How to remove Happy New Year Ransomware & rescue locked files
Delete Happy New Year Ransomware from PC (Removal Instructions)
According to expert, it is an updated variant of WannaCash ransomware and was discovered by Alex Svirid. This notorious malware has been programmed by cyber crooks in order to encrypt data and demand ransom money for its decryption. During encryption process, all files are renamed by using assigned file number, “file encrypted. Write to” (in Russian), the cyber criminals email address and by using “.happy new year” extension. Thus, it becomes impossible for users to access even single files. After completing encryption process, Happy New Year Ransomware drops a text file named “how to decrypt files” on the desktop which contain ransom note.
What does ransom note says?
Все значимые файлы на ВАШЕМ компьютере были упакованы в закодированные архивы с уникальными 100”значыми паролями, при использованием AES-256-битного шифрования.
Пораженные расширения и типы:
.doc .docx .xls .xlsx .xlst .ppt .pptx .accdb .rtf .pub .epub .pps .ppsm .pot .pages .odf .odt .ods .pdf .djvu .html .rtf .1Cv8ddb.1cl .1CD .cf .dt .efd .jpg .png ║
.mp4 .mov .avi .mpeg .flv .gif .bmp .3gp .zip .rar’+’ .7z .gzip .gz .tib .bak .iso .dat .cpp .h .pas .dpr .dproj .py .JS .css .php .asm .jar .apk .xml .psd .psb
.AEPX .PRPROJ .SWF .veg .txt .bd .default “Cookies” “History” “Login Data” “Favicons” “Web Data” “default”
Я гарантирую, что ВЫ сможете безопасно и легко восстановить все свои файлы.
Чтобы подтвердить мои честные намерения, отправьте мне на почту 2 разных файла, и ВЫ получите их расшифровку. Они НЕ должны быть документами (офис и тп).
почта: [email protected]
резеврная почта: [email protected]
Если не отвечаю в течении суток, пишите на резервную почту.
У ВАС есть ровно 7 дней на связь со мной. 03/01/20 числа в расшифровке ВАМ будет отказано.
Внимание !
* Не переименовывайте зашифрованные файлы.
* Не пытайтесь расшифровать ваши данные с помощью сторонних программ, это может привести к повреждению или другим неприятным последствиям.
Крайне не рекомендую обращаться за помощью на форумы антивирусных компаний. Только лишь потеряете время на ожидание отрицательного ответа.
More details about Happy New Year Ransomware
As usual, the text file message informs victims that all their files have been compressed into password, protected archive which are unique and contain one hundred characters. It encrypt all types of files like text, document, image, audio and archive file to a variety of browsing related data by using AES-256 cryptographic algorithm. Further, to gain the trust of users, they offer to decrypt by to two files free of charge. They also threaten users to contact ransomware developers within 7 days otherwise their request will be refused. In other words, victims who do not follow these instructions may not recover their data. They also warn user not to rename encrypted files by using third party tools otherwise it may cause permanent data loss.
Regrettably, in most cases of ransomware infections without the involvement of cyber criminals behind attack, decryption is impossible. It might possible that after paying money the decryption key they provide may contain bugs or flaws or it does not work properly. In such situations it is not safe to make a deal with the devil. Thus, to prevent Happy New Year Ransomware from further encryptions, it must be removed from system. Thus, there is only one solution to recover data is to use existing backup if created earlier before ransomware attack.
How did ransomware infect my PC?
There are multiple ways that can used to drop the payloads and harmful files in the PC. The most effective and popular of them are spam email attachments and suspicious web-links that are present in the email received from unknown senders, freeware and shareware downloads especially the cracks and hack tools, fake software update and so on.
As a preventive measure, it is strongly recommended to remove this kind of perilous infection in real-time. Don’t click on random links and pop-ups, avoid updating software from untrusted sources, don’t use peer-to-peer file sharing networks, careful about spam email campaigns and tricks that has been discussed above and many more.
How to remove Happy New Year Ransomware & retrieve files?
