on the desktop and work-station is now working on “Safe mode with networking”.
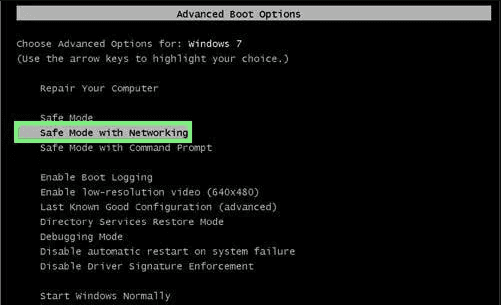
For Windows 8 Users: Go to the “Start Screen”. In the search results select settings, type “Advanced”. In the “General PC Settings” option, choose “Advanced startup” option. Again, click on the “Restart Now” option. The work-station boots to “Advanced Startup Option Menu”. Press on “Troubleshoot” and then “Advanced options” button. In the “Advanced Option Screen”, press on “Startup Settings”. Again, click on “Restart” button. The work-station will now restart in to the “Startup Setting” screen. Next is to press F5 to boot in Safe Mode in Networking.
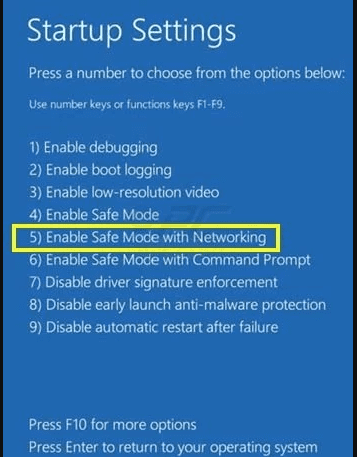
For Windows 10 Users: Press on Windows logo and on the “Power” icon. In the newly opened menu, choose “Restart” while continuously holding “Shift” button on the keyboard. In the new open “Choose an option” window, click on “Troubleshoot” and then on the “Advanced Options”. Select “Startup Settings” and press on “Restart”. In the next window, click on “F5” button on the key-board.
Step 2: Delete Erica ransomware using “System Restore”
Log-in to the account infected with Erica ransomware. Open the browser and download a legitimate anti-malware tool. Do a full System scanning. Remove all the malicious detected entries.
Special Offer (For Windows)
Erica ransomware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Data Recovery Offer
We Suggest you to choose your lately created backup files in order to restore your encrypted files, however in case if you don’t have any such backups, you can try a data recovery tool to check if you can restore your lost data.
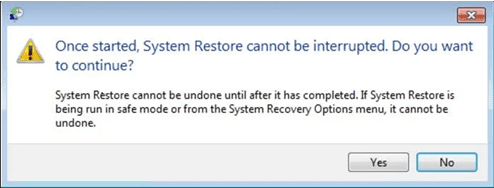
In case if you cannot start the PC in “Safe Mode with Networking”, Try using “System Restore”
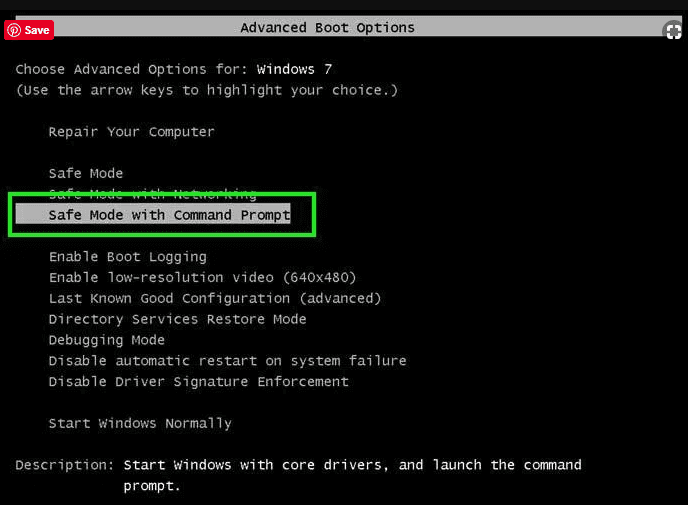
- During the “Startup”, continuously press on F8 key until the “Advanced Option” menu appears. From the list, choose “Safe Mode with Command Prompt” and then press “Enter”
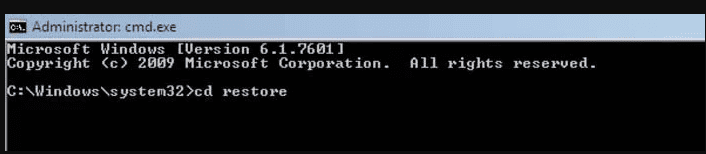
- In the new opened command prompt, enter “cd restore” and then press “Enter”.
