How to remove .Lisp ransomware and recover encrypted files
Complete .Lisp ransomware removal tips
.Lisp ransomware is a huge risk ransomware infection, belongs to DJVU ransomware family. Like all other predecessors, Lisp encrypts stored files, renames them and then drops _readme.txt file to put ransom demand. Files encrypted by this ransomware will receive .Lisp extension. For example, a file named 1.jpg would appear something similar to 1.jpg.lisp, “2.jpg” to “2.jpg.lisp”, and so forth.
The text message within _readme.txt file informs people about the ransomware attacks and files encryption happened on their devices due to which all the files including images, audios, videos, documents, and presentations become inaccessible. It states that the files can be recovered. For this, victims are asked to contact the crooks behind .Lisp ransomware developers via the provided email address ([email protected] or [email protected]). According to the ransom note, the malicious actors have the unique decryption tool that helps in files recovery.
The price of the decryption tool, as mentioned in the ransom note, is $980. However, for the users who establish a contact with the crooks within 72 hours can get a huge 50% discount of the price of the tool and for them this price will drop to $490. Prior to the payment, the victims are asked to send 1 encrypted file less than 1 MB and must not contain any valuable information. The crooks claim to provide free decryption of this tool as a proof that their decryption tool is really working. The ransom message also warns people not to rename the filenames of the encrypted files as this will result into permanent data loss.
Here is the full text presented on the .Lisp ransomware’s created _readme.txt file:
ATTENTION!
Don’t worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-jydQMZP2Ie
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
To get this software you need write on our e-mail:
Reserve e-mail address to contact us:
Your personal ID:
–
Pay ransom is not a good option
Very often crooks who designed the ransomware are the only people who have the right decryption tools. There are no third party tools available that can decrypt .Lisp ransomware encrypted files. However, it is not recommended to contact/ pay to the crooks under any circumstances. It is because these people often do not send the decryption tool even if all their demands are met. The only possible way to recover the files without the interference of the crooks behind it is to restore the files using backups. The volume shadow Copies are other data recovery option available for you, if .Lisp ransomware virus does not corrupt this automatically created backup option during the process the files encryption is done. Also, data recovery tools are nowadays designed with special functionalities added and so you can keep such tools as one of the data recovery option.
However, before attempting to recover the files using any of the stated methods, make sure that the malware is not present inside the system. If it is, it will interfere during the files recovery process and make the files recovery impossible for you by corrupting the tool you are using. The malware removal is necessary for several more reasons. The major ones are the risks associated with the various operations (depending upon the modules used) that the ransomware does on the system background, if it stays for a long time. The developers could use it to inject other malicious malware or steal sensitive and personal data and use them in fraudulent transactions, purchases and other severe activities that cost on privacy and cause identity exposure. To remove .Lisp ransomware, we recommend you run a full system scan using some reputable antivirus tool. You can use our manual guide provided below the post for the same.
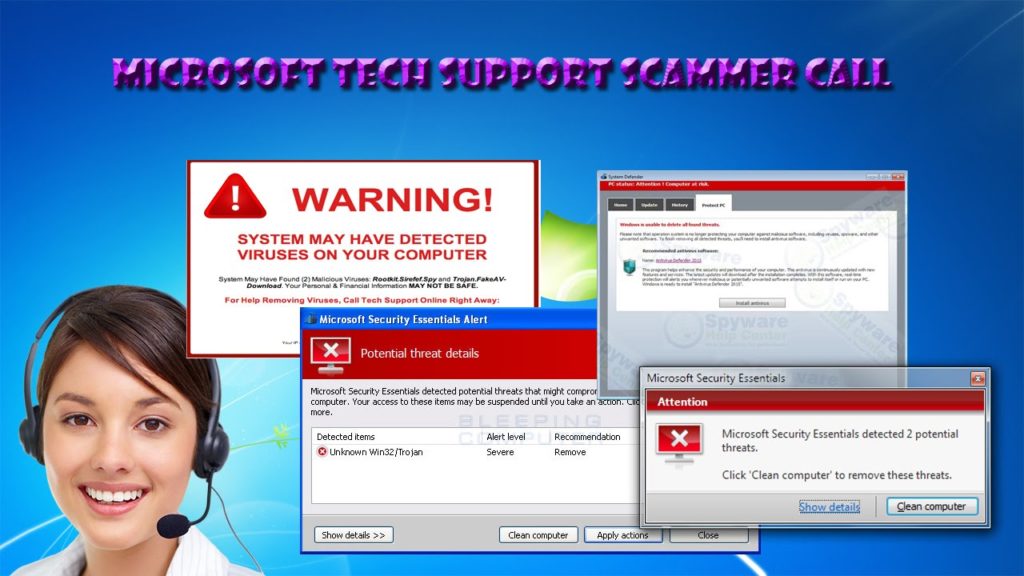
How did .Lisp ransomware intrude in?