It is advised not to contact hackers and fulfill any of their demands. Rather your main aim is to remove Happy New Year Ransomware from PC so that other data will remain safe. Otherwise, it will damage your files and data and leads to serious privacy issue and theft of information including bank account details, geographical address, IP address and so on. Once malware gets removed, you can use the backup files (if available) for encrypted data restoration. The other option is to use the “Shadow Volume Copies” which is a temporary backup file created by the OS. The last option to restore the encrypted data is to use a powerful data recovery tool.
Threat specification
Name: Happy New Year Ransomware
Type: File-lockers, Cryptovirus, Ransomware
Extension used on locked files: .happy new year (also appended with number and developers email address)
Ransom note: как расшифровать файлы.txt
Contact of developer: [email protected] and [email protected]
Distribution: Spam email campaigns, harmful links and ads, peer-to-peer file sharing such as torrents, hidden attachment with freeware and shareware
Symptoms: A different unusual extension are added in the personal files and data stored in the PC hard-disk, A ransom note demanding money appears on the screen when you trying to access them.
Damage: Leads to data loss. Secretly adds other severe malware infection in the backdoor including password stealing Trojan, spyware and so on.
Removal and Data recovery: Advised to immediately scan the PC and remove all file viruses immediately. Once the malware gets removed, you can use the backup files for recovery. The other option is to use a data recovery tool.
Special Offer (For Windows)
Happy New Year Ransomware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Data Recovery Offer
We Suggest you to choose your lately created backup files in order to restore your encrypted files, however in case if you don’t have any such backups, you can try a data recovery tool to check if you can restore your lost data.
Antimalware Details And User Guide
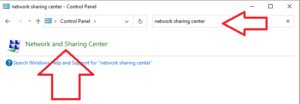
Step 1: Remove Happy New Year Ransomware through “Safe Mode with Networking”
Step 2: Delete Happy New Year Ransomware using “System Restore”
Step 1: Remove Happy New Year Ransomware through “Safe Mode with Networking”
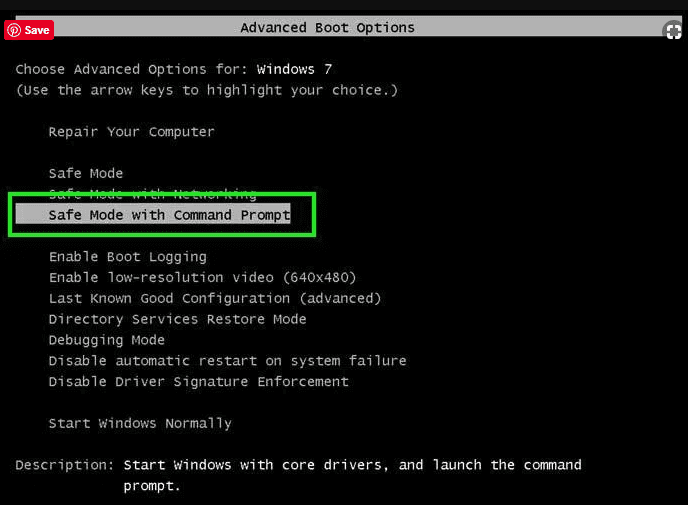
For Windows XP and Windows 7 users: Boot the PC in “Safe Mode”. Click on “Start” option and continuously press on F8 during the start process until the “Windows Advanced Option” menu appears on the screen. Choose “Safe Mode with Networking” from the list.
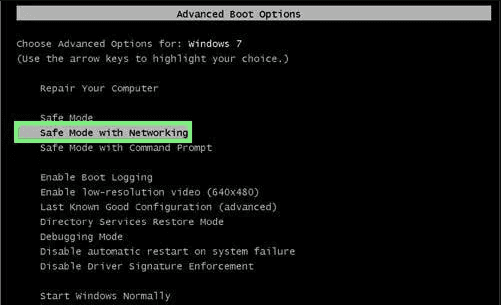
Now, a windows homescreen appears on the desktop and work-station is now working on “Safe mode with networking”.