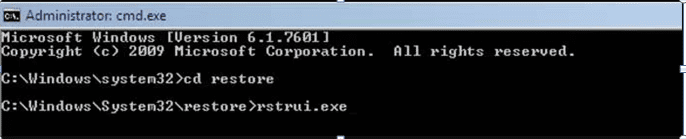
- Type: rstrui.exe and Press “ENTER”
- Click “Next” on the new windows
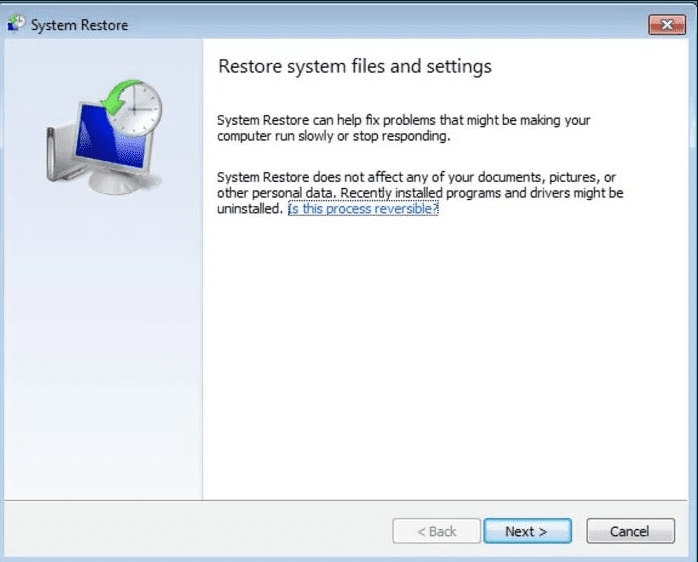
- Choose any of the “Restore Points” and click on “Next”. (This step will restore the work-station to its earlier time and date prior to Erica ransomware infiltration in the PC.
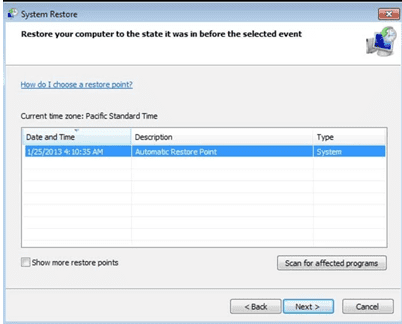
- In the newly opened windows, press on “Yes”.
Once your PC gets restored to its previous date and time, download the recommended anti-malware tool and perform a deep scanning in order to remove Erica ransomware files if they left in the work-station.
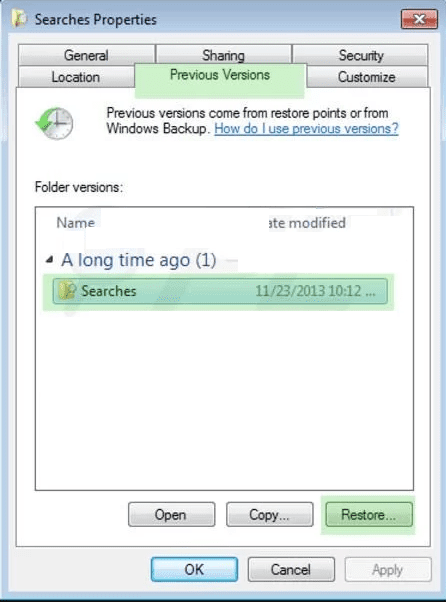
In order to restore the each (separate) file by this ransomware, use “Windows Previous Version” feature. This method is effective when “System Restore Function” is enabled in the work-station.
Important Note: Some variants of Erica ransomware delete the “Shadow Volume Copies” as well hence this feature may not work all the time and is applicable for selective computers only.
How to Restore Individual Encrypted File:
In order to restore a single file, right click on it and go to “Properties”. Select “Previous Version” tab. Select a “Restore Point” and click on “Restore” option.