Ransomware and other malicious malware are often distributed through Trojans, mal-spam campaigns, unreliable software download sources/ channels, fake software updating and unofficial activation tools. Trojans are malicious programs that are designed to download/ install additional malware. Mal-spam campaigns are used to send spam emails that contain infectious files or links for such files. If downloaded or opened, such files initiate the malware download/ installation process. Examples of such files are malicious Microsoft Office or PDF documents, JavaScript files, archive files and executable files. Unreliable downloading sources like p2p networks, free file hosting sites and third party downloaders/ installers spread malware by presenting it as legit software. Fake software updaters infect computers either by installing malware instead of updates, fixes for installed software or by exploiting bugs, flaws of installed software that is not up-to-date. Unofficial activation tools infect systems simply by installing malware instead of bypassing activation keys for paid software.
How to prevent ransomware infection?
Attachments or website links should never be opened if they are presented on any emails whose senders’ addresses seem suspicious and irrelevant. Files and programs should be downloaded only from official websites and direct links. Other sources, tools like third party downloaders, unofficial websites, p2p networks, free file hosting sites and etc should never be used. Unofficial, fake software updating and activation should never be used as well. Software update and activation should be done using official software developers’ tools/functions only. Additionally, a computer should have a reputable antivirus tool and this tool should be up-to-date. If .Lisp ransomware already infiltrates in, run a full system scan using some reputable antivirus tool to automatically elimination this ransomware.
Special Offer (For Windows)
.Lisp ransomware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Data Recovery Offer
We Suggest you to choose your lately created backup files in order to restore your encrypted files, however in case if you don’t have any such backups, you can try a data recovery tool to check if you can restore your lost data.
Antimalware Details And User Guide
Step 1: Remove .Lisp ransomware through “Safe Mode with Networking”
Step 2: Delete .Lisp ransomware using “System Restore”
Step 1: Remove .Lisp ransomware through “Safe Mode with Networking”
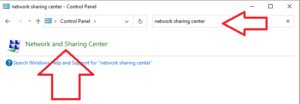
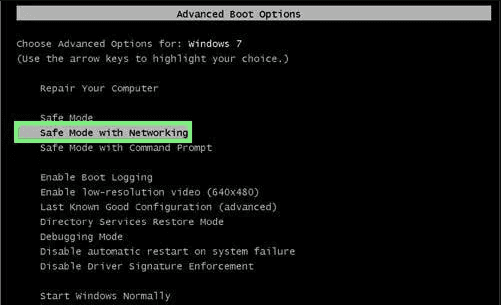
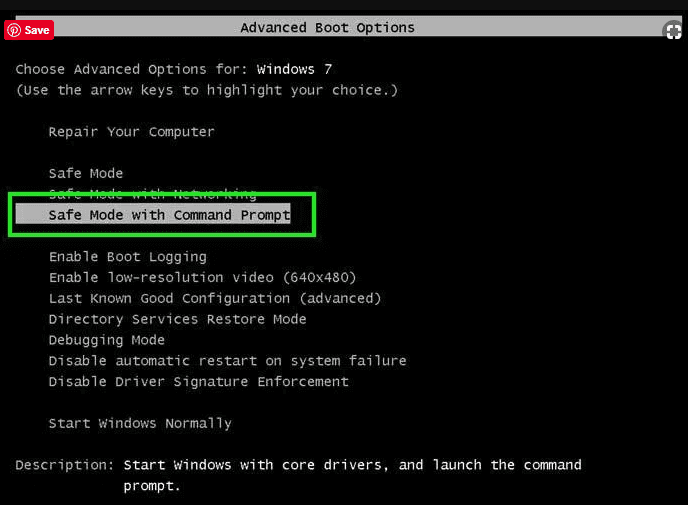
For Windows XP and Windows 7 users: Boot the PC in “Safe Mode”. Click on “Start” option and continuously press on F8 during the start process until the “Windows Advanced Option” menu appears on the screen. Choose “Safe Mode with Networking” from the list.