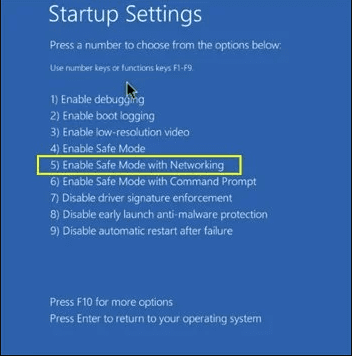
For Windows 8 Users: Go to the “Start Screen”. In the search results select settings, type “Advanced”. In the “General PC Settings” option, choose “Advanced startup” option. Again, click on the “Restart Now” option. The work-station boots to “Advanced Startup Option Menu”. Press on “Troubleshoot” and then “Advanced options” button. In the “Advanced Option Screen”, press on “Startup Settings”. Again, click on “Restart” button. The work-station will now restart in to the “Startup Setting” screen. Next is to press F5 to boot in Safe Mode in Networking.
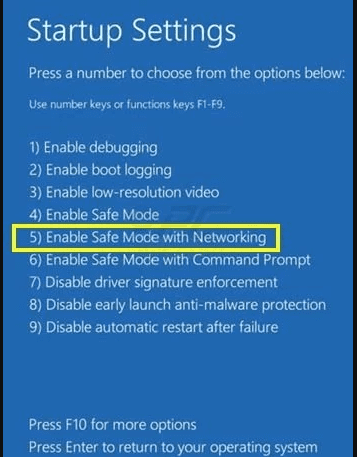
For Windows 10 Users: Press on Windows logo and on the “Power” icon. In the newly opened menu, choose “Restart” while continuously holding “Shift” button on the keyboard. In the new open “Choose an option” window, click on “Troubleshoot” and then on the “Advanced Options”. Select “Startup Settings” and press on “Restart”. In the next window, click on “F5” button on the key-board.
Step 2: Delete Happy New Year Ransomware using “System Restore”
Log-in to the account infected with Happy New Year Ransomware. Open the browser and download a legitimate anti-malware tool. Do a full System scanning. Remove all the malicious detected entries.
Special Offer (For Windows)
Happy New Year Ransomware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Data Recovery Offer
We Suggest you to choose your lately created backup files in order to restore your encrypted files, however in case if you don’t have any such backups, you can try a data recovery tool to check if you can restore your lost data.
In case if you cannot start the PC in “Safe Mode with Networking”, Try using “System Restore”
- During the “Startup”, continuously press on F8 key until the “Advanced Option” menu appears. From the list, choose “Safe Mode with Command Prompt” and then press “Enter”
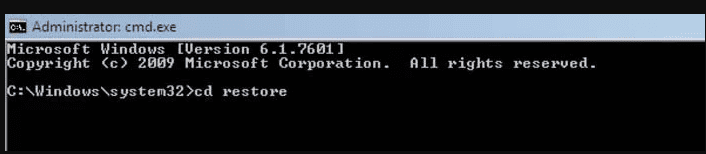
- In the new opened command prompt, enter “cd restore” and then press “Enter”.
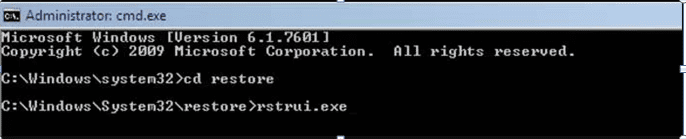
- Type: rstrui.exe and Press “ENTER”
- Click “Next” on the new windows
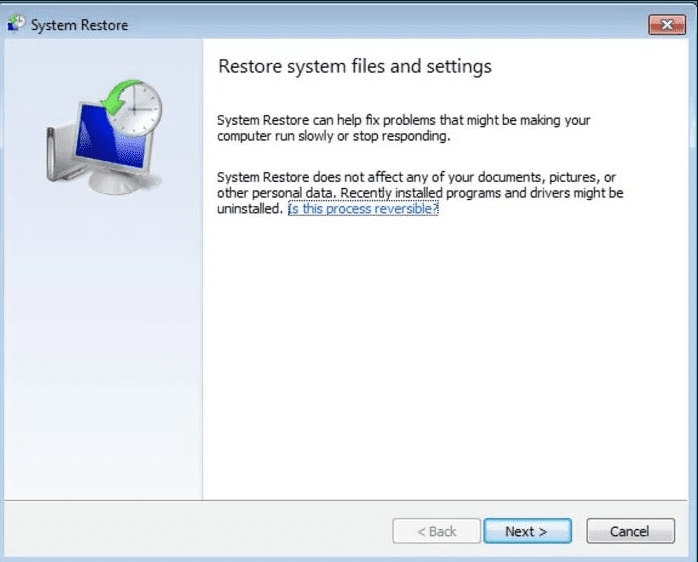
- Choose any of the “Restore Points” and click on “Next”. (This step will restore the work-station to its earlier time and date prior to Happy New Year Ransomware infiltration in the PC.