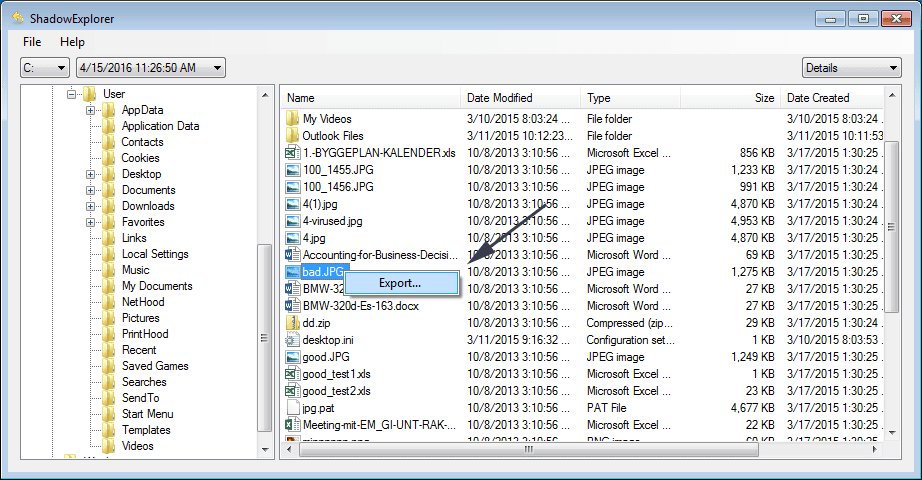
In order to access the files encrypted by Erica ransomware, you can also try using “Shadow Explorer”. In order to get more information on this application, press here.
Important: Data Encryption Ransomware are highly dangerous and it is always better that you take precautions to avoid its attack on your work-station. It is advised to use a powerful anti-malware tool in order to get protection in real-time. With this help of “SpyHunter”, “group policy objects” are implanted in the registries in order to block harmful infections like Erica ransomware.
Also, In Windows 10, you get a very unique feature called “Fall Creators Update” that offer “Controlled Folder Access” feature in order to block any kind of encryption to the files. With the help of this feature, any files stored in the locations such as “Documents”, “Pictures”, “Music”, “Videos”, “Favorites” and “Desktop” folders are safe by default.
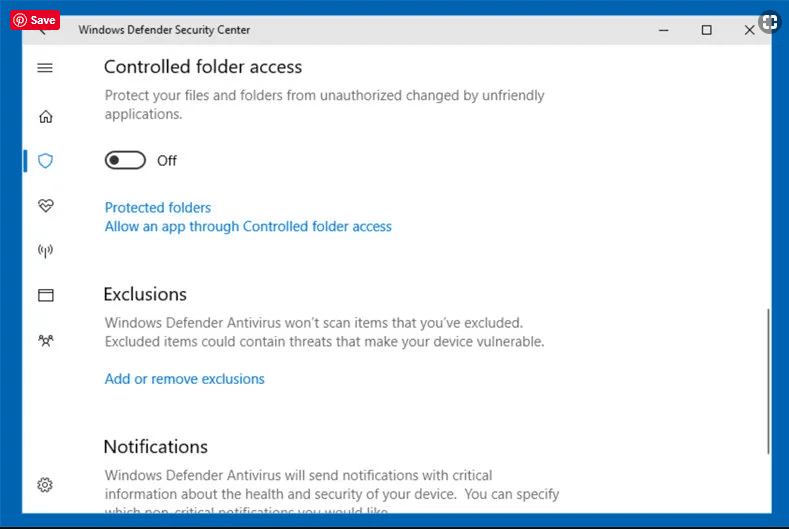
It is very important that you install this “Windows 10 Fall Creators Update” in your PC to protect your important files and data from ransomware encryption. The more information on how to get this update and add an additional protection form rnasomware attack has been discussed here.
How to Recover the Files Encrypted by Erica ransomware?
Till now, you would have understood that what had happed to your personal files that got encrypted and how you can remove the scripts and payloads associated with Erica ransomware in order to protect your personal files that has not been damaged or encrypted until now. In order to retrieve the locked files, the depth information related to “System Restore” and “Shadow Volume Copies” has already been discussed earlier. However, in case if you are still unable to access the encrypted files then you can try using a data recovery tool.