Now, a windows homescreen appears on the desktop and work-station is now working on “Safe mode with networking”.
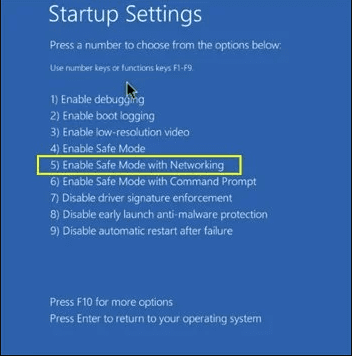
For Windows 8 Users: Go to the “Start Screen”. In the search results select settings, type “Advanced”. In the “General PC Settings” option, choose “Advanced startup” option. Again, click on the “Restart Now” option. The work-station boots to “Advanced Startup Option Menu”. Press on “Troubleshoot” and then “Advanced options” button. In the “Advanced Option Screen”, press on “Startup Settings”. Again, click on “Restart” button. The work-station will now restart in to the “Startup Setting” screen. Next is to press F5 to boot in Safe Mode in Networking.
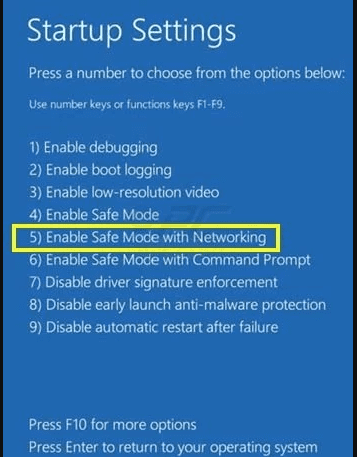
For Windows 10 Users: Press on Windows logo and on the “Power” icon. In the newly opened menu, choose “Restart” while continuously holding “Shift” button on the keyboard. In the new open “Choose an option” window, click on “Troubleshoot” and then on the “Advanced Options”. Select “Startup Settings” and press on “Restart”. In the next window, click on “F5” button on the key-board.
Step 2: Delete .Lisp ransomware using “System Restore”
Log-in to the account infected with .Lisp ransomware. Open the browser and download a legitimate anti-malware tool. Do a full System scanning. Remove all the malicious detected entries.
Special Offer (For Windows)
.Lisp ransomware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Data Recovery Offer
We Suggest you to choose your lately created backup files in order to restore your encrypted files, however in case if you don’t have any such backups, you can try a data recovery tool to check if you can restore your lost data.
In case if you cannot start the PC in “Safe Mode with Networking”, Try using “System Restore”
- During the “Startup”, continuously press on F8 key until the “Advanced Option” menu appears. From the list, choose “Safe Mode with Command Prompt” and then press “Enter”
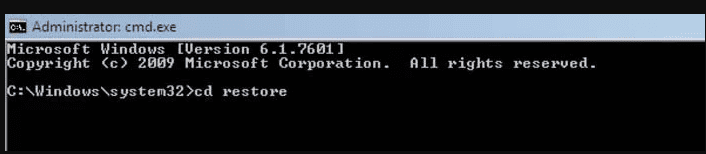
- In the new opened command prompt, enter “cd restore” and then press “Enter”.