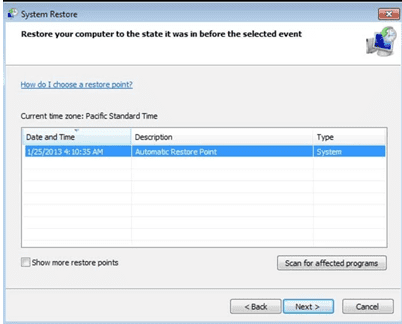
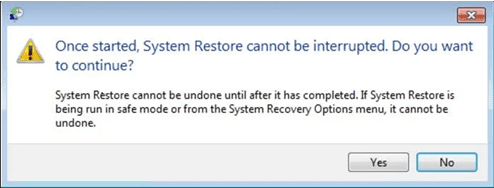
- In the newly opened windows, press on “Yes”.
Once your PC gets restored to its previous date and time, download the recommended anti-malware tool and perform a deep scanning in order to remove Happy New Year Ransomware files if they left in the work-station.
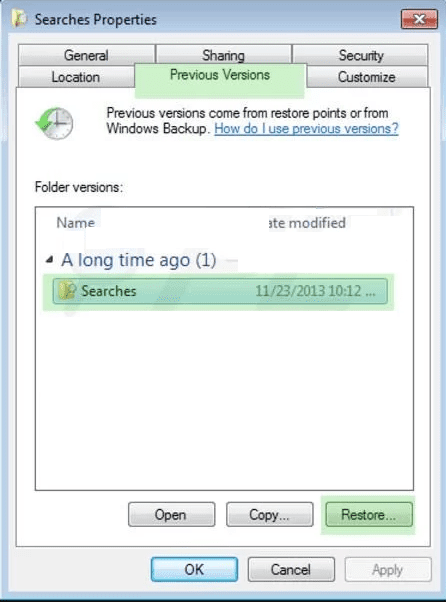
In order to restore the each (separate) file by this ransomware, use “Windows Previous Version” feature. This method is effective when “System Restore Function” is enabled in the work-station.
Important Note: Some variants of Happy New Year Ransomware delete the “Shadow Volume Copies” as well hence this feature may not work all the time and is applicable for selective computers only.
How to Restore Individual Encrypted File:
In order to restore a single file, right click on it and go to “Properties”. Select “Previous Version” tab. Select a “Restore Point” and click on “Restore” option.
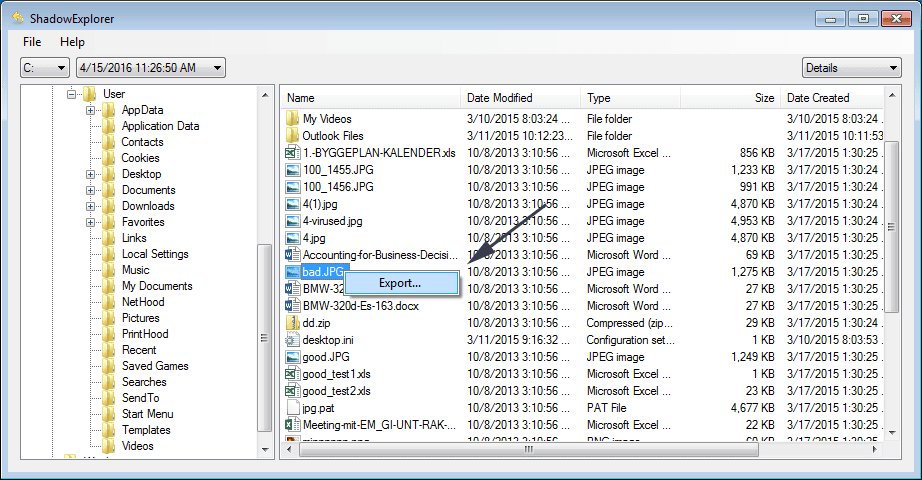
In order to access the files encrypted by Happy New Year Ransomware, you can also try using “Shadow Explorer”. In order to get more information on this application, press here.