Use of Data Recovery Tool
This step is for all those victims who have already tries all the above mentioned process but didn’t find any solution. Also it is important that you are able to access the PC and can install any software. The data recovery tool works on the basis of System scanning and recovery algorithm. It searches the System partitions in order to locate the original files which were deleted, corrupted or damaged by the malware. Remember that you must not re-install the Windows OS otherwise the “previous” copies will get deleted permanently. You have to clean the work-station at first and remove Erica ransomware infection. Leave the locked files as it is and follow the steps mentioned below.
Step1: Download the software in the work-station by clicking on the “Download” button below.
Step2: Execute the installer by clicking on downloaded files.
Step3: A license agreement page appears on the screen. Click on “Accept” to agree with its terms and use. Follow the on-screen instruction as mentioned and click on “Finish” button.

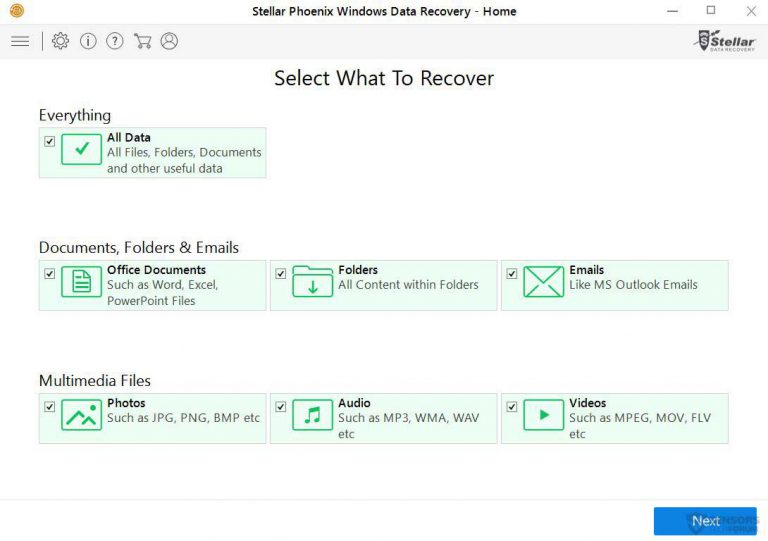
Step4: Once the installation gets completed, the program gets executed automatically. In the newly opened interface, select the file types that you want to recover and click on “Next”.
Step5: You can select the “Drives” on which you want the software to run and execute the recovery process. Next is to click on the “Scan” button.
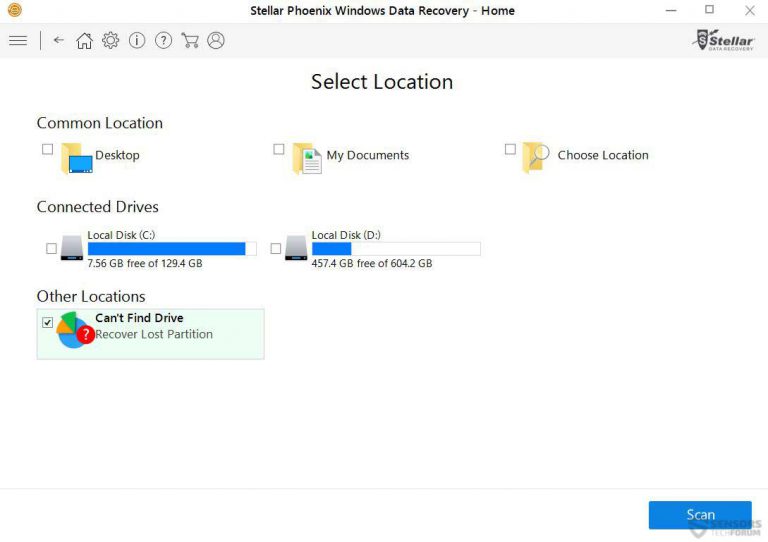
Step6: Based on drive you select for scanning, the restore process begins. The whole process may take time depending on the volume of the selected drive and number of files. Once the process gets completed, a data explorer appears on the screen with preview of that data that is to be recovered. Select the files that you want to restore.

Step7. Next is to locate the location where you want to saver the recovered files.

Special Offer (For Windows)
Erica ransomware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Data Recovery Offer
We Suggest you to choose your lately created backup files in order to restore your encrypted files, however in case if you don’t have any such backups, you can try a data recovery tool to check if you can restore your lost data.