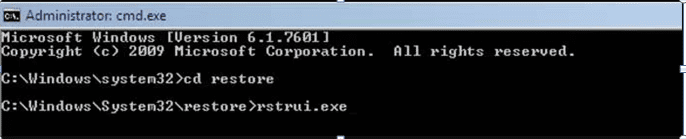
- Type: rstrui.exe and Press “ENTER”
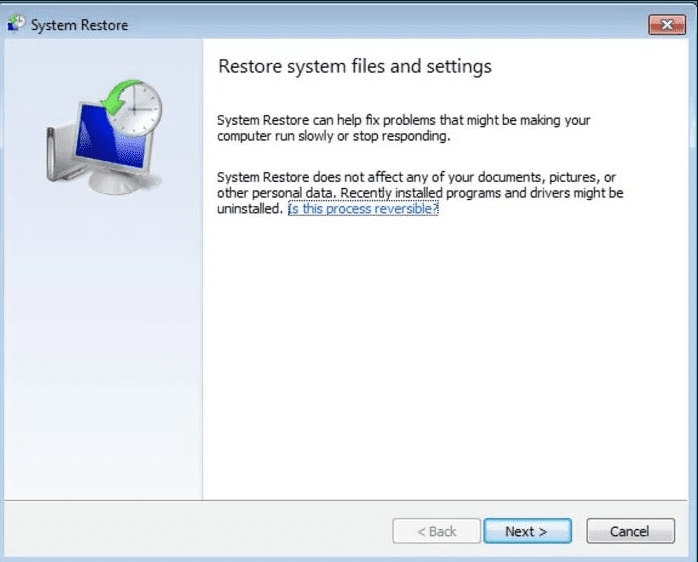
- Click “Next” on the new windows
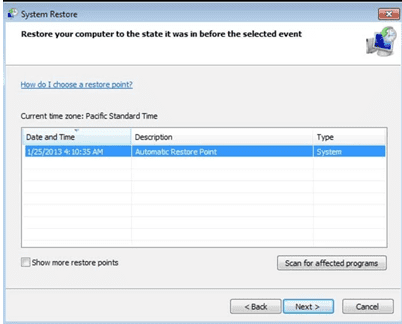
- Choose any of the “Restore Points” and click on “Next”. (This step will restore the work-station to its earlier time and date prior to .Lisp ransomware infiltration in the PC.
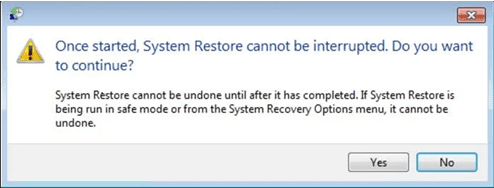
- In the newly opened windows, press on “Yes”.
Once your PC gets restored to its previous date and time, download the recommended anti-malware tool and perform a deep scanning in order to remove .Lisp ransomware files if they left in the work-station.
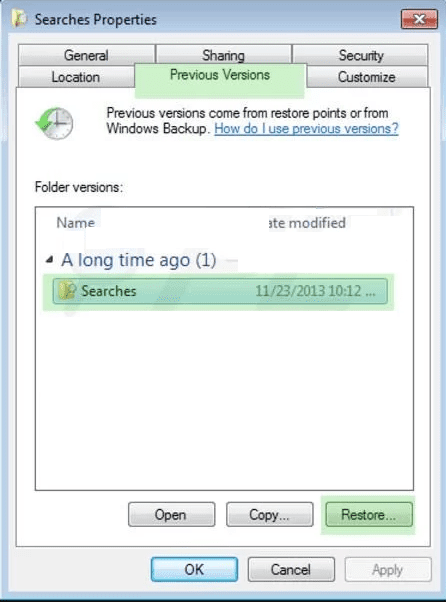
In order to restore the each (separate) file by this ransomware, use “Windows Previous Version” feature. This method is effective when “System Restore Function” is enabled in the work-station.
Important Note: Some variants of .Lisp ransomware delete the “Shadow Volume Copies” as well hence this feature may not work all the time and is applicable for selective computers only.
How to Restore Individual Encrypted File:
In order to restore a single file, right click on it and go to “Properties”. Select “Previous Version” tab. Select a “Restore Point” and click on “Restore” option.