Important: Data Encryption Ransomware are highly dangerous and it is always better that you take precautions to avoid its attack on your work-station. It is advised to use a powerful anti-malware tool in order to get protection in real-time. With this help of “SpyHunter”, “group policy objects” are implanted in the registries in order to block harmful infections like Happy New Year Ransomware.
Also, In Windows 10, you get a very unique feature called “Fall Creators Update” that offer “Controlled Folder Access” feature in order to block any kind of encryption to the files. With the help of this feature, any files stored in the locations such as “Documents”, “Pictures”, “Music”, “Videos”, “Favorites” and “Desktop” folders are safe by default.
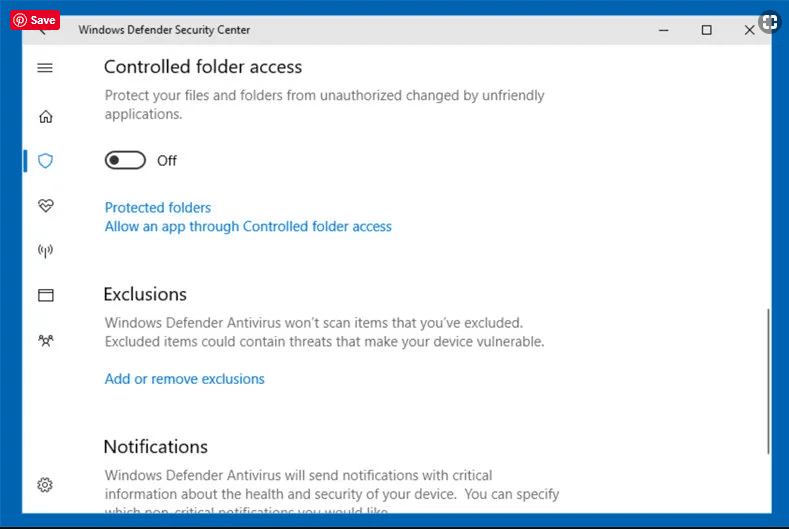
It is very important that you install this “Windows 10 Fall Creators Update” in your PC to protect your important files and data from ransomware encryption. The more information on how to get this update and add an additional protection form rnasomware attack has been discussed here.
How to Recover the Files Encrypted by Happy New Year Ransomware?
Till now, you would have understood that what had happed to your personal files that got encrypted and how you can remove the scripts and payloads associated with Happy New Year Ransomware in order to protect your personal files that has not been damaged or encrypted until now. In order to retrieve the locked files, the depth information related to “System Restore” and “Shadow Volume Copies” has already been discussed earlier. However, in case if you are still unable to access the encrypted files then you can try using a data recovery tool.
Use of Data Recovery Tool
This step is for all those victims who have already tries all the above mentioned process but didn’t find any solution. Also it is important that you are able to access the PC and can install any software. The data recovery tool works on the basis of System scanning and recovery algorithm. It searches the System partitions in order to locate the original files which were deleted, corrupted or damaged by the malware. Remember that you must not re-install the Windows OS otherwise the “previous” copies will get deleted permanently. You have to clean the work-station at first and remove Happy New Year Ransomware infection. Leave the locked files as it is and follow the steps mentioned below.
Step1: Download the software in the work-station by clicking on the “Download” button below.
Step2: Execute the installer by clicking on downloaded files.
Step3: A license agreement page appears on the screen. Click on “Accept” to agree with its terms and use. Follow the on-screen instruction as mentioned and click on “Finish” button.

Step4: Once the installation gets completed, the program gets executed automatically. In the newly opened interface, select the file types that you want to recover and click on “Next”.
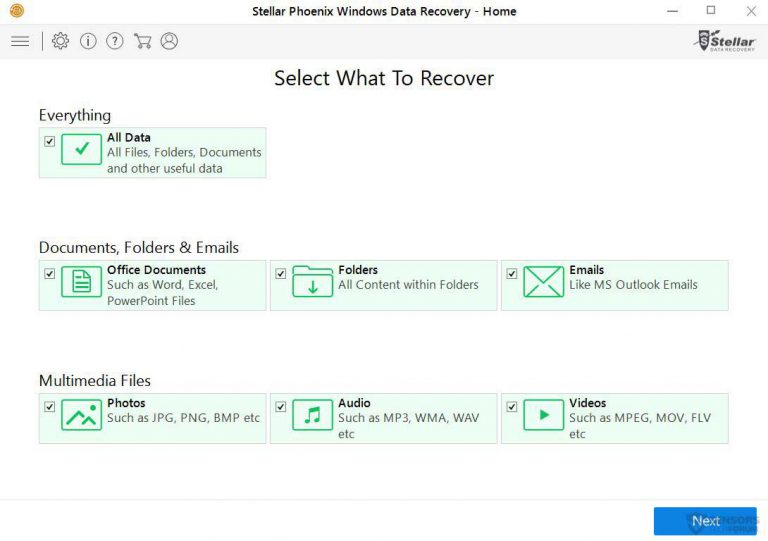
Step5: You can select the “Drives” on which you want the software to run and execute the recovery process. Next is to click on the “Scan” button.
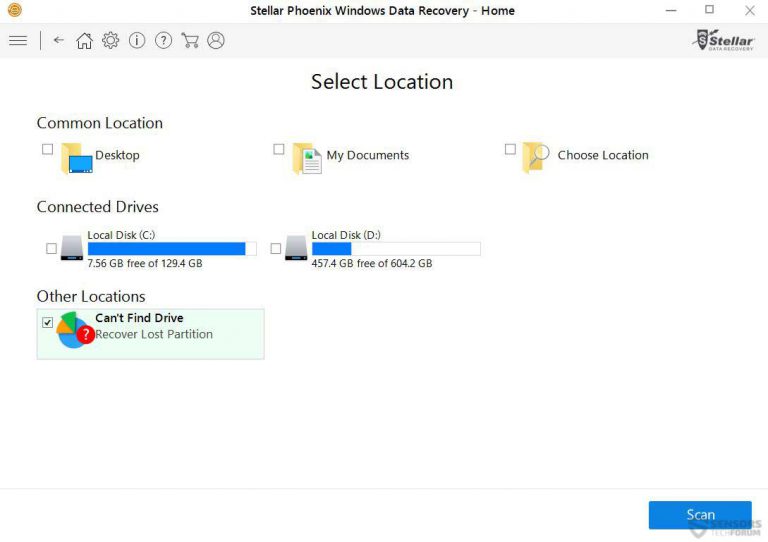
Step6: Based on drive you select for scanning, the restore process begins. The whole process may take time depending on the volume of the selected drive and number of files. Once the process gets completed, a data explorer appears on the screen with preview of that data that is to be recovered. Select the files that you want to restore.

Step7. Next is to locate the location where you want to saver the recovered files.

Special Offer (For Windows)
Happy New Year Ransomware can be creepy computer infection that may regain its presence again and again as it keeps its files hidden on computers. To accomplish a hassle free removal of this malware, we suggest you take a try with a powerful Spyhunter antimalware scanner to check if the program can help you getting rid of this virus.
Do make sure to read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter free scanner downloaded just scans and detect present threats from computers and can remove them as well once, however it requires you to wiat for next 48 hours. If you intend to remove detected therats instantly, then you will have to buy its licenses version that will activate the software fully.
Data Recovery Offer
We Suggest you to choose your lately created backup files in order to restore your encrypted files, however in case if you don’t have any such backups, you can try a data recovery tool to check if you can restore your lost data.