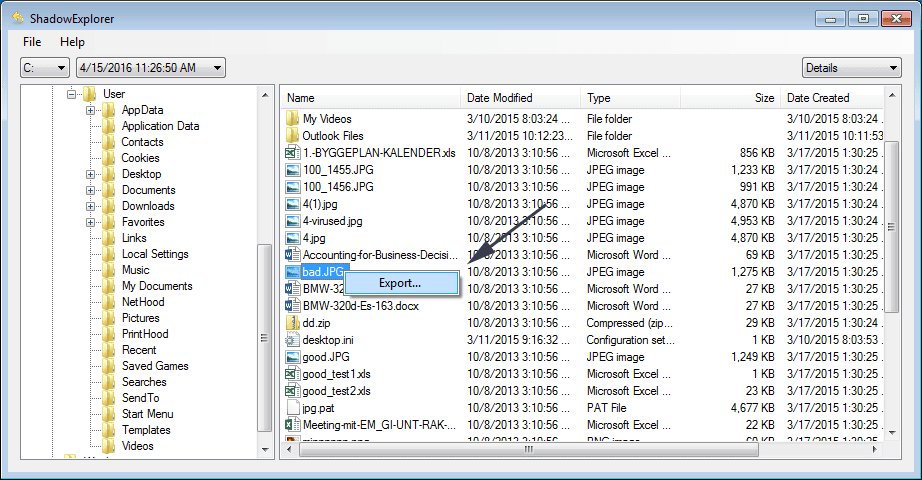
In order to access the files encrypted by .Lisp ransomware, you can also try using “Shadow Explorer”. In order to get more information on this application, press here.
Important: Data Encryption Ransomware are highly dangerous and it is always better that you take precautions to avoid its attack on your work-station. It is advised to use a powerful anti-malware tool in order to get protection in real-time. With this help of “SpyHunter”, “group policy objects” are implanted in the registries in order to block harmful infections like .Lisp ransomware.
Also, In Windows 10, you get a very unique feature called “Fall Creators Update” that offer “Controlled Folder Access” feature in order to block any kind of encryption to the files. With the help of this feature, any files stored in the locations such as “Documents”, “Pictures”, “Music”, “Videos”, “Favorites” and “Desktop” folders are safe by default.
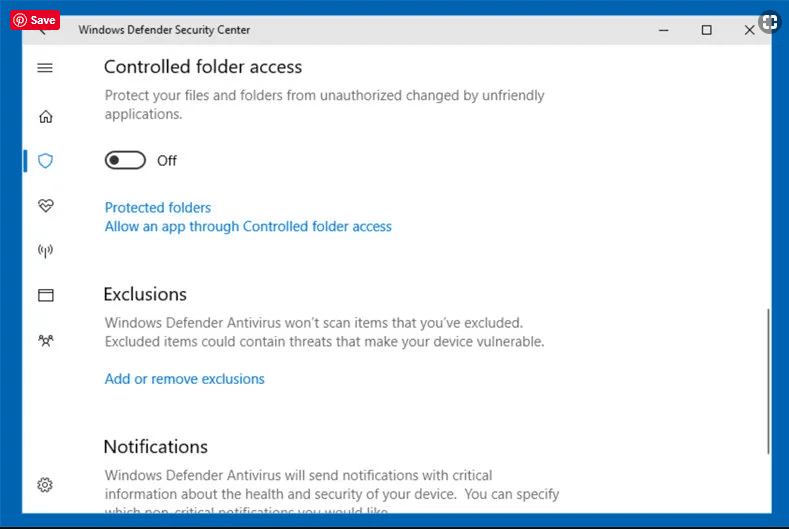
It is very important that you install this “Windows 10 Fall Creators Update” in your PC to protect your important files and data from ransomware encryption. The more information on how to get this update and add an additional protection form rnasomware attack has been discussed here.
How to Recover the Files Encrypted by .Lisp ransomware?
Till now, you would have understood that what had happed to your personal files that got encrypted and how you can remove the scripts and payloads associated with .Lisp ransomware in order to protect your personal files that has not been damaged or encrypted until now. In order to retrieve the locked files, the depth information related to “System Restore” and “Shadow Volume Copies” has already been discussed earlier. However, in case if you are still unable to access the encrypted files then you can try using a data recovery tool.
Use of Data Recovery Tool
This step is for all those victims who have already tries all the above mentioned process but didn’t find any solution. Also it is important that you are able to access the PC and can install any software. The data recovery tool works on the basis of System scanning and recovery algorithm. It searches the System partitions in order to locate the original files which were deleted, corrupted or damaged by the malware. Remember that you must not re-install the Windows OS otherwise the “previous” copies will get deleted permanently. You have to clean the work-station at first and remove .Lisp ransomware infection. Leave the locked files as it is and follow the steps mentioned below.
Step1: Download the software in the work-station by clicking on the “Download” button below.
Step2: Execute the installer by clicking on downloaded files.
Step3: A license agreement page appears on the screen. Click on “Accept” to agree with its terms and use. Follow the on-screen instruction as mentioned and click on “Finish” button.

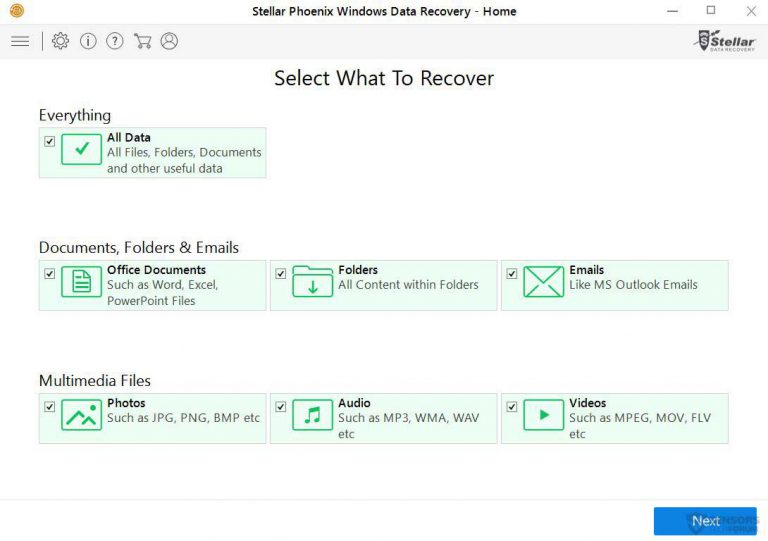
Step4: Once the installation gets completed, the program gets executed automatically. In the newly opened interface, select the file types that you want to recover and click on “Next”.
Step5: You can select the “Drives” on which you want the software to run and execute the recovery process. Next is to click on the “Scan” button.
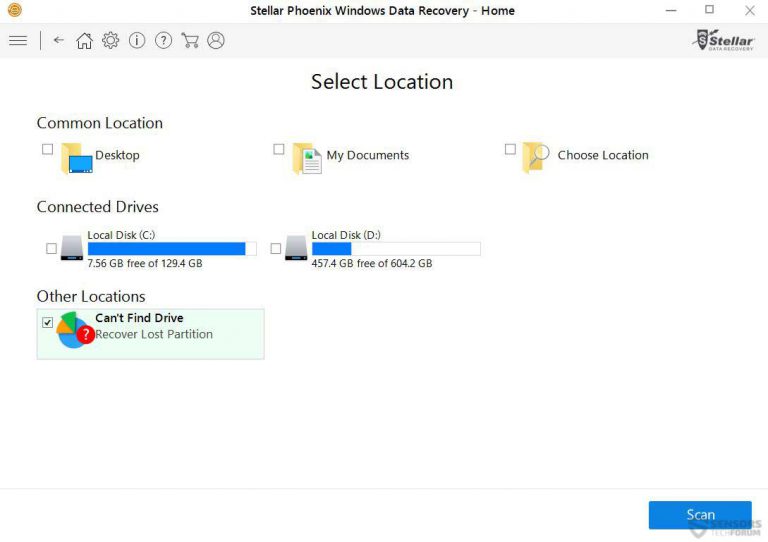
Step6: Based on drive you select for scanning, the restore process begins. The whole process may take time depending on the volume of the selected drive and number of files. Once the process gets completed, a data explorer appears on the screen with preview of that data that is to be recovered. Select the files that you want to restore.

Step7. Next is to locate the location where you want to saver the recovered files.

Special Offer (For Windows)
.Lisp ransomware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Data Recovery Offer
We Suggest you to choose your lately created backup files in order to restore your encrypted files, however in case if you don’t have any such backups, you can try a data recovery tool to check if you can restore your lost data.